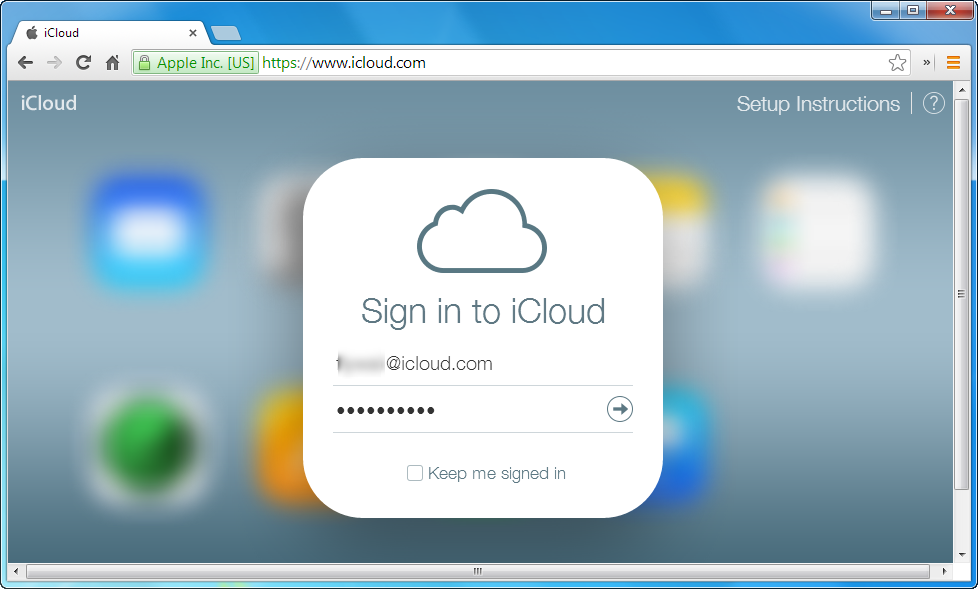
Recently the report said Apple iCloud was breached, but after long investigation Apple said “None of the cases we have investigated has resulted from any breach in any of Apple’s systems including iCloud or Find my iPhone”.
Apple lovers cant’ rest or take is easily as now the brute force abuse of the login feature for the service is not longer possible.
More than 40 hours have been spent investigating the cause of the leak, as rumors about possible vulnerabilities in its software set customers on edge”,Apple Says.
It seems that the celebrities fell victims to targeted attacks replying on social engineering techniques to know or discover the user name, password and security information and questions. A well planned phishing campaigns targeted specifically at them not any hacking or attack involved.
“It is more likely that the images have been acquired though spear phishing attacks or social engineering, which exposed a username and password”,believed Cloudmark research analyst Andrew Conway
Although this method is been investigated and speculated by security researchers too. Changing passwords more often is a good practice to safe account from attackers. Setting hard passwords coupled with 2FA is the suggestion of security experts.
2FA ensures that even the username and password are hacked and discovered by the hackers, they wont’ allow to access contents in the account because a 3rd authentication code would be required at that time, which will be genrally delivered to the users’ phone via SMS.
However all nude pics of celebrities leaked online are not real and some content is fake. Mary Elizabeth Winstead, Kirsten Dunst and Jennifer Lawrence were among those admitting the photos were real. Even FBI are also under investigation on this case.