Researchers from VPNPro have discovered multiple vulnerabilities in many of the Top Free Android VPN apps. The most critical of all is the SuperVPN app that has the most extensive userbase too. The app boasts over 100,000,000 installs on Google Play Store, thus putting the security of 100 million users at risk.
Elaborating on their findings in a blog post, the researchers stated that SuperVPN Free VPN Client app bears multiple critical vulnerabilities. Exploiting these vulnerabilities triggers MiTM attacks, thus exposing the data transmitted over the VPN to the attackers.
Highlighting the possible consequences and risks to the users of SuperVPN Free VPN Client, the researchers state,
More than 105 million people could right now be having their credit card details stolen, their private photos and videos leaked or sold online, every single minute of their private conversations recorded and sent to a server in a secret location. They could be browsing a fake, malicious website set up by the hacker and aided by these dangerous VPN apps.
Additionally according to researchers the app mentions SuperSoftTech – a Singaporean company (as it poses) – as the developer, whereas it actually belongs to an independent Chinese developer Jinrong Zheng.
While going through the app details, LHN noticed that its Privacy Policy hints towards Tutela Technologies . Tutela (as they claim) facilitates the mobile and wireless industry in improving networks by collecting data from “millions of mobile devices”. They clearly mentioned in their Privacy Charter that their software runs at the back of various apps for collecting data (excluding personal details).
Other Vulnerable Free Android VPN Apps
Alongside SuperVPN Free VPN Client, the researchers also found 9 other VPN apps exhibiting one or more vulnerabilities. Regarding their flaws, the researchers briefly stated,
2 apps use hard-coded cryptographic keys, and 10 apps are missing encryption of sensitive data. 2 of these apps suffer from both vulnerabilities… Some apps have their encryption keys hard-coded within the app.
Below is the list of all risky apps the researchers analyzed.
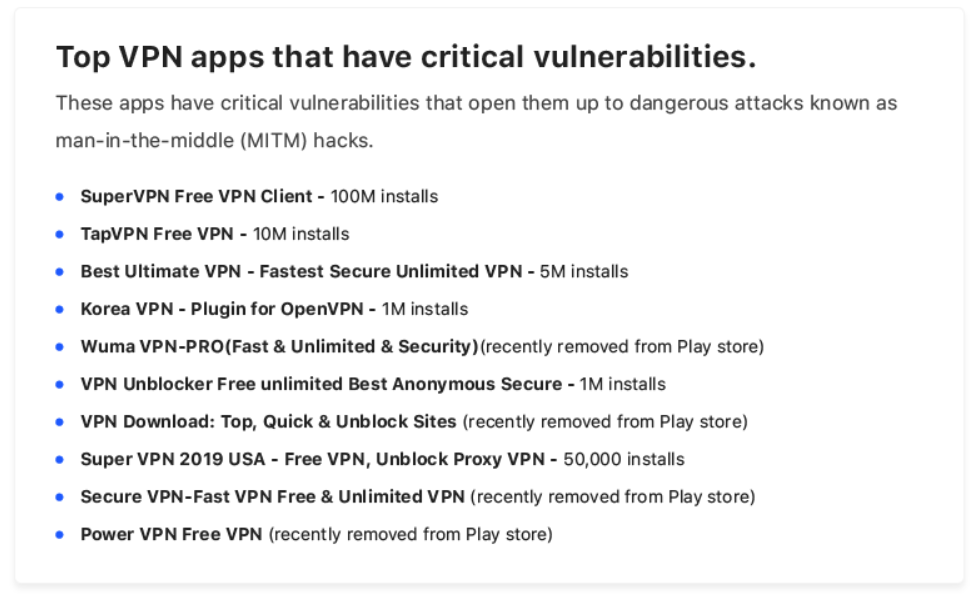
Source: VPNPro
In all, these apps together threaten the security of more than 120 million users. What makes them more suspicious is their negligence towards researchers’ prompts.
After discovering the flaws, researchers informed all the 10 apps about their findings. Yet, just one app, Best Ultimate VPN addressed the matter and fixed the bugs. The other apps did not respond.
Though Google has removed some of the insecure VPN apps recently from the Play Store, the researchers still advise users to remain careful.
If you’ve installed any of these dangerous VPN apps, you should consider alternatives.
Let us know your thoughts in the comments.

