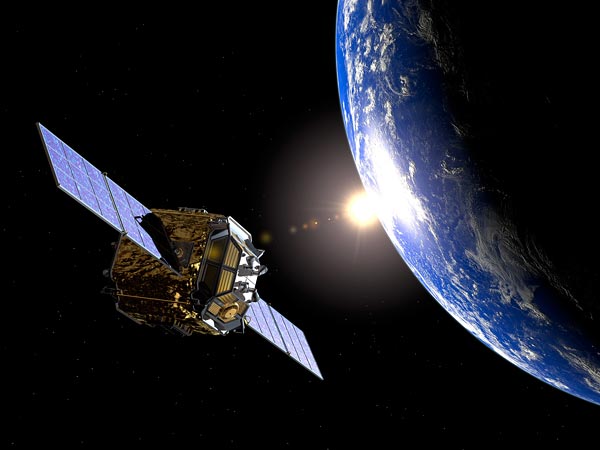
Turla, a cyber-espionage group which many suspect is made up by Russian-speaking hackers has been accused of hijacking vulnerable commercial satellite communications by Kaspersky, using hidden receiving stations in Africa and the Middle East to mask attacks on Western military and governmental networks.
It was a new exquisite attack channel being used by the group that was virtually untraceable.The Turla hackers buy a satellite dish to intercept that traffic, rent a house in the area where those vulnerable satellites provide coverage, and also get a classic landline Internet connection.

As traffic comes down from the satellite the hackers sniff through its content and see what users are online at that moment, randomly selecting an IP.This IP is broadcasted to their botnet’s infected clients via the landline, clients which then send their stolen data via the satellite connection to the IP of an unsuspecting satellite Internet subscriber.By this hackers can easily perform a MitM (man-in-the-middle) attack and intercept the traffic meant for that IP.
“Safe to say this is the ultimate level of anonymity that any cyber espionage group has reached in terms of hiding its origins”, said a senior security researcher at Kaspersky.