Reconnoitre is a tool that was created to automate routine actions within the OSCP lab environment. It is a simple script, which can automate information gathering and service enumeration. It searches for the live hosts, and performs a scan on the hosts that are found, enumerates its detected services and sends commands to it. The tool can discover virtual hosts running on the targeted system. The information is stored methodically by creating a directory like structure to store the findings, results, and methodologies used for each host, recommended commands to execute and the directory structures for storing loot and flags.
Downloading and Installing Reconnoitre
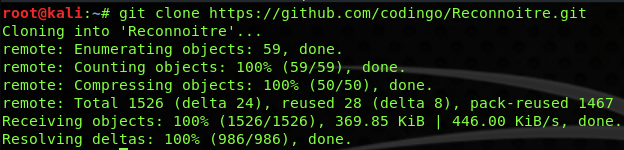
It can be downloaded in the Kali Linux with the following command;
git clone https://github.com/codingo/Reconnoitre.git
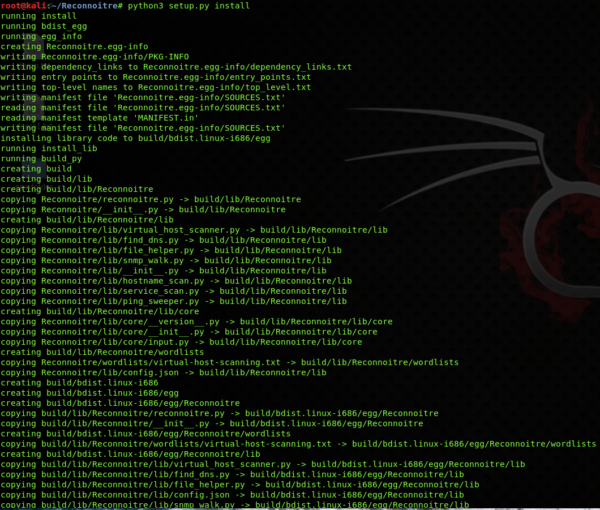
Once the download completes, make sure you have python3 installed as it is a pre-requisite for the installation. You need to navigate to its downloaded directory and install it using the command given below;
python3 setup.py install
Running Reconnoitre
We will first look for the help file;
reconnoitre -h
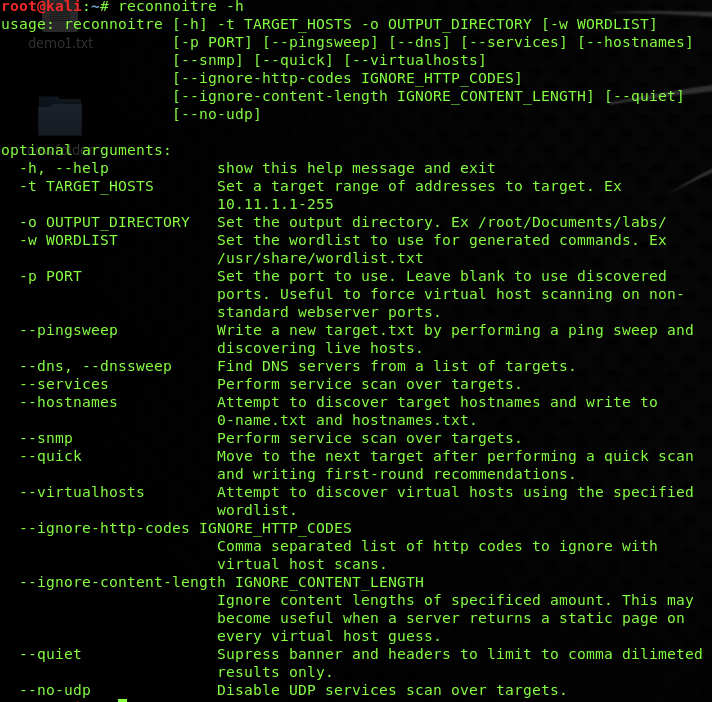
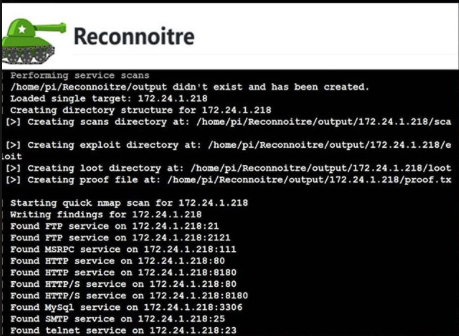
You can see that it is a simplified tool with many awesome functions. In this example, we will use some basic options, like starting with the service enumeration and saving the result in a directory with them. Start the quick service enumeration scan with;
reconnoitre -t <IP ADDRESS> --services --quick -o /root
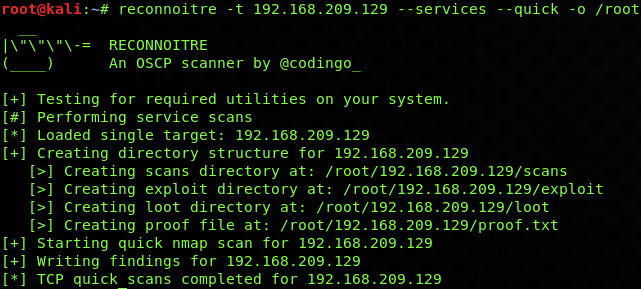
The result can be seen from the directory which was mentioned in the -o argument;
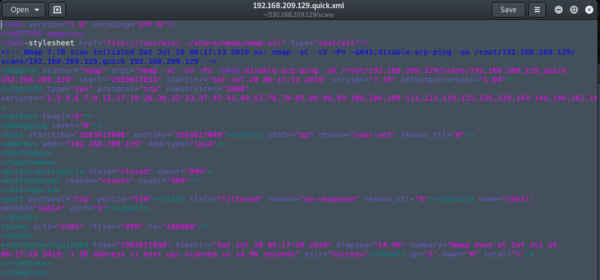
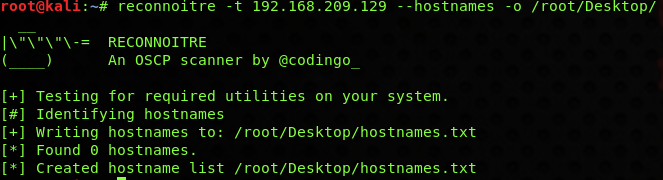
The above performed a quick scan on the target and provided numerous useful results in an easily readable format, now scan for the target’s hostname;
What Bunny rating does it get?
Reconnoitre is very easy to use, it can be customised easily using their option flags to make it do the job you require. You save a lot of time by using it, and the data you gain can be handy in the information-gathering phase. I am giving it 4 out of 5 bunnies.




Want to learn more about ethical hacking?
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.