In the previous year, Cerberus malware emerged as a powerful Android trojan. It even revamped its functionalities to become more malicious with version 2. However, the malware didn’t continue for long, and following a team break up, it became available for sale. Nonetheless, a new malware dubbed “Alien” has now appeared to fill up the space created by the demise of Cerberus.
Alien Malware Emerges As The New Android Banking Trojan
Researchers from ThreatFabric have now discovered another Android banking trojan that can replace Cerberus. Dubbed Alien, the malware seems capable enough to serve as the next MaaS (Malware as a Service).
Specifically, Alien is a fork of Cerberus malware. Due to its similarity, the active Alien campaigns are often misunderstood as Cerberus attacks. However, the researchers have made it clear that Alien is a separate malware run by a separate group, and possesses more maliciousness than the Cerberus.
Briefly, the malware emerged in January 2020 as a fork of Cerberus v1. As Cerberus discontinued, its customers seemingly switched to Alien malware that already ran active campaigns in the wild. Their latest effort is the impersonation of a Coronavirus-themed Android app.
Another difference between Alien and Cerberus lies in their C2.
Alien malware is already active in the wild and is seemingly targeting the institutions globally. It’s because the malware allows the threat actors to add personalized targets. Yet, the malware can presently target 226 different Android apps so far, stealing their credentials.
Besides, the malware mainly aims at the commonly targeted regions, such as Spain, the USA, UK, Turkey, Germany, Australia, France, Italy, China, Japan, Switzerland, and more.
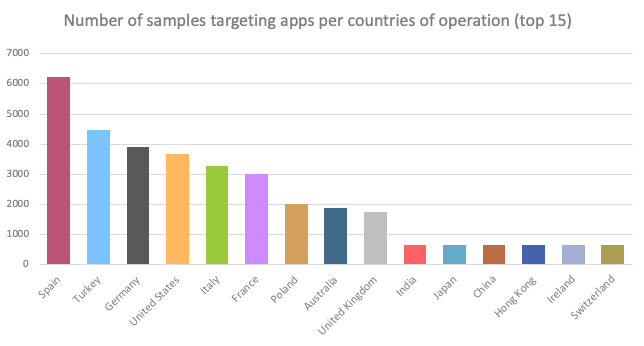
Source: ThreatFabric
What Can Alien Do?
Alien and Cerberus have predominantly similar functionalities. However, Alien is more advanced due to TeamViewer-based remote control and notification sniffer.
Regarding its capabilities, here is what ThreatFabric has described.
“It has common capabilities such as overlay attacks, control and steal SMS messages and harvest the contact list. It can leverage its keylogger for any use and therefore broaden the attack scope further than its target list. Also offers the possibility to install, start and remove applications from the infected device. Most importantly, it offers a notifications sniffer, allowing it to get the content of all notifications on the infected device, and a RAT (Remote Access Trojan) feature (by abusing the TeamViewer application), meaning that the threat actors can perform the fraud from the victim’s device.
For now, the researchers haven’t explicitly described how the malware propagates and reaches the victims’ devices. Perhaps, this step varies according to the preferences of the MaaS customers.
Let us know your thoughts in the comments.

