A set of Google Chrome extensions that were hijacking Facebook accounts which was found by an 19-year-old Danish student named Maxime Kjaer, has been removed by Google. These extensions were distributed via Facebook posts for all sorts of viral content. Users who clicked on the links were asked to install one of many Chrome extensions which were capable of many more malicious actions apart from hacking your Facebook account.
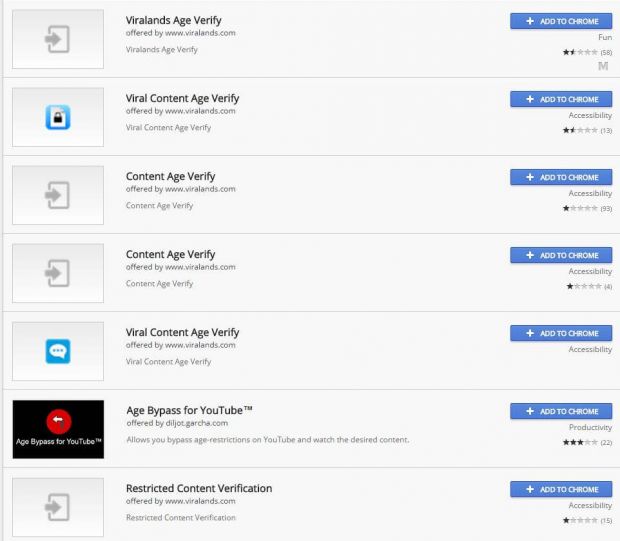
All of these extensions had a similar name like involving the words “viral“, “age“, and “verify“, and were hosted on the Google Chrome Web Store, which helped users dispel any doubts they had about the extension’s legitimacy. Researchers reported the IP addresses used to download the malicious script payload and the C&C servers to Digital Ocean, the company that was hosting the servers.
Kjaer Explanation On These Extensions
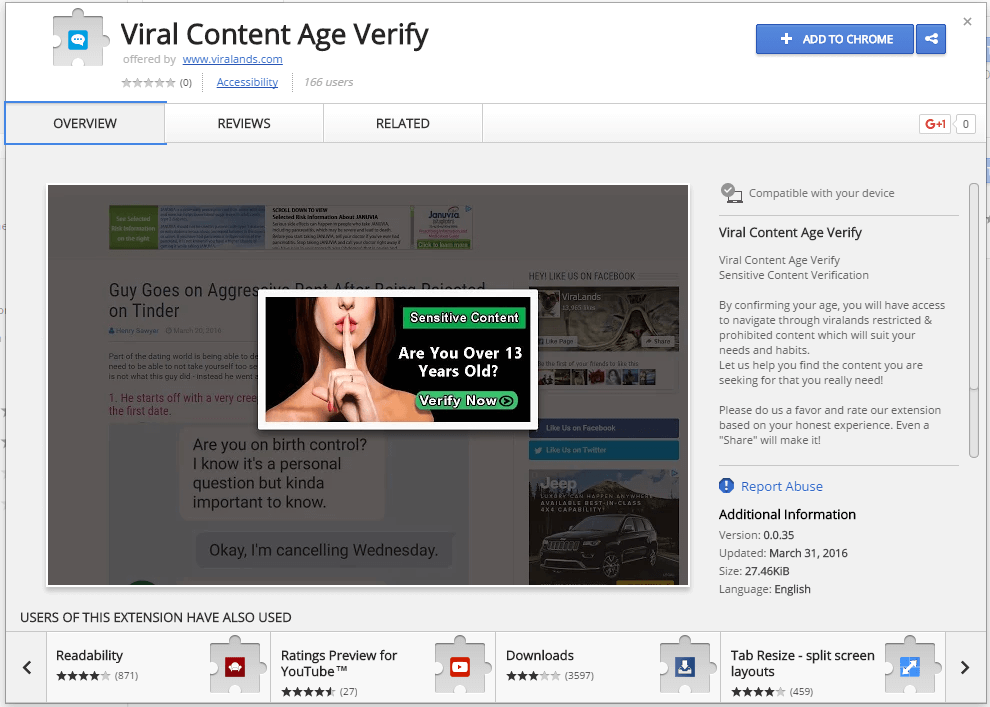
Kjaer explained that all these extensions requested intrusive permissions, such as the ability to “Read and change all your data on the websites you visit”, which gives complete control of a user’s visited sites. He added that the extensions contained only three files which executes in persistent mode, that is they couldn’t be paused and executed from when the browser started until the user shut it off.
There was no “less than 18” verification process and that the source code found inside this file only started a random timer after the user filled in their date of birth, and then showed “Loading…” during the timer and “Done!” at the end, according to Kjaer.
All the malicious activity could be found only in the third file. Because of Google’s automated scans when submitting extensions to the Chrome Store it is not possible to include malicious code inside the extension so this third script would connect to a server and download another script, which it would later execute. By this method the hackers manage to bypass the Google’s scan and upload their extensions.
It was a C&C server used to control the infected browsers
Basically the downloaded script would be able to make requests and receive instructions from a command and control (C&C) server. During Kjaer’s experiment, the C&C server told his browser to access a Facebook URL that exposed his access token, a programmatic key to his Facebook account. Because of the “Read and change all your data on the websites you visit” permissions the user has granted the extension at installation, the crook was able to recover this access token. As soon as their access token was stolen, the C&C server instructed the user’s browser to give a Like to a Facebook Page Kjaer had never seen before.
According to his calculation over 132,265 infected computers had installed the malicious Chrome extensions. He also informed Google, who removed the extensions from the Chrome Web Store and then blacklisted them, which means they were automatically uninstalled from all infected browsers.