Cloakify Factory is a tool to transforms any file type into a list of harmless and even useless looking strings. This ability allows for you to hide a data file in plain sight and also transfer it over the network without triggering malware alerts. The functionality which Claokify utilizes is called text-based steganography that protects the data by making it look benign.
The cloaked files defeat signature-based malware detection tools, DLP, etc. In this demonstration, we will be working on Kali Linux.
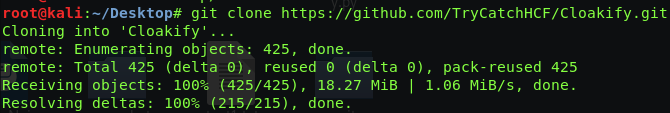
Downloading Cloakify
It can be downloaded in the Kali Linux with the following command;
git clone https://github.com/TryCatchHCF/Cloakify.git
Once the download completes, make sure you have python2.7 installed as it is a pre-requisite for running it. You need to navigate to its downloaded directory to run it;
Running Cloakify
Let’s run the tool by the following command;
python cloakifyFactory.py
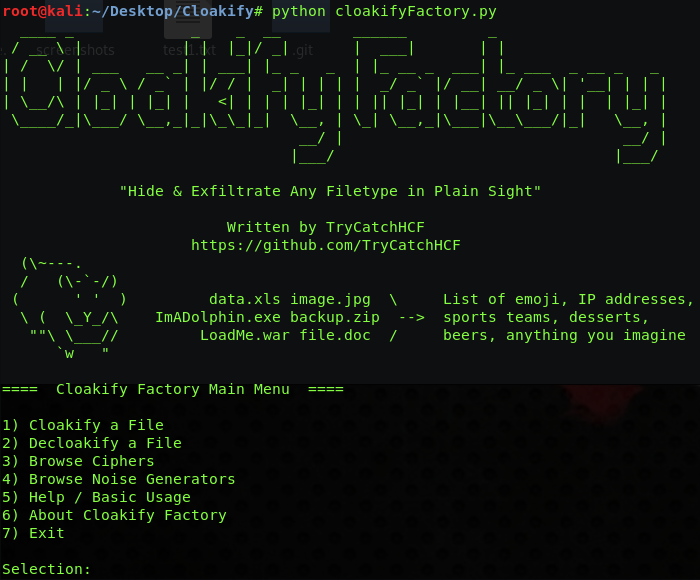
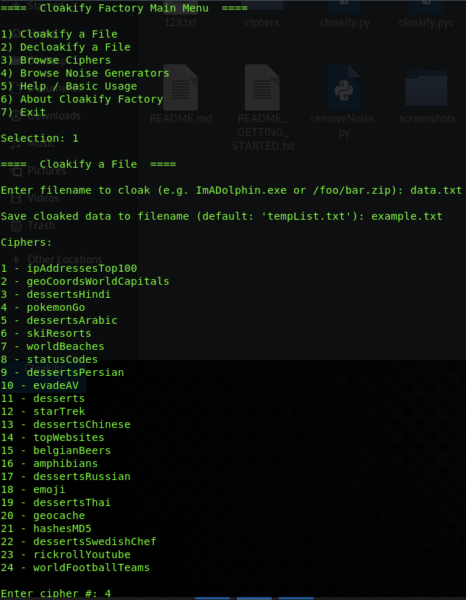
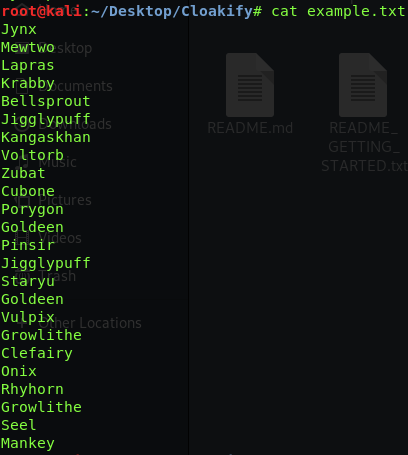
So as it seems that Cloakify Factory has a menu-driven tool that leverages its script set. When you choose a file to Cloakify, it first converts it into theBase64-encode, then applies a ciphertext to generate a list that encodes the Base64 payload. And then the cloaked data can be transferred to your desired destination. Let’s start cloakifying it the file which contains by data which you can see below;
![]()
Now I will encode this data.
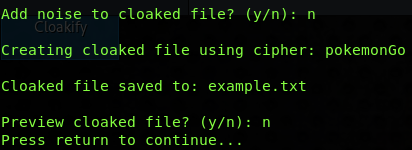
Now as the data is encoded, I will check for my output data file which was processed by Cloakify;
As data is encoded, so now it as exfiltrated, choose Decloakify with the same cipher to decode the payload.
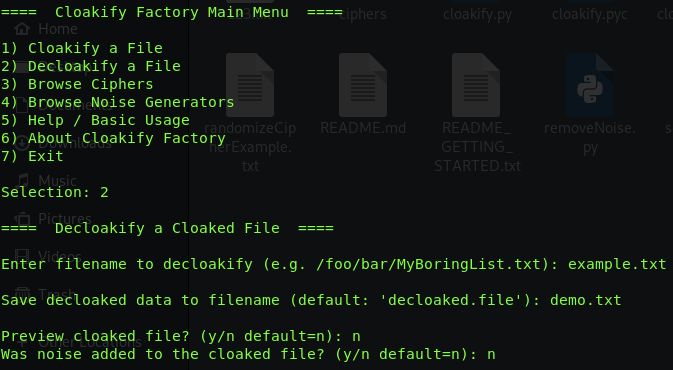
Now check for the data, if it reverted to the original state or not.
![]()
It worked successfully, as all the data get converted back to the actual state.
What Bunny rating does it get?
Cloakify is an excellent tool to pass the data from the network without being detected and triggering alarms. Both blue and red team activities can use it. I am giving it 4.5 out of 5 bunnies.




![]()
Want to learn more about ethical hacking?
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.

