Recent trending news all over the world, the nude pics leaked online by hackers which rattled not only the fans but also for the scammers. The content popped all over and the method used was brute-force the login into Apple’s iCloud service, which did not have protection against this type of attack.
Having lot information about this incident, scammers take advantage and started to prepare phishing mails targeting Apple ID users.Not just emails are delivered by the cybercriminals, as Satnam Narang from Symantec notes that, smishing is also used.
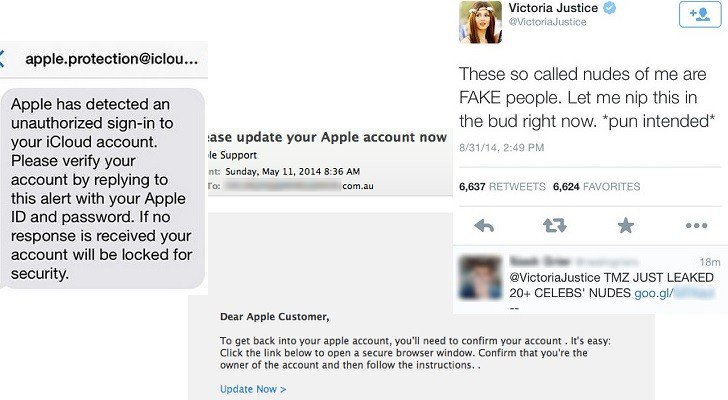
Smishing is a phishing attack carried out via short text messages sent to the victim’s phone who make use of Apple ID. The message claims as it had come from an Apple division and inform the potential victim that unauthorized access to their iCloud account has been detected.
That message or email has a link to which the password of the respective users of Apple ID can be changed and of course it is not true link, it will redirect the users to unknown website containing scams and surveys.
“Since this story broke, users have taken to various social networks and search engines to look for news about the stolen photographs. Knowing that people are searching for this content, it hasn’t taken long for scammers to try to take advantage of it,” Narang writes.
Malicious tweets have been observed, in one of the tweets some twitter user replied that TMZ had leaked more than 20 pics giving links that directs to spoofed site of TMZ which ask visitors to download and install AdobeVideo Players.
The piece of software was part of an affiliate marketing scheme that earns the scammer money for each installation of the product.