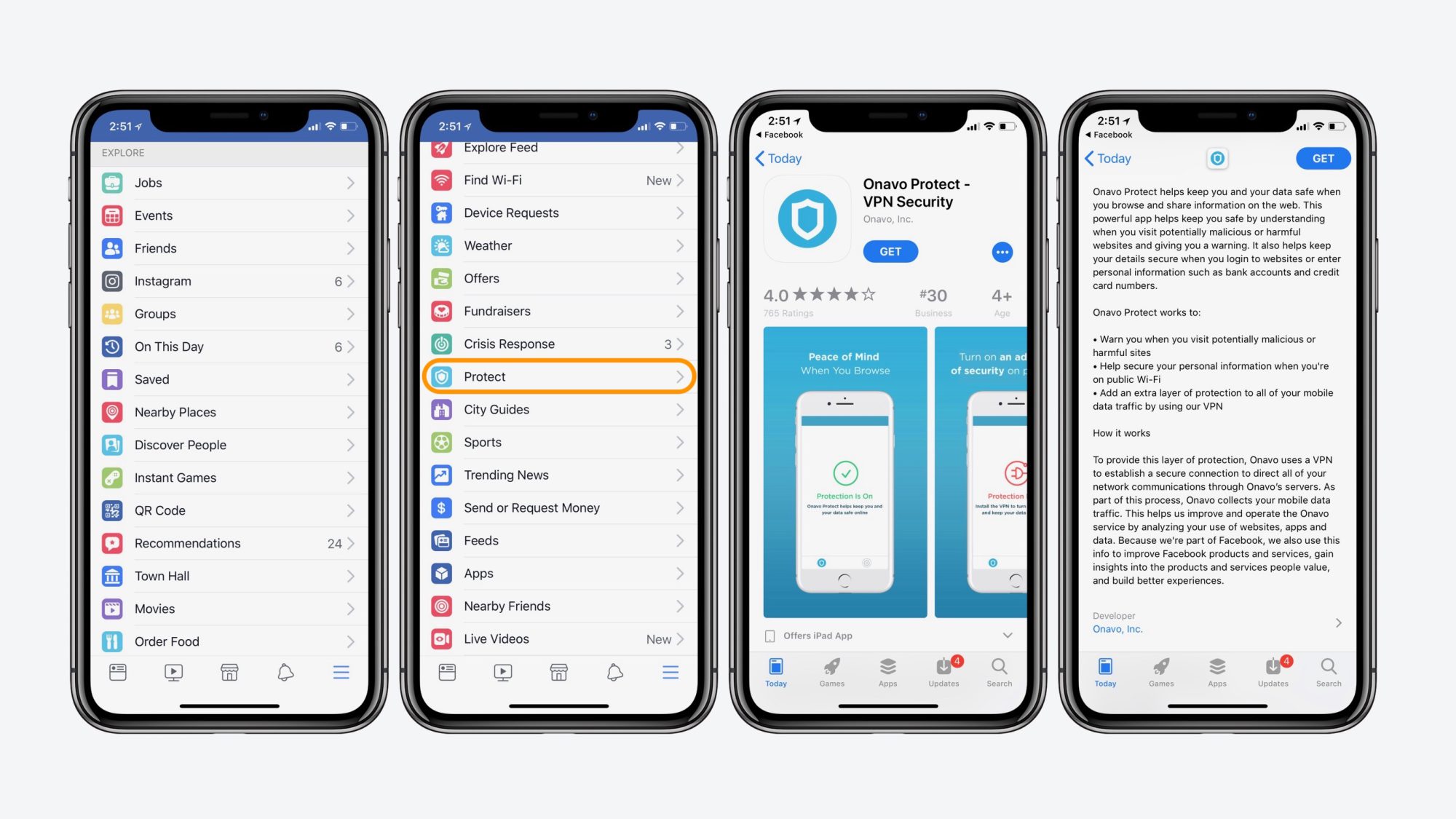
Facebook has launched its own Mobile VPN application called Onavo, the purpose of which is to protect the personal information of the users over public networks. However the application actually collects user data even when the application is disabled by the user.
On Monday, Will Strafach, CEO of the Sudo Security Group, wrote his findings of the data obtained by Onavo. The app uses a Packet Tunnel Provider app extension as part of Apple’s iOS SDK to handle the VPN’s network traffic routing.
The Following Data is being sent to Facebook:
- When the Mobile Data is turned on and off
- Daily WiFi usage (even when the application is turned off)
- Daily Cellular data usage (even when the application is turned off)
- Amount of VPN time used
- Location Data
- Log File of user
Strafach said that:
Onavo Protect will flush collected analytics information to log files from memory if there are greater than 49 “events” waiting in RAM or if it has been more than 2 minutes since the last flush.
The log files are then prepared for upload in a network request to Facebook. Analytics data is sent in a POST request to https://graph.facebook.com/v2.3/logging_client_events from the Packet Tunnel Provider process (The Packet Tunnel Provider process would be running at any time the VPN connection for Onavo is switched on, enabling periodic analytics data uploads to Facebook even if the Onavo Protect app is not open).
Facebook is even collecting the user’s screen time to know the user’s browsing habits, furthermore it even knows how long a user uses their mobile during the course of the day. The weird part is that the application is actually collecting the analytics even when the app is turned off.
Strafach said that Facebook should be clearer about what it’s doing with the data.
Take your time to comment on this article.
Source: The Register, Betanews