Cmsmap is a python based CMS scanner for automating the process of vulnerability assessment in most popular CMS’s. It can search for interesting files, plugins, directories and known vulnerabilities in WordPress, Joomla or Drupal.
Installing CMSmap
To install CMSmap you have to clone the repo from github.
git clone https://github.com/Dionach/CMSmap.git
After that, you need to make the right changes to the cmsmap.conf file inside the cmsmap folder. If you have Kali Linux you are good to go. If not make the right changes after the [exploit-db] option to your exploit-db path.
cd CMSmap/cmsmap nano cmsmap.conf
Running CMSmap
Run CMSmap through python3.
python3 cmsmap.py -h
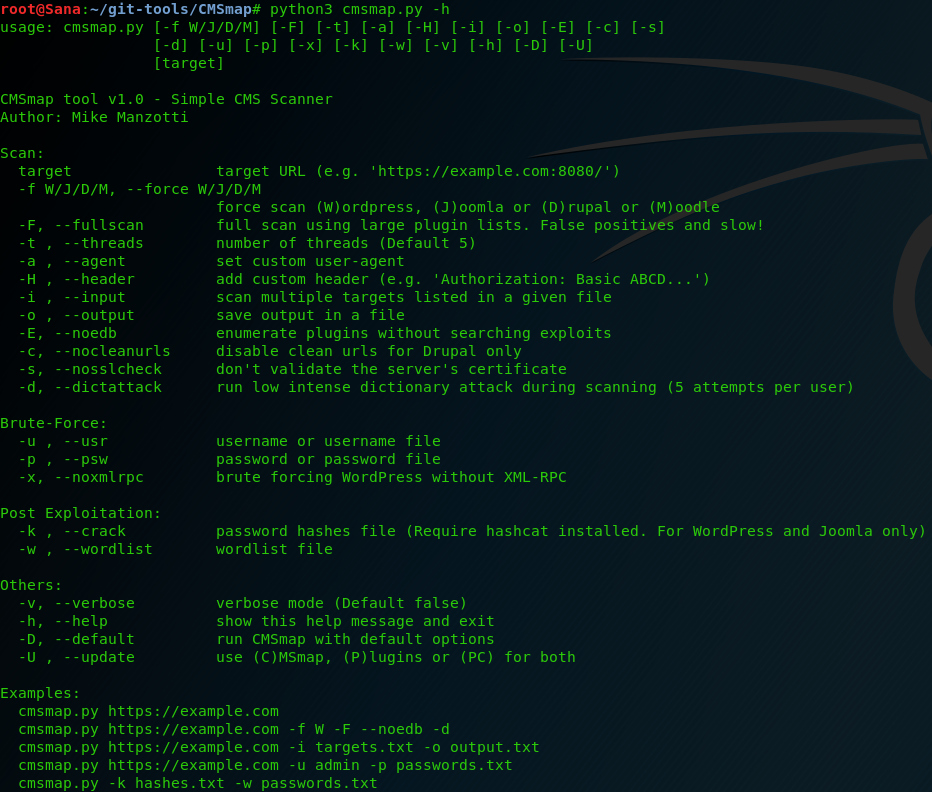
We got a lot of different options to use. We can change the type of the target, the threads, the agent and the certifications options. Also, we can Bruteforce the target and even crack hashed passwords.
In our example, we will perform a full scan against a Joomla CMS target.
python3 cmsmap.py [target] -f J (joomla) -F (full-scan)
The first time you will run the script, it will install all the missing components. Then give it sometime for the script to finish.

We got some interesting data from the scan. At first, we got some basic stuff such as the Joomla Version, the templates of the website and the Administrator and the server that is running.

After that, we got some interesting files, we should check them later for further information. Also, there are some Joomla Components with the known Vulnerabilities. Some have cross-scripting, other are vulnerable to SQL-injection. However we need to check them manually for false-positives.
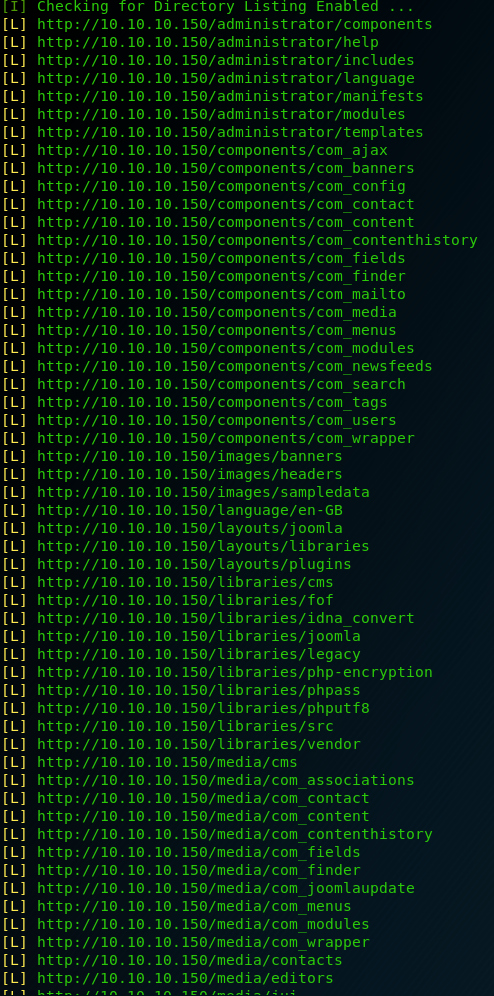
In the end, we got a Directory listing. We can search them later for further vulnerability assessment.
What Bunny rating does it get?
CMSmap can automate some process in the vulnerability assessment phase for you. It can list some interesting data. However, you shouldn’t base your results in only one tool, there is a high risk for false-positives. Overall, it’s a good tool I’m giving it 3 out 5 bunnies.



Want to learn more about ethical hacking?
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.

Comments are closed.