All of us think of VPNs as our savior when it comes to online privacy. VPNs play a vital role in protecting ourselves from potential hackers. But, what if the VPNs themselves get hacked? Another interesting report from DEF CON tells us how exploiting a compression algorithm against VPNs can increase VORACLE attacks.
VORACLE Attacks Can Result In VPN Compromise
At DEF CON, a researcher Ahamed Nafeez demonstrated a method to hack VPNs. However, it worked only in the case of HTTP connections, VPNs working with HTTPS remain safe from this attack.
As explained by Ahamed, the VORACLE attack involves exploiting compression algorithms to alter VPN encryption features. In other words, VORACLE is simply a Compression Oracle Attack on a VPN. VPNs working over the OpenVPN protocol first compress the user data transmitted between a user and the VPN server prior to encryption.
Nafeez explained his findings through a detailed presentation. Thankfully, conference officials have uploaded the presentation on the DEF CON media server.
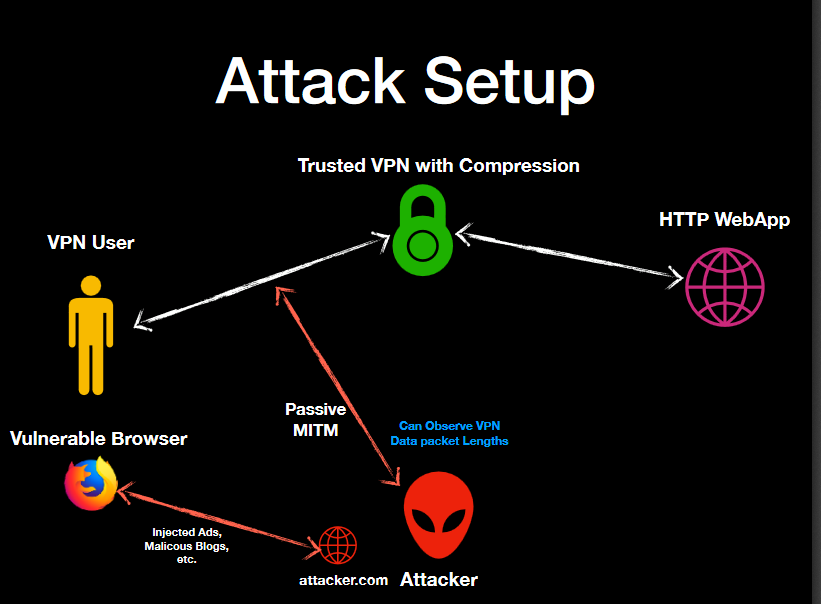
Slide from Ahamed Nafeez’s presentation delivered at DEF CON 2018, showing how an attacker could exploit VPN compression to access encryption keys.
Fortunately there is a little bit of a silver lining since most of websites today use SSL. Considering how CRIME (in 2012), TIME and BREACH attacks (in 2013) created problems with TLS protocols used by websites, HTTPS went through several changes and is now hardened to such attacks. Never the less, a number of websites still do not use HTTPS.
Nafeez went on to say:
“It is time everything moves to HTTPS. There is really no excuse for any website not to use it anymore.”
Though Google has already begun marking HTTP websites as “Not Secure”, many web links do not switch to HTTPS.
Let us know your thoughts on this in the comments section.

