George Chatzisofroniou has published a new Method for Hacking WPA/WPA2 Security using a WiFi social engineering tool designed to steal credentials from users of secure wireless networks.
The administrator at the University of Greece developed the WiFiPhisher tool which is used to discover and replicate WPA-protected networks, sans password.
The tool, can be downloaded from GitHub here and works by producing a number of deauthorisation packets at a legitimate access point jamming it and prompting users to inspect available networks.
Users will see the malicious network posing as their trusted access point.
“WiFiPhisher is a security tool that mounts fast automated phishing attacks against WPA networks in order to obtain the secret passphrase [and] does not include any brute forcing,” Chatzisofroniou @_sophron said.
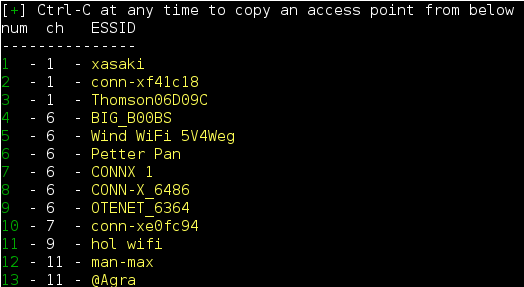
“WifiPhisher sniffs the area and copies the target access point’s settings [and] creates a rogue wireless access point that is modeled on the target.”
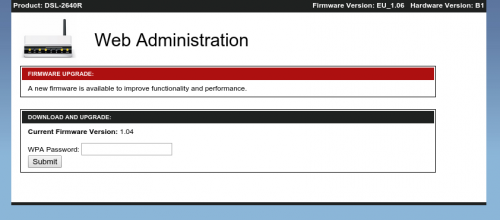
“As soon as the victim requests a page from the internet, WifiPhisher will respond with a realistic fake page that asks for WPA password confirmation due to a router firmware upgrade.”
New Method for Hacking WPA/WPA2 Security
How it works
Wifiphisher is a security tool that mounts fast automated phishing attacks against WPA networks in order to obtain the secret passphrase. It is a social engineering attack that unlike other methods it does not include any brute forcing. It is an easy way for obtaining WPA credentials.
Wifiphisher works on Kali Linux and is licensed under the MIT license.
From the victim’s perspective, the attack makes use in three phases:
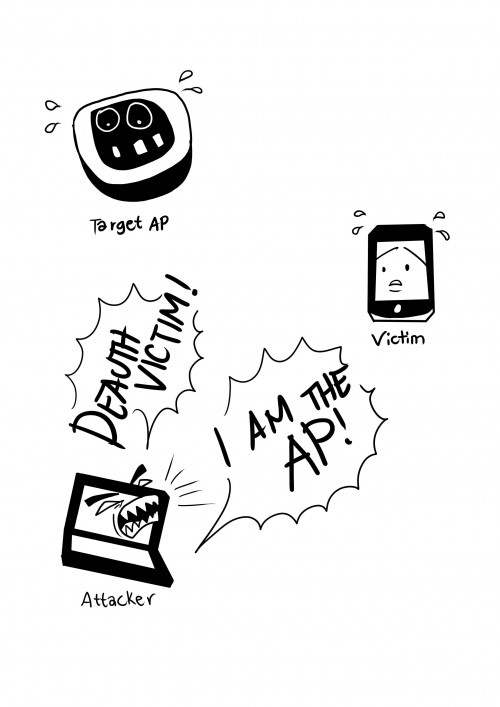
1.) Victim is being deauthenticated from their access point. Wifiphisher continuously jams all of the target access point’s wifi devices within range by sending deauth packets to the client from the access point, to the access point from the client, and to the broadcast address as well.
2.) Victim joins a rogue access point. Wifiphisher sniffs the area and copies the target access point’s settings. It then creates a rogue wireless access point that is modeled on the target. It also sets up a NAT/DHCP server and forwards the right ports. Consequently, because of the jamming, clients will start connecting to the rogue access point. After this phase, the victim is MiTMed.
3.) Victim is being served a realistic router config-looking page. wifiphisher employs a minimal web server that responds to HTTP & HTTPS requests. As soon as the victim requests a page from the Internet, wifiphisher will respond with a realistic fake page that asks for WPA password confirmation due to a router firmware upgrade.
Here is a diagram of the above:
New Method for Hacking WPA/WPA2 Security

18 comments
Please kindly show me a step by step way to install this software. i couldn’t open the file after download. please give me a step by step method
thanks
New? That metod is basically a reworked way of the fundamental and and very well known “Evil Twin” method.
The exact technique also has some requirements:
– The fake hotspot has to have a higher transmit power (in mW / dbm);
– It’s probably gonna work only if the attacker is physically closer to the victim compared to the real router – victim.
Well, nice 2k15 refresh tho 😉
you can download this from this page :https://github.com/sophron/wifiphisher
you found it under Clone in Desktop button , name is Download . zip
Great idea, but i found whilst testing on multiple wifi routers that it causes a DOS on the users which you are attempting to social engineer the key from, since they do not connect the rouge AP. I have even used high gain antennas and still cannot get them to join the rouge network.
can u send me one? for educational purposes only.
https://github.com/sophron/wifiphisher/archive/master.zip
Jajajaja Fabulous!!!
Download now!
Please send copie for educational use
How Can We Download It..?
Is this tool is available for windows ????
No it’s not..
WifiPhisher
can u send me one? for educational purposes only.
educational purposes :))))) good 😉
The LINSET script is much better than this and there from 2013 http://www.dragonjar.org/crackeando-redes-wpa-y-wpa2-sin-diccionario.xhtml
Sinister…
lel
BUT LINSET DO THE SAME…. OR NOT ?
Comments are closed.