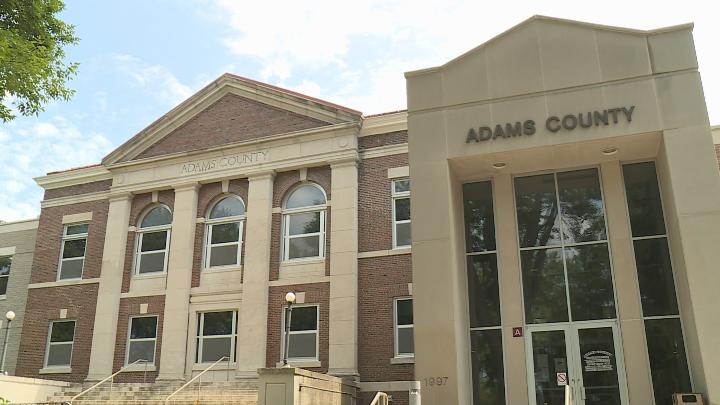
Once again, a massive cyber attack on a government’s computer has affected thousands of citizens. Reportedly, the data of more than 250,000 people got exposed as a result of a data breach in Adams County,Wisconsin. The breach has lasted for around six years and reportedly has also affected a top county official.
Adams County, WIS Data Breach Affected 250,000 People
On Friday, Adams County officials released a media statement and a detailed notification regarding a security breach. The officials confirmed the exposure of the details of 258,120 individuals in the Adams County data breach. The investigations revealed that the breach lasted for around six years – that is, from January 2013 to March 2018.
Allegedly, the incident happened as a result of unauthorized access to the County’s computer system and network discovered on March 28, 2018. After noticing the matter, the officials continued with the investigations and received a comprehensive forensic report on June 29, 2018. The breached data includes explicit details of the individuals including “Personal Identification Information (PII), Personal Health Information (PHI), and/or Tax Intercept Information (TII)” stored with the following six departments of their Adams County website: Veteran Service Office, County Employees, Extension Office, Solid Waste, Child Support, Health and Human Services, and Sheriff’s Office.
As stated in their media statement,
“There is evidence that there was unauthorized access of this information and/or unauthorized acquisition of this information. Unauthorized individual(s) obtained rights, users names and passwords by manipulation of certain software programs on the Adams County computer network and system that allowed them access to environments that were beyond their role and/or department.”
A County Clerk Suspected In The Incident
In the media statement, Adams County hinted towards the identification of suspects. Yet, they did not disclose or pinpoint any specific individuals. Rather they simply confirm that the suspect no longer has any access to their system.
“Suspect(s) have been identified during the course of the investigation. The suspect(s) no longer have any access rights to view the entirety of the Adams County computer network and system. Further steps were taken to remedy the unauthorized access and there is limited access to the Adams County computer system and network. The suspect(s) accounts have been suspended and the suspect(s) no longer have access to the system. All software control measures manipulated during the operative time period have been disabled. Access to control and/or authorize access to the involved departments has been restricted and placed in the control of one designated individual.”
Nonetheless, further reports hint towards a County clerk as the suspect. Reportedly, a special agent from the Wisconsin Department of Justice detained the laptop of a Cindy Phillippi, a County Clerk, upon the receipt of an approved search warrant. According to the search warrant, Phillippi used a keylogger to gain access to the other computers. However, for now, no arrests or criminal charge lodge has taken place.
So another Government breach but this time the culprit is believed to be not an outside hacker but a rogue employee, what their intentions were though remain to be seen – let us know what you think in the comments section.