Continuing the trail of security threats to air-gapped systems, now joins a malware. Dubbed Ramsay, the malware with as much as three different variants can steal data from air-gapped networks.
Overview Of Ramsay Malware
Researchers from ESET have caught a new malware ‘Ramsay’ targeting air-gapped networks. Sharing the details in a blog post, researchers revealed that they found around three different malware variants. All of these possess different capabilities, from rudimentary to advanced attack features.
According to the researchers, this malware seems specifically tailored for air-gapped networks. However, it presently appears to be in its developmental phase. And, hence, may acquire more functionalities in the future.
Source: ESET
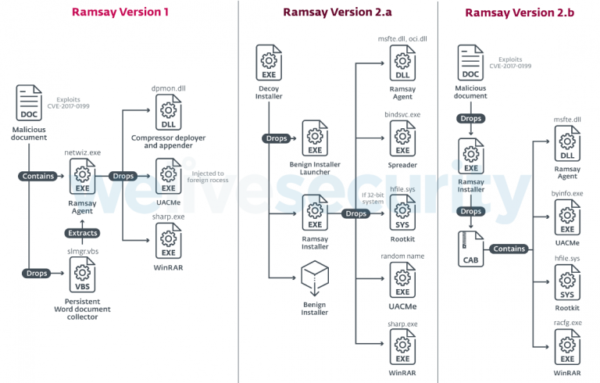
Briefly, the three malware versions leverage different attack vectors to reach the target system, including some old known bugs.
For instance, Ramsay version 1 delivers through malicious documents exploiting CVE-2017-0199 vulnerability. However, this version lacks advanced features and bears low complexity.
Whereas, the researchers found the Ramsay version 2a impersonating a 7zip installer. This version exhibited advanced features including Spreader component and rootkit.
Likewise, the Ramsay version 2b delivers via malicious documents exploiting another old vulnerability CVE-2017-11882. This version lacks the Spreader component (found with version 2a) that serves as a file infector.
Upon reaching the target system, Ramsay can persist on the network as it continues stealing data from the system. This data-stealing does not remain confined to the local system. Rather the malware also looks for the target data in the network and removable drives.
The stolen data (predominantly, the Word files) is gathered in a hidden container awaiting exfiltration later.
Exfiltration Technique Remains Undetected
While the researchers presented the technical analysis of the malware, they could not identify the exact exfiltration technique. Certainly, this is the most important phase of the entire attack.
Yet, they hinted about the associated of this malware with Darkhotel APT Group. They also caught some shared artifacts with Retro backdoor.
The researchers have stated that they will continue monitoring the malware. So, we might get more details about it in the days to come.

