KillShot is a penetration testing tool that can be used to gather useful information and scan vulnerabilities in target host devices and web applications. KillShot makes use of the Shodan search engine to find information about target devices.
Web application information gathering process is carried out by using inbuilt scripts. The KillShot tool can crawl target web applications and find backend web technologies, identify content management system in use, and scan open ports with running services.
The types of vulnerabilities that can be detected with KillShot include SQL injection, XSS, Tomcat RCE, and CMS vulnerabilities. Moreover, KillShot has the ability to generate backdoors to connect with the target. Backdoors need to be uploaded manually to make connection between the target and KillShot tool.
KillShot Installation
KillShot is a ruby script tool that can be cloned from Github using the following command.
git clone https://github.com/bahaabdelwahed/killshot

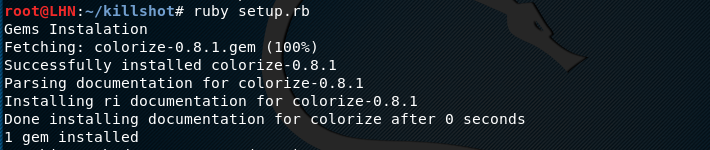
The killshot directory contains setup.rb setup file that should be run in order to complete the installation process.
cd killshot ruby setup.rb
How KillShot Works
In order to execute KillShot tool, run the following command in the terminal.
ruby killshot.rb
In the next step, we need to select web application or target device by typing site or targ arguments in the command line. The full list of arguments can be viewed by typing help command as shown below.

To start scanning web application, type site in the command line.
>site
In the next step, type the target web address
>testphp.vulnweb.com
After filling the above mandatory fields, KillShot gives different penetration testing options shown in the following screenshot.

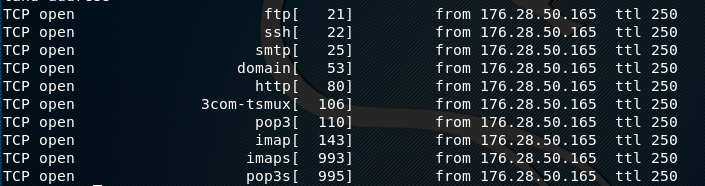
Let’s assume we need port information of the target web application. We can launch port scanning by selecting its sequence number i-e # 3. KillShot offers Nmap and Unicorn utilities to scan target web application ports. We can select any of these utilities to process with the port scanning process.

The tool scans the target ports and displays results in the following format.
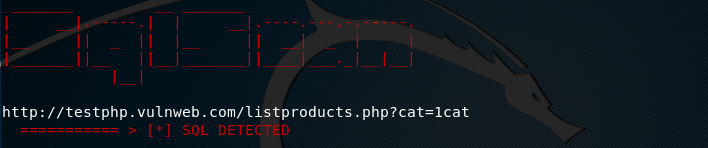
Similarly, we can select the vulnerability assessment option from the list to scan target web application for the said vulnerabilities (SQL, XSS, and Tomcat Rce). The tool asks for the potential parameters to be scanned for the SQL injection analysis. If the target url is vulnerable, the tool displays results in the following format.
What Bunny Rating Does it Get?
KillShot is a quick information gathering and vulnerability analysis tool. The information gathering features are decent. However, the scope of vulnerability analysis is limited. The tool does not perform deep scanning of directories or pages in vulnerabilities analysis operations so therefore I am awarding it 3.5 bunnies out of 5.




Want to learn more about ethical hacking?
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.

