An adware delivery ploy involving replica websites was uncovered by a French security researcher. These clone sites are essentially utilizing domain names that appear to be legitimate to fool unassuming victims into downloading popular apps that have been infected with adware.
Ivan Kwiatkowski uncovered the first batch of sites a few days ago, with the very first website being keepass.fr. The phony domain name was attempting to replicate the official site of the app which was actually: keepass.info.
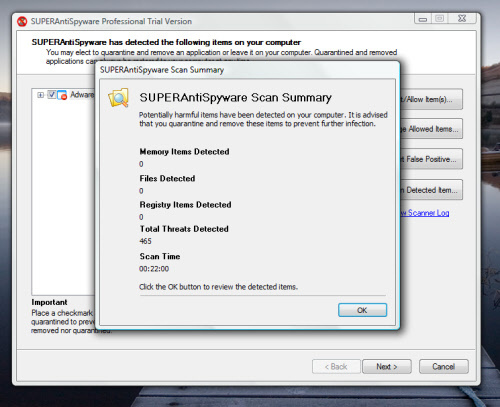
The Keepass password manager app downloaded from the clone site contains a valid, fully-functional version; however, it has also been infected with InstallCore adware.
InstallCore is a kind of adware that bundles free software along with 3rd-party offers included as part of that app’s installation procedure. Every time one of those additional programs is successfully installed the bundler of that adware is paid a commission fee.
While some of the “offers” happen to be legitimate apps, these kinds of software bundles are also widely known to be “pushers” of more malicious apps and have, in the past, pushed search hijackers, cyptocurrency miners, adware, and tab hijackers, just to name a few.
Once the offers are either accepted or declined and then installed by the user, the bundler also installs the free app that the user was attempting to download in the first place.
The Keepass.fr site wasn’t the only clone website, either. It was actually found to be part of a much bigger collection of typosquatted domains, all of which had been registered with the exact same email address.
Audacity, 7Zip, Inkscape, Paint.net, Truecrypt, Scribus, Celestia, GParted, Blender, Filezilla, and Adblock were just some of the popular software applications that this individual or group tried to replicate with the clone registered domain names.
Many of the domains had been registered using .es or .fr and the sites’ content was in either Spanish or French. This info suggested that whoever was behind these fake websites was attempting to push the adware-infected apps only to users who spoke either Spanish or French. A small number of the phony sites were available in English and utilizing international TLDs, as well.
Kwiatkowski said that all of the sites appeared to have been hosted on the exact same server and this made shutting down the whole operation relatively easy.
Anytime you download software, even if you’re downloading it from the official website, it is always a good idea to check the download with sites such as virus total.
Please leave any comments in this article below.