PyJFuzz is a small, extensible and ready-to-use framework used to fuzz JSON inputs , such as mobile endpoint REST API, JSON implementation, browsers, cli executable and much more. It is shipped with a built-in tool called PyJFuzz Web Fuzzer , this tool will provide an automatic fuzzing console via HTTP and HTTPS server, it can be used to easly fuzz almost any web browser even when you can’t control the process state!
There are two switch used to launch this tool (–browser-auto and –fuzz-web), the first one perform automatic browser restart when a crash occur, the other one try to catch when a browser doesn’t make requests anymore.
Requirement:
- Python
- PyJFuzz
- Linux system
Download and Install:
Download PyJFuzz and install its dependencies using the command given below. You can install if from automatic setup.py installtion.
git clone https://github.com/mseclab/PyJFuzz.git && cd PyJFuzz && sudo python setup.py install
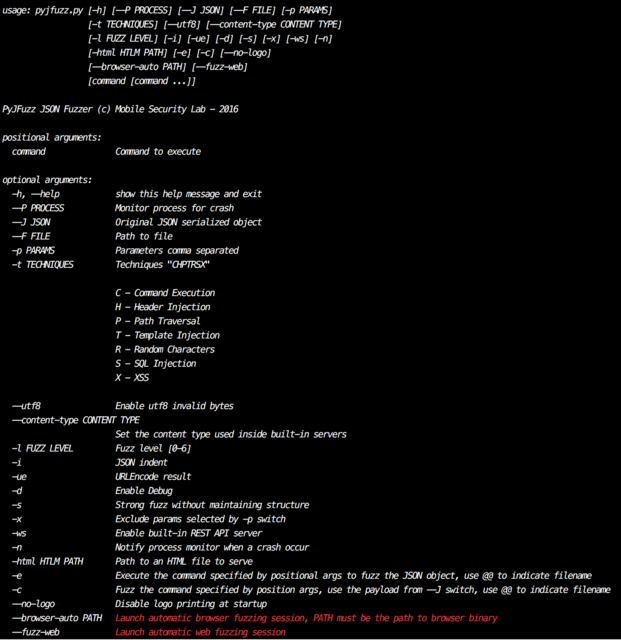
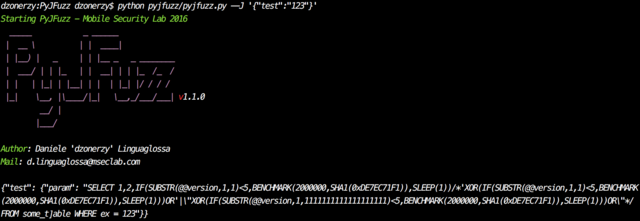
Once installed PyJFuzz will create both a python library and a command-line utility called pjf (screenshot below)
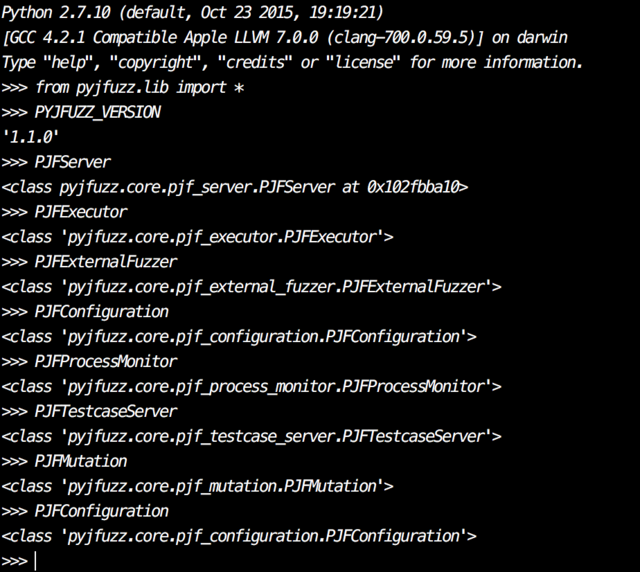
You can work as library in PyJFuzz, you can import it into your project by using the following command:
from pyjfuzz.lib import *
List of available object/class:
- PJFServer – User to start and stop built-in HTTP and HTTPS servers
- PJFProcessMonitor – Used to monitor process crash, it will automatically restart proccess each time it crash
- PJFTestcaseServer – The testcase server is used in conjunction with PJFProcessMonitor, whenever a process crash the testcase server will register and store the JSON which cause the crash
- PJFFactory – It’s the main object used to do the real fuzz of JSON objects
- PJFConfiguration – It’s the configuration file for each of the available objects
- PJFExternalFuzzer – Used by PJFactory is a auxiliary class which provide an interface to other command line fuzzer such as radamsa
- PJFMutation – Used by PJFFactory provide all the mutation used during fuzzing session
- PJFExecutor – Provides an interface to interact with external process
Note: When changing default ports, you should always handle exception due to needed privileges!