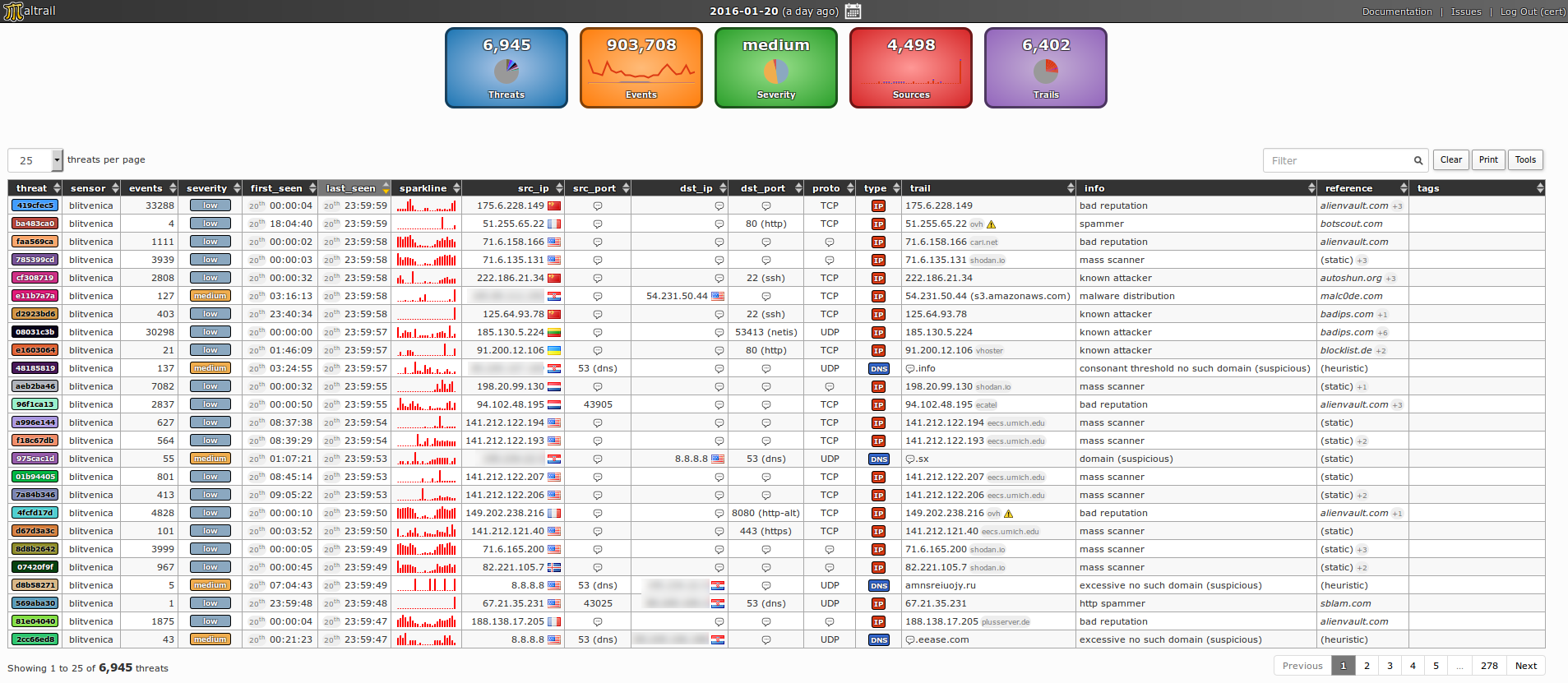
Maltrail is a malicious traffic detection system, using publicly available lists containing malicious and/or generally suspicious trails, along with static trails compiled from various AV reports and custom user defined lists, where trail can be anything from domain name , URL or IP address. Also, it has advanced heuristic mechanisms that can help in discovery of new malware.
How Maltrail works ?
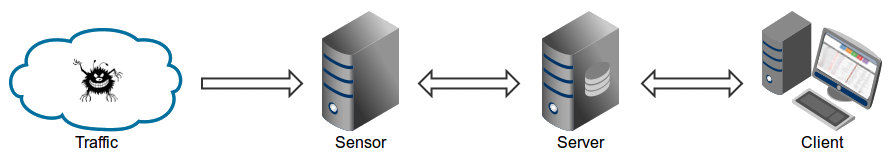
Maltrail is based on the Traffic > Sensor > Server > Client architecture.
Sensor is a standalone component that runs on the monitoring node or at the standalone machine where it “monitors” the passing Traffic for blacklisted items/trails (URLs or IPs).
In case of a positive match, it sends the event details to the main Server where they are being stored inside the appropriate logging directory. If Sensor is being run on the default machine as Server, logs are stored directly into the local logging directory. Otherwise, they are being sent via UDP messages to the remote server.
Server’s primary role is to store the event details and provide back-end support for the reporting web application. In default configuration, server and sensor will run on the same machine. So, to prevent potential disruptions in sensor activities, the front-end reporting part is based on the “Fat client” architecture.
Events for the chosen period are transferred to the Client, where the reporting web application is solely responsible for the presentation part. Data is sent toward the client in compressed chunks, where they are processed sequentially.
The final report is created in a highly condensed form, practically allowing presentation of virtually unlimited number of events.
Note: Server component can be skipped altogether, and just use the standalone Sensor. In such case, all events would be stored in the local logging directory, while the log entries could be examined either manually or by some CSV reading application.
Requirement:
- Python 2.6.x or 2.7.x
- pcapy (sudo apt-get install python-pcapy)
- Sensor component with the admin/root privileges.
Installation:
Enter the following commands
sudo apt-get install python-pcapygit clone https://github.com/stamparm/maltrail.gitcd maltrailsudo python sensor.py
Now to start the server on same machine, open a new terminal and type the following command
[[ -d maltrail ]] || git clone https://github.com/stamparm/maltrail.gitcd maltrailpython server.py
After starting the server now you have to test that everything is up
ping -c 1 136.161.101.53cat /var/log/maltrail/$(date +"%Y-%m-%d").log
Access the interface by visiting http://127.0.0.1:8338 from your web browser.
For more information about Maltrails you can visit GitHub for change of sensor configuration settings, server configuration settings and user guide.
Free Download: Maltrails (from GitHub)