Fluxion is a wifi security analysis tool that can simulate wifi attacks using the MITM technique. The tool can create rogue access points and steal wifi credentials through phishing. The tool also tries to obtain WPA/WPA2 encryption hashes through handshake process.
Fluxion Installation
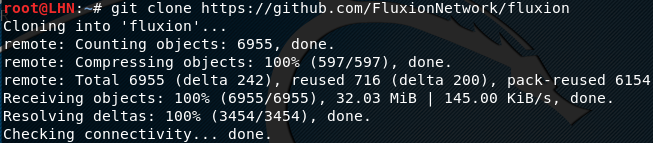
Run the following command in order to clone the Fluxion from github repository.
git clone https://www.github.com/FluxionNetwork/fluxion.git
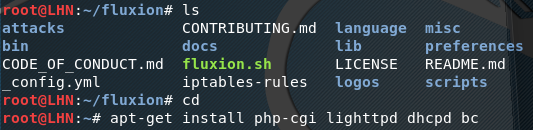
Fluxion depends on different packages, such as aircrack-ng, bc, dhcpd, nmap, openssl, xterm, route, fuser, lihttpd, macchanger, and php-cgi. The packages required by Fluxion are auto installed while running the Fluxion for the first time. Move to the Fluxion directory and run the following commands in order to auto install the missing dependencies.
cd fluxion ./fluxion.sh
However, using the above commands sometimes fails installing the required packages and Fluxion does not work. In that situation, note down the missing packages that are marked by Flxuion and install them manually by using the following command.
sudo apt-get install <missing packages>
For example
sudo apt-get install php-cgi lighttpd dhcpd bc
Wifi Security Test Using Fluxion
Fluxion tool can be set into action by running the following command in the terminal.
./fluxion.sh
The tool checks if all the dependencies are fulfilled. If all the required packages are installed, the tool offers a choice of attacks that can be performed. Currently, there are two types of attacks that can be launched with the tool. These are Captive Portal attack and Handshake Snooper attack. The Captive portal attack allows creating the rogue access point (evil twin) to steal the wifi credentials, while Handshake Snooper attack is used for acquiring WPA/WPA2 encryption hashes.
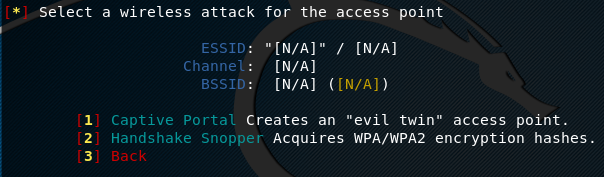
Let’s suppose we select the first option to simulate the Captive Portal attack. Fluxion scans the available wifi interfaces and asks the user to select the desired interface to imitate it (fake rogue access point) for the attack.

Fluxion starts a DNS server to redirect all the requests to the attacker’s machine. A jammer starts, de-authenticating the users and asking them to re-enter the wifi credentials into a spawned web server. Once the user enters the correct wifi credentials, the attack automatically terminates. The valid wifi credentials can be seen from the fluxion portal.
What Bunny rating does it get?
Fluxion is a powerful tool that can simulate the WPA/WPA2 wireless attacks without using dictionary or brute-force techniques. As a result we will be awarding this tool a rating of 4.5 out of 5 bunnies.




![]()

