Zeus scanner is an open source tool used for reconnaissance and vulnerability assessments of web applications. The tool is equipped with a powerful parsing engine to extract cached web pages from multiple search engines. During parsing, the robots.txt and sitemap.xml files information of target host is saved in a file on the local system.
The tool also has the ability to bypass the API calls, IP blocking, and captchas security while extracting data from search engines. Supported search engines include Google, Bing, AOL, and DuckDuckGo. Zeus supports Tor proxy and Tor browser emulation.
Besides the reconnaissance feature, Zeus also has the ability to assess various web vulnerabilities, such as SQLi, XSS, clickjacking, port scanning, admin panel information, and Whois lookup information. The vulnerability assessment can be performed either by running a default user-agent, personal user-agent, or one can select a random user-agent from an available pool of 4000 random user-agents scripts.
The record of the useful information obtained while scanning the target is saved in a log file. Zeus can also identify defensive strategies. This includes the identification of an intrusion detection system, intrusion prevention system, and web application firewalls.
How to Install Zeus Scanner
Zeus Scanner requires some libraries and packages to operate. The basic requirements include Firefox version 52-58, Sqlmap, libxml2-dev, libxslt1-dev, and python-dev. Firefox can be updated or installed using the following commands.
sudo apt-get update sudo apt-get install firefox
Sqlmap can be installed from the github repository using the following command.
git clone https://github.com/sqlmapproject/sqlmap.git
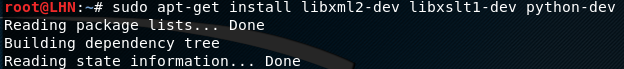
libxml2-dev, libxslt1-dev, and python-dev. can be installed as follows.
sudo apt-get install libxml2-dev libxslt1-dev python-dev
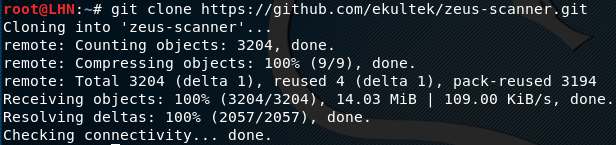
Besides dev, libxslt1-dev, python-dev, Zeus requires some python packages, such as selenium-webdriver, requests, python-nmap, whichcraft, lxml, beautifulsoup, psutil, and pyvirtualdisplay. Before installing these packages, clone the Zeus Scanner setup from github repository using the following command.
clone https://github.com/ekultek/zeus-scanner.git
The final step is to install the aforementioned python packages using the following commands.
cd zeus-scanner sudo pip2 install -r requirements.txt
How Zeus Works
Run the Zeus tool by executing the zeus.py file in the following format.
sudo python zeus.py
The simplest way to scan a target is done by passing single dork scan argument (-d) to the following command.
python zeus.py –d <target website>
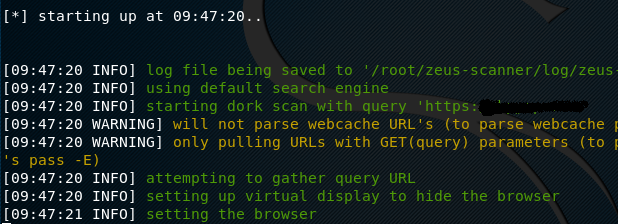
The tool starts extracting data from the search engines and saves the results in the root/zeus-scanner/log folder.
To run the dork list, the following command needs to be run in the terminal.
python zeus.py –l dork.txt
The dork.txt contains the urls to be scanned with the tool. The other arguments, e.g proxy setting, can also be appended with the commands in the following format.
python zeus.py –d <target website> --proxy=”proxy address here”
Similarly, we can use Zeus to check if the target host is vulnerable to SQL injections by sending the request to the sqlmap tool.
python zeus.py –s –d <target website> --sqlmap-args=”threads 5, level=3, risk=3, randomAgent true”
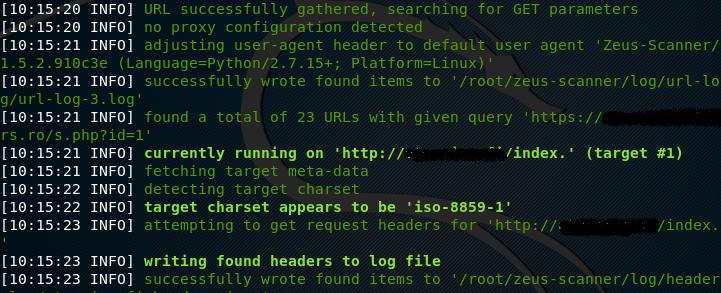
By running the above command, the tool validates the url and parameters required to proceed with the sql injection query.
What Bunny rating does it get?
The tool helps in finding certain client urls that are either blocked or hidden from public search forums. Such urls can be helpful in identifying possible hidden vulnerabilities that can be later exploited by the pen tester. The addition of tools like sqlmap in Zeus can verify the vulnerabilities and the false negatives, as a result we will be awarding this tool a rating of 4 out of 5 bunnies.




Want to learn more about ethical hacking?
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.