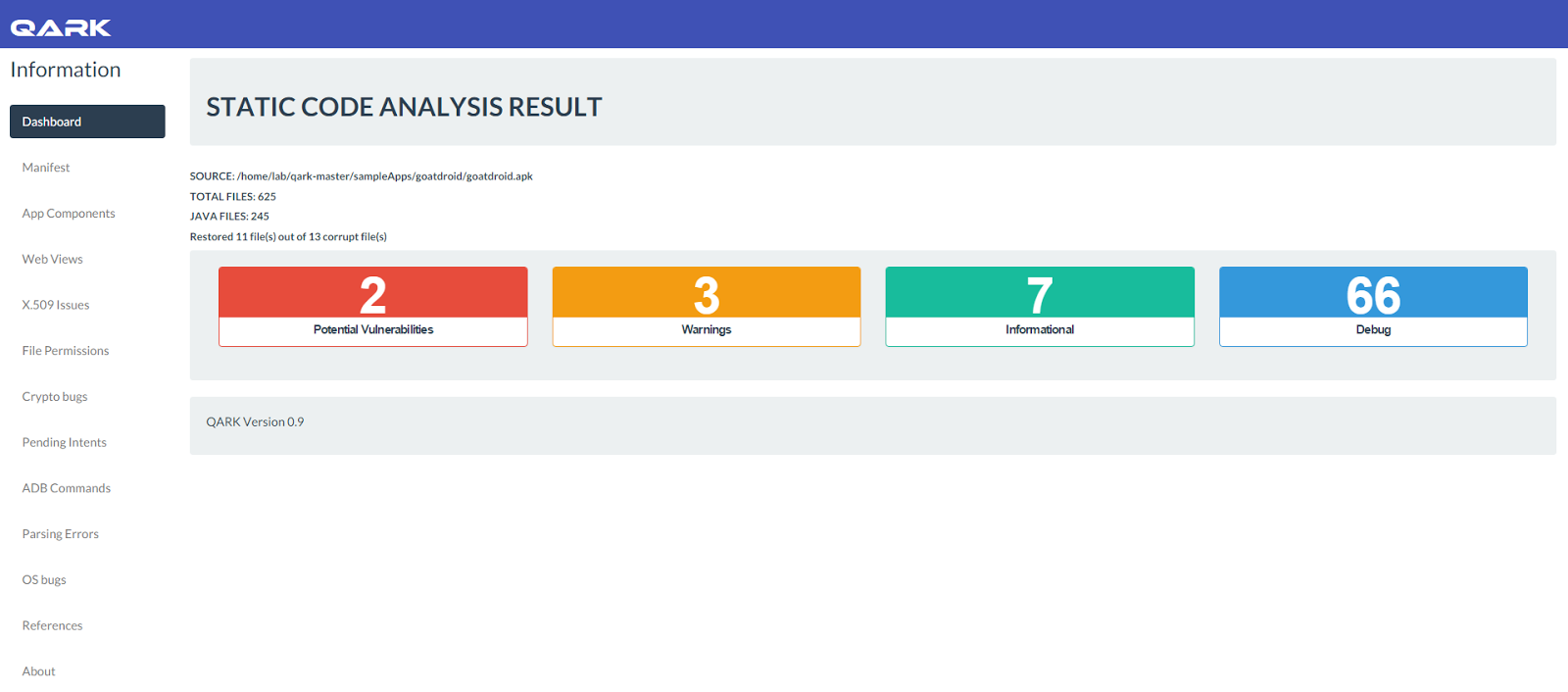
QARK also knows as Quick Android Review Kit used to scan several security related Android application vulnerabilities, either in source code or packaged APKs.
This tool can create “Proof-of-Concept” deployable APKs and ADB commands, capable of exploiting many of the vulnerabilities it finds.
You don’t need to root the test device, as this tool focuses on vulnerabilities that can be exploited under otherwise secure conditions.
Requirements:
- Python 2.7.6
- JRE 1.6+ (recommended 1.7+)
- OSX or Ubuntu Linux (others may or may not work)
How to use:
Download QARK and to run in interactive mode:
python qark.py
To run in headless mode:
python qark.py --source 1 --pathtoapk /Users/foo/qark/sampleApps/goatdroid/goatdroid.apk --exploit 1 --install 1
or
python qark.py --source 2 -c /Users/foo/qark/sampleApps/goatdroid/goatdroid --manifest /Users/foo/qark/sampleApps/goatdroid/goatdroid/AndroidManifest.xml --exploit 1 --install 1
The sampleApps folder contains sample APKs that you can test against QARK
Documentation:
QARK is an easy to use tool capable of finding common security vulnerabilities in Android applications and 100% free to use. QARK allows security reviewers to locate precise, in-depth explanations of the vulnerabilities. QARK automates the use of multiple de-compilers, leveraging their combined outputs, to produce superior results, when de-compiling APKs.
The major advantage QARK has over traditional tools, that just point you to possible vulnerabilities, is that it can produce ADB commands, or even fully functional APKs, that turn hypothetical vulnerabilities into working “POC” exploits.
Included in the types of security vulnerabilities this tool attempts to find are:
- Inadvertently exported components
- Improperly protected exported components
- Intents which are vulnerable to interception or eavesdropping
- Improper x.509 certificate validation
- Creation of world-readable or world-writeable files
- Activities which may leak data
- The use of Sticky Intents
- Insecurely created Pending Intents
- Sending of insecure Broadcast Intents
- Private keys embedded in the source
- Weak or improper cryptography use
- Potentially exploitable WebView configurations
- Exported Preference Activities
- Tapjacking
- Apps which enable backups
- Apps which are debuggable
- Apps supporting outdated API versions, with known vulnerabilities
Roadmap:
Things that will be added soon:
- Rewrite of code to support extensibility
- Bound Service vulnerability detection and exploitation
- Content Provider vulnerability detection and exploitation
- Additional WebView configuration demonstrations
- Static Tapjacking mitigation detection
- File browser capable of using root permissions
Note: QARK decompiles Android applications back to raw source code. Please do not use this tool if this may be considered illegal in your juristdiction. If you are unsure, seek legal counsel.
If you run into issues on OSX, especially relating to the outbound call to the Play Store, or the downloading of the SDK, it is likely due to your Python/OpenSSL configuration and the fact that recent changes in OSX impacted Python installed via brew. Nuking your Python installation(s) and re-installing from source may fix your issues.
For more information about QARK you can visit GitHub and download this tool from official page