As the title itself states, nmap-xsl-bootstrap, a brand-new utility or, better to say an Nmap hack, that helps in beautifying the regular Nmap output which comes out of your Nmap scans. This output is often fairly unpleasing to the eye since it is difficult to be read if the infrastructure is so large. Furthermore these outputs can be sometimes nearly unmanageable through the command line which is why bootstrapping them can give them a better overall presentation that can be more soothing as well as useful for us. Besides you are likely to miss out less number of results due to these unwieldy scan reports, particularly if your scan target is huge.
For example, imagine, you have an assignment that targets an organization like Facebook which has hundreds of thousands of IP addresses and you need to scan each IP for the initial enumeration and recon activity, with your python script which makes use of the Nmap packages/modules in it. How easy could it be if you can just convert these reports into html format like this than the usual gibberish looking command line output or, using other old school formatting options?
TL;DR
This is a simple xml stylesheet which you can pass as a command line option to your Nmap scan command to format with Bootstrap, the Nmap scan report. Therefore this hack comes in handy for your recon activity and report making.
Objective
The most obvious objective we must have in mind before continuing further is that – Enumeration is the key aspect of system penetration testing. And the clearest way to have in mind before proceeding towards this goal of penetrating into a system, is to hone and sharpen your existing skills and most importantly the tools you already have before you start. As Abraham Lincoln said,
Give me six hours to chop down a tree and I will spend the first four sharpening the axe.
Ouch, but we definitely don’t have 6 whole hours for this sole task of sharpening our tools, how about a few minutes for it? Do you have 6 whole minutes to focus at this article, if yes then we can change the way you scan targets with Nmap and make reports that take you further towards rooting systems… That’s right, let’s learn how to format Nmap scan reports in a better manner so that it makes sense to us of what we had been doing all the while as well as make it easier for us to utilize the Nmap scan reports to the fullest!
This tool was also featured on HackTheBox video solution by ippsec on YouTube – Refer to ippsec’s solution of Poison box below for more relevant information regarding that.
Nmap-xsl-bootstrap at your rescue, to create visually stunning Nmap scan reports
This is basically an Nmap XSL implementation with Bootstrap, great isn’t it?
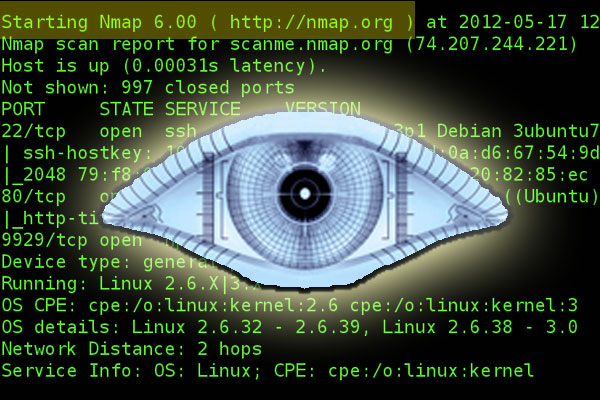
Check out these brilliant screenshots of it being in action –
Nmap-xsl-bootstrap in action
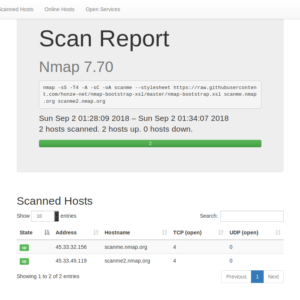
If you think it’s cool then it’s time to take a quick look at some other shots –

The above pic gives you a brief idea of online hosts that you just scanned for. It’s much better than the usual command line output, agree?
If still not, then here’s one more formatted output to please your senses –

And here I am, done with the visual testimonials that this minimal tool really helps you at enumeration. You have just seen how to sharpen Nmap so that it’s made the best use of in your future pen test assignments!
How to?
Git Repo –
https://github.com/honze-net/nmap-bootstrap-xsl
Using it is as simple as running this command inside your favorite terminal emulator, I use “GNOME” and tmux, both of which are excellent at their jobs! Comment me your favorite terminal emulator(s) which are particularly great at this task, if you know of some –
nmap -sS -T4 -A -sC -oA scanme --stylesheet https://raw.githubusercontent.com/honze-net/nmap-bootstrap-xsl/master/nmap-bootstrap.xsl scanme.nmap.org scanme2.nmap.org
Here’s a quick rundown of the recipe our command uses
Host/Your target IP – The above command scans the following hosts – scanme.nmap.org and scanme2.nmap.org.
Command line arguments and flags have their usual meanings, these are optimized to perform quick scans and bring out the best possible results. Do you have any Nmap hacks for better optimization for this enumeration process, leave them in comments.
We specify the filename “scanme” in the command for the generated file, passing it as a command line arguments.
Finally, last but not least, the Nmap-xsl-bootstrap comes in at less than a single line or, it’s not even a one liner, a piece of command line flag — stylesheet which specifies the style information associated with our generated Nmap xsl output that helps in shaping/formatting our Nmap scan report with the style information contained within it giving it a better visual appearance.
Result/Command output
You get a “scanme.xml” file which looks like this
What you get is an XML formatted file which can be further converted to html format with the help of this one liner/command –
xsltproc -o scanme.html nmap-bootstrap.xsl scanme.xml
Done!
Also, format old Nmap scan reports into this way –
Old scans
- You can also format old scans with the xsl stylesheet.
- Insert
<?xml-stylesheet href="https://raw.githubusercontent.com/honze-net/nmap-bootstrap-xsl/master/nmap-bootstrap.xsl" type="text/xsl"?>after<!DOCTYPE nmaprun>.
Looks like we are all caught up, but for a short and quick interview with the creator of this tool/implementation – Andreas Hontzia.
Let’s connect with the creator of this hack, to get the most out of this tool, and gain some tips and insights from him –
( The interview gist for transparency of interview)
Can you provide us some tips to use this nmap hack to achieve the best possible results?
You achieve the best results, by choosing the appropriate scanning options for Nmap. This is no trivial task, as numerous books, YouTube videos and articles show. If you ask Nmap the wrong question, it will answer it, but the result is not satisfying. For tiny scans, lets say one host and two ports, it might be a lot of overhead, because you can easily do this in the console. But if you want to document it well, then you should also save the scan as xml file. No need to add the Bootstrap XSL stylesheet while scanning. You can always add it later.
The Bootstrap XSL is best for scanning multiple hosts with multiple services. Some people already scanned a /16 DMZ (64K hosts) and got Megabytes of results. Some people do not like to read all this in a flat black and white terminal. With the Bootstrap XSL you can search, filter and sort your scan results. So for example if you are focusing on web applications, you can filter for http and sort by hostname. This makes later enumeration and documentation a lot easier and less prone to mistakes. And if you have to explain some scan results to people, who are not so familiar with a terminal, they will have a better experience, too.
What came as a motivation for the development of this minimal and great hack?
Thank you very much. I appreciate it!
Oh, this is a fun story. As always, somebody had a bad day (me) and goofed up the proper enumeration for a host and spent hours trying to find an initial attack vector for a lab machine, without success. Usually I work with a terminal and a browser side-by-side. The next day I read my scan result again, but in a maximized browser window, as I hadn’t opened my terminal, yet.
The scan results looked a bit different. Suddenly it had more text. Some text was cut off the view-port as I halved the browser window. After a few minutes I was finished with spotting all differences and there was my initial foothold. The missing piece of information I needed for a successful compromise was hidden, all day long. I sat back, sighed and thought 20 minutes about this lesson learned.
After a few minutes it was clear, that I had made a mistake. I ran a script scan with long output lines and tried to view it in a small browser window and I knew that sometimes the lines would be cut off. Not very smart. As I did not want to begin resizing the browser window during enumeration all the time, I looked for a solution to that problem. I knew that I could fix this with some simple CSS, but after a while I felt an itch: I wanted to redo the XSL in a framework, so that I had not to deal with CSS hacks in the future.
I took the original XSL file as a reference and tried to understand how it worked. Because Benjamin Erb (author of the first XSL file) did an awesome job by writing a well structured XSL, I could learn how all parts of it worked. After two evenings the prototype was finished. I polished it and uploaded it to GitHub. Wrote a tweet about it, which somehow exploded. I did not expect this. But I really want to thank all people out there for their great feedback. This is what fuels my motivation.
Can you tell us a bit more about yourself
Sure, my name is Andreas Hontzia. I am 35 years old and I live in Munich, Germany. I work as an IT Security Engineer in an industrial company. My first contact with hacking was over 20 years ago. So I made my hobby my job. I love to run Linux (mostly Kali and Arch, started with SuSE Linux in the late 90s). I hack for fun and profit. Occasionally I write a bit on Medium. Sometimes I give talks on information security events.
If you have any questions or just want to drop me a line, feel free to contact me.
Twitter: https://twitter.com/honze_net
Medium: https://medium.com/@honze_net
Xing: https://www.xing.com/profile/Andreas_Hontzia
Are you going to use this tool/hack in your next penetration testing assignment?
Let us know your thoughts on this article in comments below.