Google Play Store for Android users seems flooded with suspicious apps. In previous months, we reported several occurrences of Google removing apps from the Play Store. Such apps either induced malware infections on target devices or misused the data obtained from users. Although Google has been fighting to eliminate such apps from the Play Store, the problem still persists. Recently, a researcher has analyzed various Android VPN apps only to find how they demand unnecessary access to users’ device.
Android VPN Apps Seeking Unnecessary Permissions
John Mason from TheBestVPN has published a report about Android VPN apps. He analyzed multiple VPN apps existing on the Google Play Store and made worrisome findings. As per his observations, many of these apps request unnecessary access to the users’ device.
According to the report, he found many VPN apps demanding dangerous permissions. In other words, these apps seek explicit access to the device that interferes with users’ privacy. Ideally, a VPN must not ask for such permissions. As stated by Mason,
“As a VPN user, you want your VPN to not ask any kind of dangerous permissions that are not needed for the VPN app to function or which can compromise your privacy.”
Some of the dangerous permissions required by apps include access to read from and write to external storage, device’s contacts, cellular network information, location, and permission to use mobile data or WiFi.
In the study reported by Mason, 81 VPN apps were analyzed to know the permissions these apps require. The results obtained varied greatly for the apps, but most of them required unnecessary permissions.
“Many of the VPN apps reviewed in this study ask for permissions that are not needed for a VPN to function. Some permissions are fairly harmless… However, others are more suspicious.”
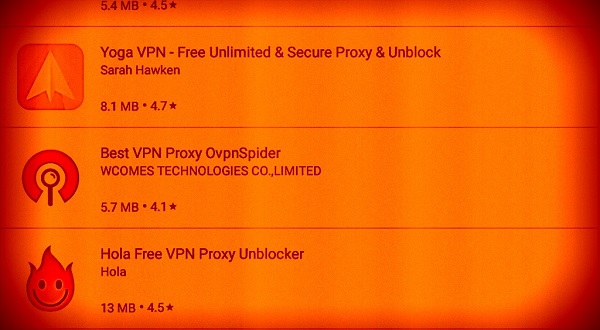
Summing up the findings, the study revealed that 50 out of the 81 tested apps seek at least one unnecessary permission. Whereas, the apps appearing most dangerous from the list include Yoga VPN (6 suspicious permissions), ProXPN and Dash VPN (both requiring 5 suspicious permissions). Besides, Seed 4 Me, oVPNSpider, SwitchVPN, Hola, and Zoog VPN also made it to the list requiring 4 suspicious permissions. The complete list of all the tested VPN apps is available in Mason’s report.
What Should You Do?
In a time when cybersecurity issues are on a rise, the use of VPN is always recommended. But that doesn’t mean that every VPN is safe to use. Certainly, it is highly likely that a bad actor exploits VPN to target users. The malicious purposes these apps serve include everything from dropping malware to spying and data exfiltration. In fact, we have just reported a few days ago how Facebook exploited its Onavo VPN app for collecting users’ data.
So, in such a situation, users need to stay cautious while choosing VPN apps. Perhaps, they should opt for the more reputed brands to avoid becoming prey to any malicious activity.