Net Creds is a free tool that sniffs passwords and hashes from a network interface. The tool launches a MITM attack to capture network packets, and ultimately the login credentials. The MITM attack works for the protocols that send credentials in clear text. The example protocols include HTTP, TELNET, POP, SNMP, IMAP, and NNTP. These protocols are vulnerable to MITM attack since they share the password in an unencrypted format. Net Creds is capable of sniffing the network requests based on similar protocols, such as HTTP searches, HTTP form logins, HTTP basic authentication, POP logins, IRC logins, FRP logins, SMTP logins, IRC logins, IMAP logins, and all supported protocols of NTLM version 1 and version2.
Installing Net Creds
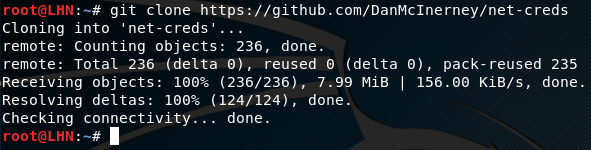
Net Creds is python based tool that requires scapy and wsgiref library to work. Net Creds runs on Linux as well as Windows OS. Linux (Kali) has built-in Python package, however, for Windows installation, a python compiler is recommended to run the script. The tool can be downloaded from github repository using the following command.
git clone https://github.com/DanMcInerney/net-creds
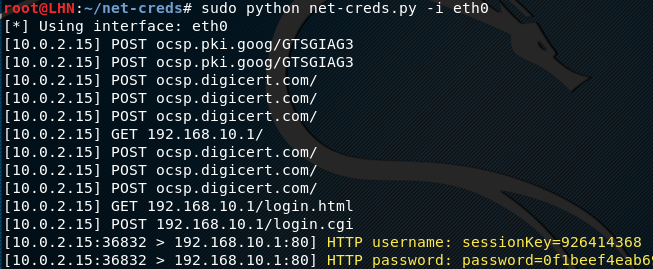
Sniffing via Net Creds
Net Creds is capable of sniffing the credentials from an interface as well as pcap file. In order to automatically detect the available interface, run the following command in the OS terminal.
sudo python net-creds.py
In our case, the tool detected ‘eth0’ as the available network interface. The following command can be used to start sniffing on the available interface i-e ‘eth0’.
sudo python net-creds.py -i eth0
To test the working of the tool, let’s open an example web application running on the HTTP protocol. We have also logged into the web application to see if the login credentials are captured by Net Creds. Once the web application is launched in the browser, the tool starts capturing the packets and login credentials as shown in the following screenshot.
The packets from a specific IP address can be ignored using the following command.
sudo python net-creds.py -f <ip address here>
Similarly, the following command can be used to read the packets from a pcap file.
python net-creds.py -p pcapfile
What Bunny rating does it get?
Net Creds is easy to install and use. The tool is capable of capturing packets and unencrypted passwords from well-known network protocols. Nowadays the majority of the network services use ample encryption technique to share password credentials. Similarly, most web applications are running over HTTPS. The tool should be updated to include potential mitigations such as SSLstrip. As a result we will be rating this tool 3 out of 5 bunnies.



Want to learn more about ethical hacking?
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.