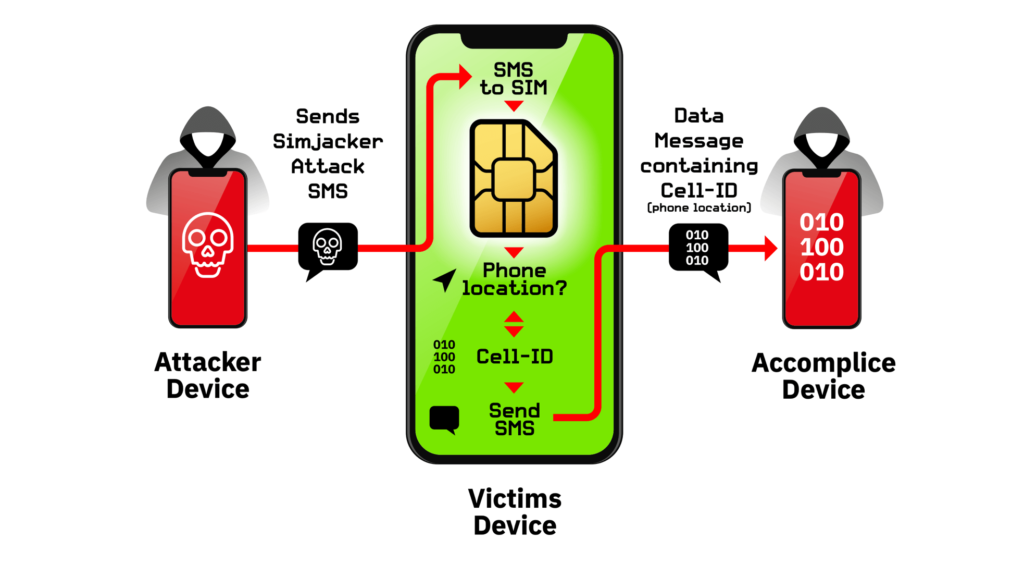
In the murky realm of hacking and jacking, cybercriminals are now using a primitive method for attacking users. Reportedly, researchers have found the Simjacker attack actively targeting various phones. The attack involves exploiting users’ SIM cards by sending malicious SMS messages.
The Notorious Simjacker Attack
Researchers from AdaptiveMobile Security have found a vulnerability that exploits SIM cards to takeover phones. Termed Simjacker, the attack begins when an adversary triggers the bug by sending malicious messages. The researchers have shared a detailed blog post about the attack. They have also set up a dedicated webpage for Simjacker.
Elaborating on the attack, the researchers stated that the attack involves the exploitation of the SIM Card (UICC) component ‘S@T Browser’. By sending a maliciously crafted SMS, an attacker can trigger this component to let the SIM takeover the target device. As stated by the researchers,
The attack exploits the presence of a particular piece of software, called the S@T Browser – that is on the UICC. Once the Simjacker Attack Message is received by the UICC, it uses the S@T Browser library as an execution environment on the UICC, where it can trigger logic on the handset.
The attacker can then retrieve sensitive details from the device, such as IMEI and location, via another SMS by triggering the same logic. Whereas, the victim remains unaware of all this process during the attack.
Source: AdaptiveMobile Security
Following the initial steps, the attackers can further expand the scope of the attack to retrieve other data and perform further commands. The researchers are going to present more details about Simjacker at the upcoming Virus Bulletin Conference (VB2019) scheduled for October 2 to 4, 2019, in London.
Active Exploitation Discovered
According to researchers, the Simjacker attack is already under active exploitation. Presently, they have found the attack to be coming from a limited origin, which collaborates with governments for monitoring individuals.
The probability of further exploitation never diminishes. The researchers believe that the attack threatens over 1 billion users. Essentially, all mobile phones with SIM cards are vulnerable to Simjacker.
Nonetheless, the researchers confirm that they have communicated the vulnerability to the GSM Association, and the SIM alliance. These entities have taken a number of steps to address the problem.
The researchers also urge the mobile operators to block any suspicious messages potentially triggering S@T Browser.
Let us know your thoughts in the comments.

