Managing fake news is a problem troubling most tech giants. While fake news has already troubled Facebook, the next victim of this problem seemed Google! All it took for a malefactor to spread wrong information was to exploit a vulnerability targeting Google search results. As a result, Google search would begin displaying incorrect results to the search query.
The Vulnerability Threatened The Credibility Of Google Search Results
A researcher has shared some interesting findings about how it was possible to manipulate Google. It would perhaps disappoint Google fans that one of the most trusted search engines by the public was vulnerable to manipulation. Any bad actor could meddle with Google search results to spread wrong information – precisely, fake news. As reported, an attacker merely had to exploit the “knowledge graph” feature for it.
What Is Knowledge Graph?
It is a unique feature launched in 2012 that displays key information on the first page of Google search results. In specific and simple words, it is that box of information displayed on one side of your screen along with search results.
Google added this feature to facilitate users to get the desired information as it displays all the key details that you might look for. However, this useful feature might also misguide the users if exploited by a criminal hacker.
Spoofing Google Search Results
The researcher Wietze Beukem shared details about the vulnerability in detail in his blog post. According to his findings, the problem existed because of a specific parameter contained in the knowledge graph that acted as its “unique identifier”. Anyone could extract that parameter from the knowledge graph URL and link it to a valid search URL. The result would show the desired knowledge graph with the search query. Then, spreading or sharing this link with others would certainly make people believe the wrong information.
As explained by Beukem,
“If you click on the share button – present on every card – you’ll be given a shortened link (a https://g.co/ address). Following this link will redirect you back to google.com with the original search query. What’s different however are the parameters used: the URL will contain a &kgmid parameter… As it turns out, you can add this parameter to any valid Google Search URL, and it will show you the Knowledge Graph card next to the search results of the search query.”
In addition, another parameter “knponly” allowed creating a search result that would only display the desired knowledge graph as a response to a search query.
While writing this article, we thought to give this trick a try – and see what LHN got. Google showed Alibaba Group somehow relates to Donald Trump.

Image: LatestHackingNews
Or this.
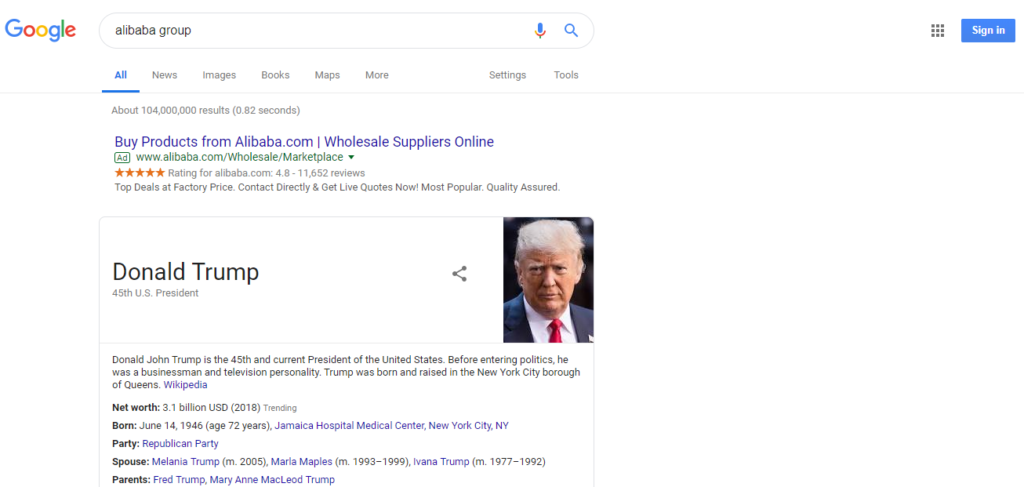
Image: LatestHackingNews
What if we say Trump owns Alibaba? Would you believe it? Well, that’s what it showed upon searching “Alibaba group”. So, this is how anyone could be spoof search results displayed against a query.
Google Fixed The Matter
While the vulnerability did not have a devastating impact on Google, it could have certainly impacted the credibility of Google search results. The average user blindly trusts what Google displays. In fact, many times, people do not even bother to scroll down to see other search results if they get their desired information from the knowledge graph. That’s what made this glitch dangerous. The manipulated URL looked legit, had ‘https’ and could be shared with anyone by any means. Thus, it merely required a few seconds for anyone to spread misinformation among the masses.
Sharing a possible fix for the problem, the researcher recommended,
“To prevent people from abusing Knowledge Graph, the disabling of the kponly parameter by Google would definitely help (when would you ever just want to see a card without further context?), although in my opinion removing the kgmid option altogether would be even better.”
Ironically, Google didn’t deem this problem as important. According to the researcher, he reported this problem to Google about a year ago. However, his bug report was closed without deeming the reported matter a “vulnerability”.
Nonetheless, Google has now fixed this vulnerability. Though we took the screenshots while exploiting this trick on January 10, 2019, the links no longer work. You will now see the genuine results for the search query even after clicking on the manipulated links. Seemingly, Google rectified this option somewhere between January 10 and 11, 2019. It’s great they fixed this problem. Yet, nobody knows if the vulnerability was already exploited earlier.

