A team from the University of California, Berkeley, and Georgetown University have developed the means to hijack your smartphone using hidden voice commands embedded within a YouTube video. This series of voice commands will make users vulnerable and can force unprotected Android or iOS smartphones to carry out malicious operations. It’s a pretty easy process to get hijacked, you need not do anything but just watch the YouTube video and you are in some serious threat.
How Does The Hidden Voice Command Works :
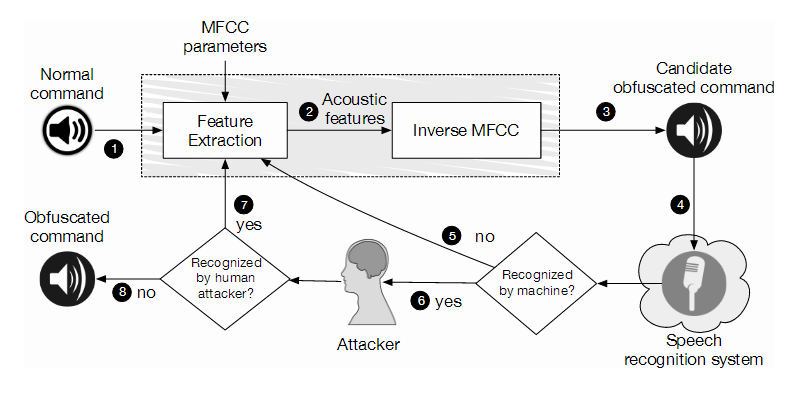
According to the researchers the hidden voice commands which are used to hijack devices are unintelligible to human listeners but which are interpreted as commands by devices. The signal is imperceptible to viewers, but is able to trigger commands within a nearby device, whether a laptop, computer, smart TV, smartphone or tablet. Once these commands are deciphered by the voice-based assistants such as Google’s Now voice assistant or Apple’s Siri personal assistant they get executed.
If the attack is successful then it allows the hackers to download and install malware to your device and also leading to device compromise, surveillance and several other issues caused by malicious code. Researchers have recorded a video of their attack, embedded below, which shows that some of the mangled voice commands are easy to pick up by a human paying enough attention, but some of the commands are not (the white-box model).
This isn’t new as these hijacking the devices using the voice commands have already done last year by two security researchers from French agency ANSSI used radio waves to send hidden commands to devices running Siri or Google Now. But the disadvantage of this attack was that it is only possible if the device had its headphones plugged in.