A2SV is an open source tool used for scanning SSL vulnerabilities in web applications. A2SV performs vulnerability scanning for CCS injection, Heartbleed, Logjam, Freak Attack, Anonymous Cipher, SSL v3 POODLE, SSL v2 Drown, and Crime (SPDY). CCS is the OpenSSL vulnerability that acts as Man in the Middle (MITM) to intercept network traffic and eavesdrop on communications through access to the SSL handshake.
A2SV Installation
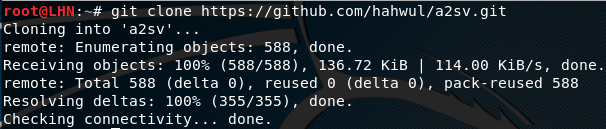
A2SV can be installed by cloning the tool from Github repository using the following command.
git clone https://github.com/hahwul/a2sv.git
The next step, after cloning the tool, is to install the OpenSSL and the python packages as follows.
cd a2sv pip install argparse pip install netaddr apt-get install openssl
How A2SV Works
After installing the tool, run A2Sv from the terminal using the following command.
python a2sv.py
A2SV comes with the following modules to test the target web application for the SSL/TLS vulnerabilities.
Anonymous:For detecting Anonymous Cipher
crime:T detect Crime(SPDY) vulnerability
heart: To find out HeartBleed vulnerability
ccs:Tracking the CCS Injection possibilities
poodle: To look for SSLv3 POODLE
freak: Identifying the FREAK Attack
logjam: To test application for LOGJAM vulnerability
drown: to look for SSLv2 DROWN issues
By default, A2SV runs all these modules to find the SSL vulnerabilities in the target web application. However, we can exclude any modules to limit the search process.
In order to test the target web application, we can use the domain name or IP address of the target application. The following command is used to test the target application for SSL vulnerabilities.
python a2sv.py -t <target web address or IP address>
The command runs all the modules one by one to test the application for the SSL vulnerabilities.
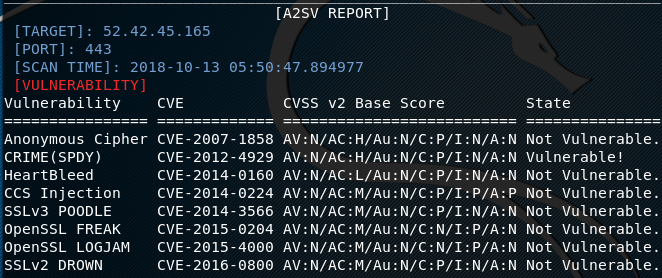
The results displayed at the end of scanning process can be stored in a text file using the following command.
-o /home/yourdir/result.txt
Similarly, in order to run any specific module from the abovementioned list, use the –m flag along with the module name as shown in the following command.
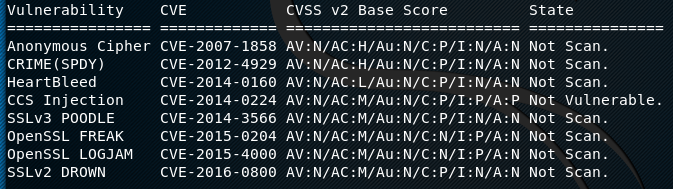
python a2sv.py -t <target IP address> -m <module name>
For example, if we want to test only the CCS injection vulnerability in the target web application, we can direct the tool using the following command.
python a2sv.py -t <target web address or IP address> -m ccs
In this case, the results are displayed in the following format.
What Bunny rating does it get?
A2SV is a nice little tool that can perform the well-known SSL vulnerabilities scanning test without much effort, not sure if it is ready to replace some of the other big names such as SSLScan or SSLyze. As a result we will be awarding this tool a rating of 3.5 out of 5 bunnies.



![]()
Want to learn more about ethical hacking?
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.