If someone is determined enough to guess your password using brute force then you need to lock down Windows . Here’s how to lock down Windows following several failed login attempts. Complex passwords can be a pain to remember and prone to mistyping, but shorter passwords can be much easier to guess by brute force.
What is a brute force ? – Brute force is generally trying huge numbers of passwords until the correct one is guessed.
In other words it is a trial and error method used by application programs to decode encrypted data such as passwords or Data Encryption Standard (DES) keys, through exhaustive effort rather than employing intellectual strategies.
Reducing the effectiveness of a brute force attack :
By limiting the number of “guesses”available before the system locks the account, requiring an administrator to reset it before the user can sign in again.
The three local security polices you need to set are:
- Account lockout threshold – which sets the maximum number of invalid login attempts before the lockout occurs.
- Account lockout duration – which sets the time in minutes for which a lockout will remain in force. If you set this value to zero, the lock will remain until reset by an administrator.
- Account lockout window – which is responsible for setting the total length of time which must pass before the count of failed login attempts is reset to zero.
Setting the lockout policy
Open an Admin command prompt, like just run the cmd as an administrator (On Windows 8.1 press Windows+X and then select Command Prompt, Admin. )
After opening the command prompt, type:
Net accounts /lockoutthreshold: value
Net accounts /lockoutduration: value
Net accounts /lockoutwindow: value
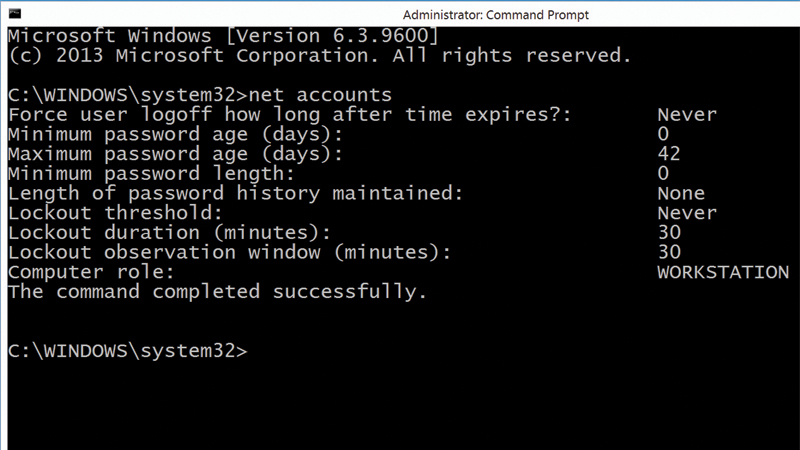
You can check your default options by typing “net accounts” in your admin command prompt.
While using this policy defends against brute force attacks on passwords, it introduces another possible vulnerability, in that an attacker could cause disruption by deliberately locking multiple accounts by repeatedly trying incorrect passwords.