Winpayloads is a python based tool which combines some of the Powershell Empire features along with the metasploit framework to create windows payloads. It is simple to use and has some interesting options to choose between.
Installing Winpayloads
First, let’s clone the repository from Github.
git clone https://github.com/nccgroup/Winpayloads.git
After that go to the directory and run the setup script.
cd Winpayloads/ ./setup.py
That’s it.
Running Winpayloads
To run Winpayloads just type this in your shell.
python Winpayloads.py
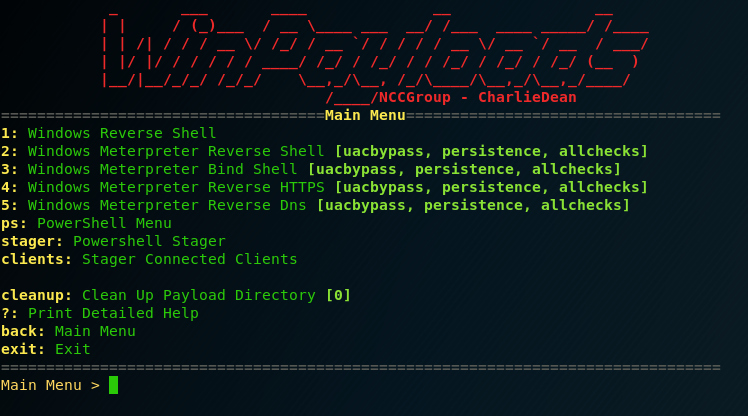
The interface shows us 5 different payloads we can use. They are created with the help of Powershell Empire and they have some interesting features, such as bypassing UAC and persistence. In our example we assume that we have already access to a Windows machine.
So, the first thing we wanna do is to create a stager, which opens a connection with a basic powershell shell. Type ‘stager‘ in your console and then ‘r‘ to create a remote connection. Then run the payload inside your target’s machine.

The connection is opened. Now we need to create a persistence, fully functioning payload. Choose one between the five options. In our example we will use option number ‘2‘ which is a meterpreter reverse tcp shell.

Change the options to fit yours and then choose to upload the .exe file that you just created with the client connection you’ve opened before. In our example, we type ‘1‘ to send the payload to our client.
After that, a metasploit console opens. Give it some time to run (around 20 seconds) and eventually the meterpreter session will open on your machine.

What Bunny rating does t get?
Winpayloads automates the process of payload creation for windows. That’s it – nothing more, nothing less. It has some interesting features and it’s simple to use. However the payloads are not undetectable from common AV solutions. For that I’m giving it 3 out of 5 bunnies.



Want to learn more about ethical hacking?
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.
