Leviathan is an open source toolkit that can be used for auditing networks and web applications. The types of audits that can be performed with Leviathan include discovery of services running on machines, identifying SQL injections in web applications, analyzing the possibility of bruteforce attacks on discovered machines, and testing the security of pre-discovered machines with custom exploits.
Within the service discovery option, Leviathan checks for the presence of SSH, RDP, MYSQL, FTP, and Telnet services running on machines located in a specific IP range or country. Leviathan makes use of Shodan, Censys, and Masscan utilities to find the running services. The bruteforce option allows to brute force the discovered services to see if they can be exploited. Leviathan uses the ncrack tool and a default passwords combination list. Similarly, the SQL injection option allows the assessment of sql injections on web applications.
Leviathan Installation Guide
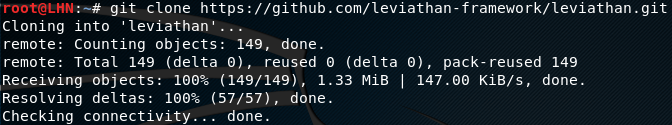
Leviathan is python toolkit that requires Python 2.7.x and is supported by Linux (Ubunto, Kali, Debian) and MacOS. The toolkit can be cloned from github using the following command.
git clone https://github.com/leviathan-framework/leviathan.git
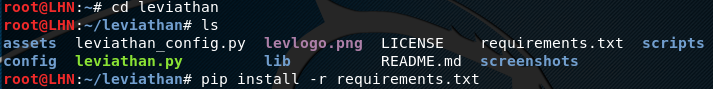
Leviathan toolkit requires Shodan, bs4, lxml, google-api-python-clinet, and requests packages. These dependencies can be installed by running the following commands.
cd leviathan pip install –r requirements.txt
How Leviathan Toolkit Works
Once the toolkit is successfully installed, it can be run using the following command.
python leviathan.py
The above command runs the Leviathan toolkit with multiple options to start the auditing.
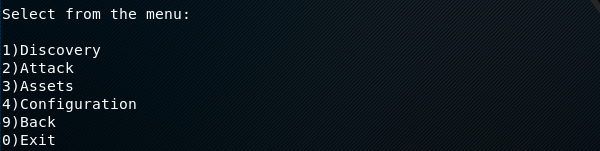
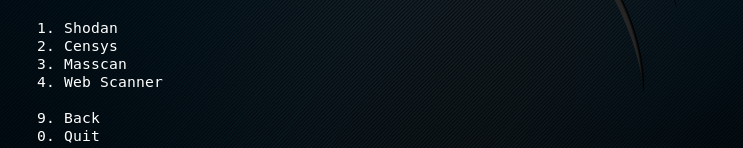
Start with the discovery module. The discovery module gives the option to discover the running services on specific machines in a specific region or ip range, or web applications with specific extensions. For instance, we select the Masscan option to discover services running on our client machines.
After selecting Masscan, the tool asks for IP range and the type of service to start scanning the machines. For demonstration purposes, we give the local ip range to the tool. The tool scans the target machines and saves the results in Leviathan’s assets folder.
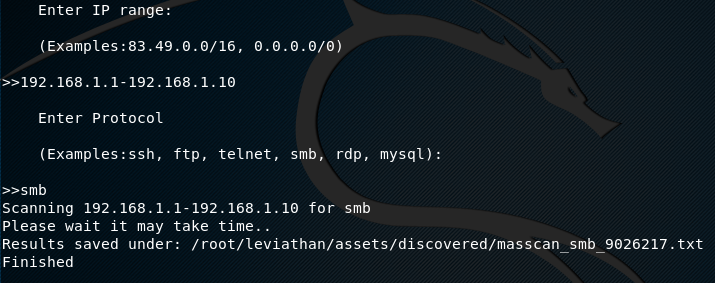
In the next steps, we can audit the machines by running the bruteforce attack for the discovered services on the target machines.
What Bunny rating does it get?
Leviathan toolkit is very helpful in discovering running services on specific machines in a given IP range and exploiting them with the built in exploit features. However, the tookit does not allow the audit for a specific web application. As a result we will be awarding this tool a rating of 3.5 out of 5 bunnies.



![]()
Want to learn more about ethical hacking?
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.