A few years ago, we previously heard of DolphinAttack targeting voice assistants to hack smartphones and other devices. Now, researchers have come up with another strategy to take over smartphones, the ‘SurfingAttack’. As discovered, SurfingAttack controls voice assistants by exploiting ultrasonic waves, to take control of the device.
SurfingAttack Via Ultrasonic Waves
A team of researchers has recently elaborated on SurfingAttack – a tactic to hack devices via voice assistants. This attack leverages ultrasonic waves to send commands to voice assistants.
Brief, in their study, the researchers minimized the limitations of transmittance of ultrasonic radiations to target a certain device. While the previously reported attack methods similar to this one, such as the DolphinAttack, involved over-the-air transmission of radiations, SurfingAttack transmits ultrasound waves via material surfaces, such as tabletops. This approach makes the attack possible over large distances and in any direction without necessarily requiring the target device to be in line-of-sight.
Conducting such attacks allows an adversary to steal sensitive details from the target devices, such as smartphones or tablets. The attacker can send inaudible voice commands in ultrasound waves to the device, minimize the device volume, and then capture the information leaked by the voice assistant. The entire attack would continue without attracting the victim user’s attention.
Attack Scenario
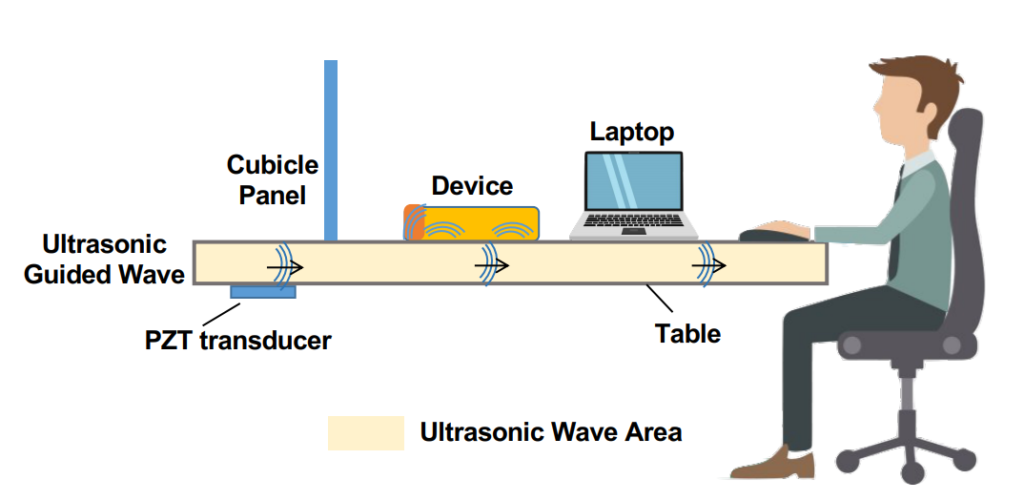
To validate their findings, the researchers set up a prototype of the attack device with a low-cost PZT transducer. Hiding this attack equipment near the target device and generating guided waves allowed the researchers to send voice commands to the target device’s voice assistants. After waking up the voice assistant, such as Google Assistant or Siri, they could then carry out various activities, including stealing of information.
The following picture shows a possible SurfingAttack setup.
Source: NDSS Symposium 2020
They tested 17 different smartphones and 4 tablets, among which, they successfully conducted SurfingAttack on 15 smartphones and 3 tablets. Specifically, the tested models included Google Pixel, Pixel 2 and 3, Motorolla G5 and Z4, Samsung Galaxy S7 and S9, Xiaomi Mi 5, Mi 8, and Mi 8 Lite, Huawei Honor View 10, and Apple’s iPhone 5, 5S, 6+, and iPhone X. Whereas, the evaluated operating systems included Android 7.0, 8.0, 9.0 and 10.0, and iOS 10.0.03, iOS 11, iOS 12.1.2, and iOS 12.4.1.
Their attack setup included different surface materials such as aluminum/steel, glass, and medium-density fiberboard (MDF). For the former two surfaces, they also evaluated the results against different thicknesses.
The following video quickly demonstrates how attackers can exploit target devices by conducting SurfingAttack.
The detailed strategy of conducting such attacks is available in the researchers’ paper. Whereas, they have also set up a dedicated website where they have shared videos demonstrating various attack scenarios.
How To Prevent SurfingAttack?
While SurfingAttack is hard to detect by an average user, researchers have advised various mitigations to prevent such attacks. These include,
- Minimizing the touch surface area between the phone and the table by using thick phone cases.
- Placing devices on soft woven fabric instead of direct surfaces.
- Disabling voice assistants on the lock screen and locking the device before putting on a surface.
- Never leave the device unattended.
- Disabling lock-screen personal results or unlock with voice match feature on Android.
Recently, researchers also demonstrated LightCommands attack exploiting voice assistants to hack smartphones, smart devices, and others. This attack involved the use of laser light to inject voice commands by exploiting a vulnerability in MEMS (microelectromechanical systems).
Let us know your thoughts in the comments.

