According to top-secret documents from the NSA and the British agency GCHQ, the intelligence agencies are seeking to map the entire Internet, including end-user devices.
The National Security Agency and its British counterpart, GCHQ, gained secret access to the German telecom companies’ internal networks, including Deutsche Telekom and Netcologne, in an effort to “map the entire Internet — any device, anywhere, all the time.”
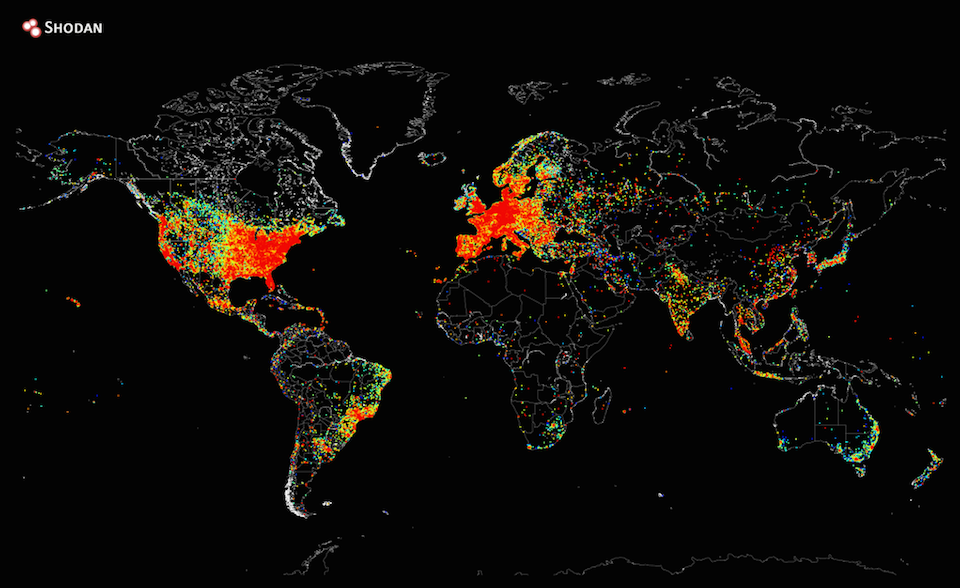
As reported by German news publication Der Spiegel, citing the new set of leaked documents provided by former NSA contractor Edward Snowden, the five major intelligence agencies including NSA and GCHQ have been collaborating to get near-real-time visualization of the global internet as a part of NSA’s ‘Treasure Map’ surveillance program, also dubbed as “the Google Earth of the Internet.”
“[The program aims] to map the Internet, and not just the large traffic channels, such as telecommunications cables. It also seeks to identify the devices across which our data flows, so-called routers. [The program] allows for the creation of an ‘interactive map of the global Internet’ in ‘near real-time,'” the report said.
The Treasure Map program was described by Snowden as “a 300,000 foot view of the internet,” as it allows agencies to collect Wi-Fi network and geolocation data from around the world, along with 30 million to 50 million unique internet provider addresses. The program was first made public by the New York Times report late last year, along with other documents by Snowden.
But at the time, the US intelligence officials apparently claimed that program was not used for surveillance purposes, but only for mapping foreign and US Defence Department networks, “limited by the amount of data available to the agency,” according to the NY Times report