Commix is a command injection exploitation tool used for testing command injection vulnerabilities in web applications. Command injection, also known as shell injection is achieved through vulnerable applications. For the attack to be successful, the application must pass unsecure user supplied data to the system shell. The tool is written in Python language.
Who can be the Victim of Command Injection?
The command injection attacks are independent of the operating system in use. They can target Linux, Unix, and Windows as well. They are also independent of the programming languages used as they can inject themselves into many programming languages including C, C++, PHP, Python, and Java.
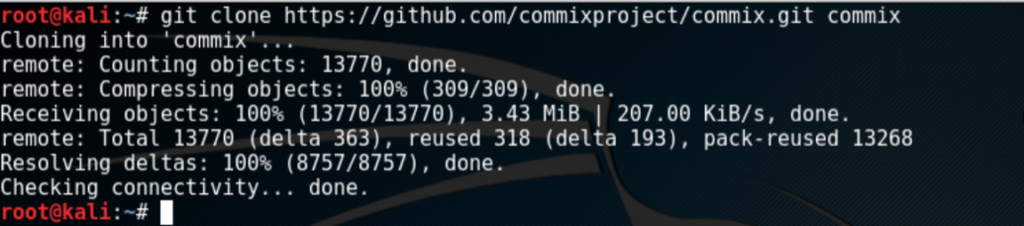
Commix Installation
Commix is supported by Linux and Mac OS X. The Commix version for Windows OS has been released as a pilot. Commix comes preinstalled with some Linux distributions including Backbox, BlackArch Linux, Parrot Security OS, and Weakerthan Linux. The tool can be downloaded from Git repository using the following command.
git clone https://github.com/commixproject/commix.git commix
The tool can be installed using the following command
--install
More helping features can be explored using the help command
--help
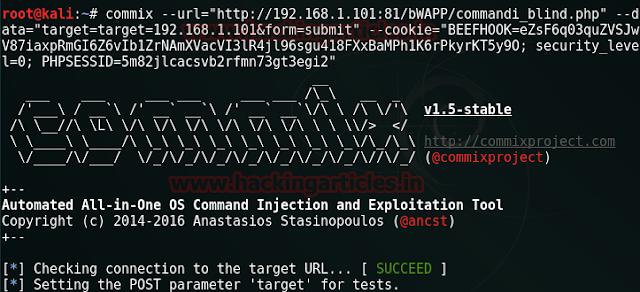
How Commix Works?
Commix works in three steps. First, the attack vector generator module generates attack vectors. Attack vectors are different attack techniques including classic, eval based, time based, and file based techniques. Attack vectors perform the vulnerability test in the host application (target). If the vulnerability is found, the exploitation step is then launched to exploit the vulnerability.
Command Injection Options
Commix provides different command options to find and connect with the target application. To set the target Url, the following command is used.
--url = URL Here, the ‘URL’ is the target web address.
Various connection options are available to select how to connect to the target URL. Some of the options to connect to the target URLs are through data strings, HTTP headers, cookies, and authentication parameters. Enumeration options are also available to enumerate the target. Some of the options include usernames, hostnames, system users, system users privileges, system users password hashes etc. Options for defining the payload parameters are also available in the command injection options.
Command Injection Techniques
Commix supports two major command injection techniques including result based command injection and the blind command injection technique. The result based command injection technique allows for visible commands being reflected back to the attacker within the web application. The blind command injection technique is used when the response from the web application may not be displayed on screen. In that case, one has to infer the results by using the time based or file based technique. The time based technique requires the commands that introduce the time delays. In file based technique, a file is used to record the response from the application.
Commix is mostly used by security experts, penetration testers, and web developers for finding bugs and vulnerabilities in the web applications.
What Bunny rating does it get?