MoneyTaker, an infamous hacker group stole almost a million dollars from the PIR Bank in Russia after it breached the bank’s network via an unpatched router.
The victim lost around $920,000 in funds which were being kept in a corresponding Bank of Russia account
The Russian cybersecurity firm, Group-IB has been identified as the investigating firm, after examining the bank’s affected servers and workstations, they gathered “irrefutable digital evidence” that implicated MoneyTaker was indeed the culprit.
Group-IB publicized MoneyTaker’s existence back in December 2017 and published a report on the hacker group’s past activities.
MoneyTaker has been linked to thievery within UK, US and Russian financial institutions and banks dating back to 2016. According to Group-IB experts, MoneyTaker attacks on banks focus specifically on the infiltration of inter-banking card processing and funds transfer systems like Automated Work Station Client of the Russian Central Bank or AWS CBR and the First Data STAR Network.
The hackers infiltrated the network of PIR bank via one of its regional branch’s outdated routers back near the end of May.
Group-IB experts stated: “The router had tunnels that allowed the attackers to gain direct access to the bank’s local network. This technique is a characteristic of MoneyTaker. This scheme has already been used by this group at least three times while attacking banks with regional branch networks.”
MoneyTaker hackers then infected the financial institution’s local network with malware using that same router. PowerShell scripts were then used to acquire persistence and perform malicious operations, all while avoiding detection.
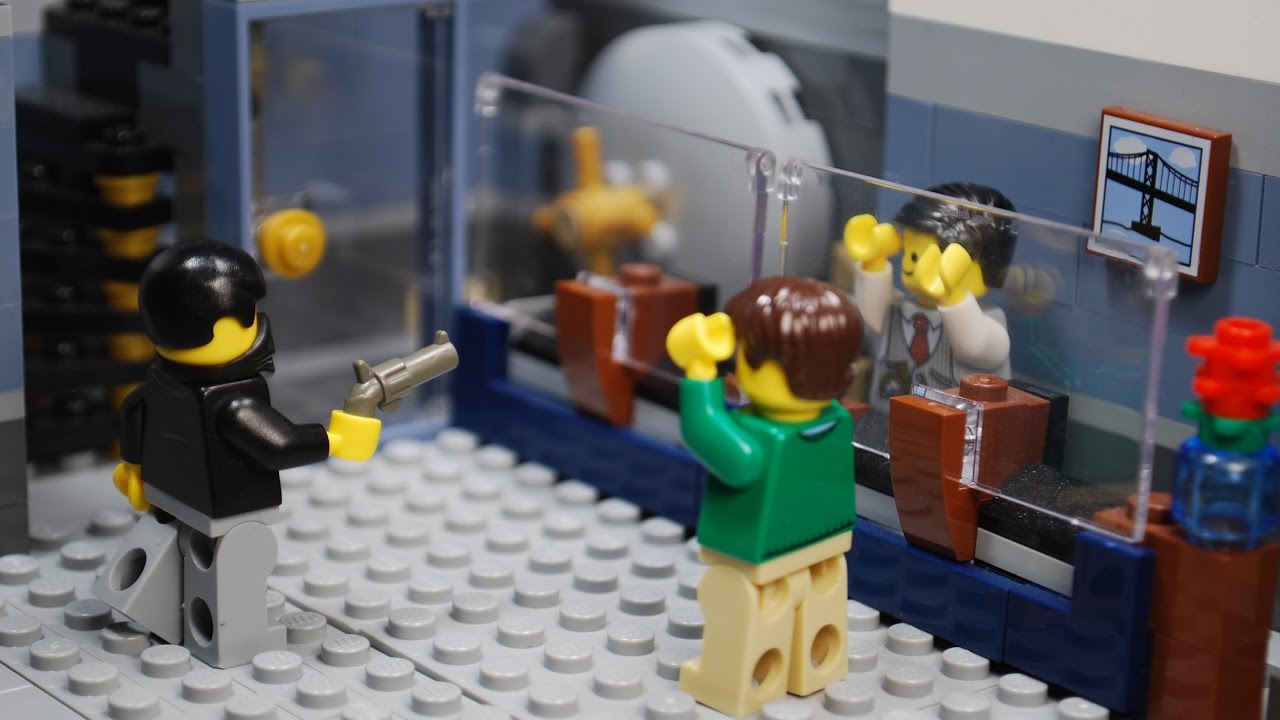
When MoneyTaker finally breached the institution’s main network, they also acquired access to the bank’s AWS CBR account which is the system they require in order to gain control of financial transactions.
Using this system, the hackers transferred money from the PIR Bank’s Bank of Russia account to 17 different accounts, ones they had created beforehand, and then money mules withdrew the funds from ATMs in Russia moments later.
The PIR Bank employees uncovered the hack the following day, July 4th, but it was already too late for the transactions to be reversed by then.
MoneyTaker tried to cover their tracks by clearing logs from computers they’d infected, but Group-IB claims they discovered reverse shells used by the hackers to access the compromised computers.
An exclusive insight has been provided to LHN from Ken Hosac, VP of IoT Strategy & Business Development at Cradlepoint:
“Software-defined Networking (SDN) enables IoT devices, such as routers, to be deployed on a completely separate network (virtually) that is invisible to the outside world. Traditional networks utilise a “connect first, authenticate second” model that allows hackers to scan networks for devices and their ports using common hacking tools. Those same hacking tools are then used to defeat the authentication. A key benefit of SDN is the model of “authenticate first, connect second”. These networks are completely invisible and inaccessible unless the organisation’s IoT devices are first properly authenticated. This means that it is much more difficult for routers to be exploited by hackers.”