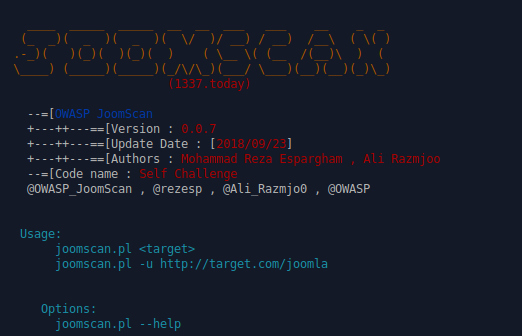
Joomscan is a scanner by OWASP, which aims to automate the task for vulnerability assessments for Joomla based sites. Based in perl, this tool can enumerate the version, vulnerabilities, components, firewalls and more, all in one friendly to use interface.
Installing Joomscan
First, let’s clone the repository to our machine.
git clone https://github.com/rezasp/joomscan.git
All the components are set, if you have perl already installed in your machine you are good to go.
Running Joomscan
Joomscan scanner is pretty easy to use, just type the target and it will automate all the tasks for you.
cd joomscan/ perl joomscan.pl
Let’s try it against a target which is running Joomla to see what results we get. Also we will enumerate all the components with the ‘-ec‘ option. Give it some time to list you all the data.
peri joomlscan.pl -u <target> -ec
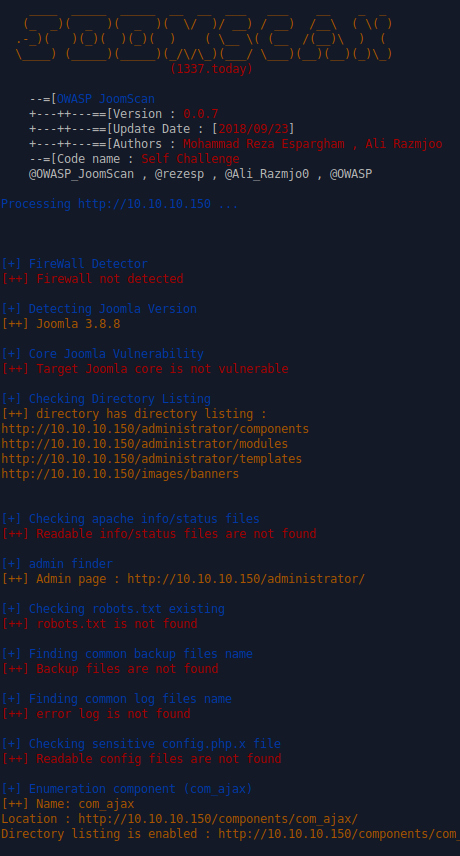
Some of the info we got is that the CMS is not behind a firewall. Also we got some administrator directories, which it might be helpful later. We got a big list of all the components too. The final report is also saved to check it later.
What Bunny Rating does it get?
Joomscan is making the vulnerability assessment process of Joomla sites, pretty easy and effortless. The interface is simple and you get a vast variety of information you can use to exploit your target. However, you should not be based to a single tool for you assessment. This tool, gets 3.5 out of 5 bunnies.




Want to learn more about ethical hacking?
We have a networking hacking course that is of a similar level to OSCP, get an exclusive discount here
Help support LHN by buying a T-shirt or a mug?
Check out our selection here
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.
