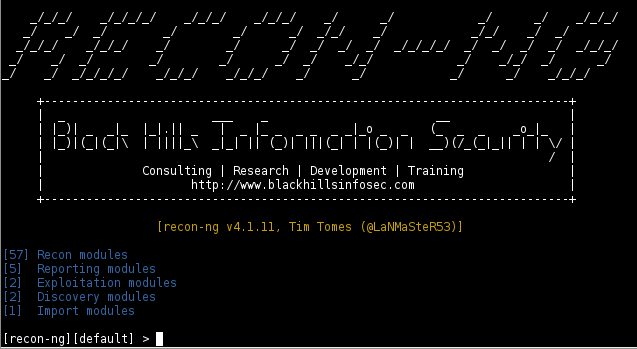
Recon-ng is a reconnaissance framework that can perform open source web based information gathering for a given target. Recon-ng is loaded with different type of modules, such as reconnaissance, reporting, import, discovery, and exploitation modules. The type of information that can be gathered with these modules include contacts, credentials, social media profiles, and handful of other information like IP, reverse IP, WHOIS information, and ports information. Recon-ng can also look for certain vulnerabilities in a target web application, such as cross site scripting, PunkSPIDER, and GHDB (Google Hacking Database).
Recon-ng Installation
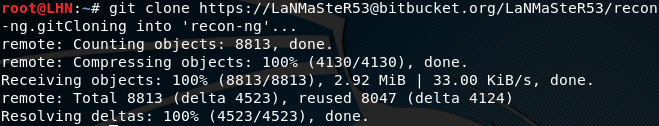
To install Recon-ng, first clone the framework using the following command.
git clone https://[email protected]/LaNMaSteR53/recon-ng.git
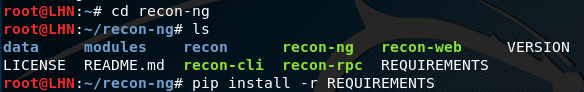
In the next step, move to the Recon-ng directory and run the REQUIRMENTS file.
cd recon-ng pip install -r REQUIREMENTS
How Recon-ng Works
Recon-ng can be set into action using the following command.
./recon-ng
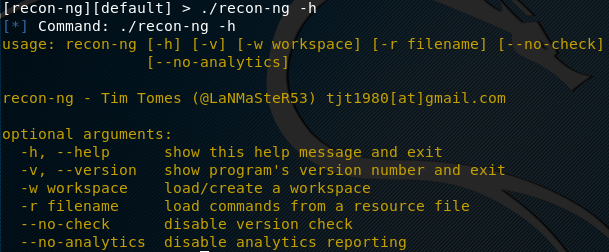
The help menu can be explored as follows.
./recon-ng –h
In order to explore the modules, run the following command. The command displays all the modules along with the path required to run each module.
show modules
In order to use any module, just type the following command.
use <module path>
Similarly, to set the target domain, use the following syntax.
set source <target domain> run
For example, if we want to run the XSSED vulnerabilities test module, we can do so in the following manner.
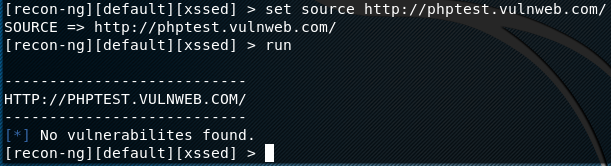
use recon/domains-vulnerabilities/xssed set source http://phptest.vulnweb.com run
The tool runs the defined module and displays the results on the screen as shown below.
We can try other modules using the same approach. There are certain modules like Shodan, Facebook, twitter, Instagram etc that require API keys to fetch results. The API key for such modules can be added using the following command.
keys add <module_api> <api key here>
For example, we have Shodan api key as SH1254AKD. We can add this API key as follows.
keys add shodan_api SH1254AKD
In order to see the configured keys in Recon-ng, use the following command.
keys list
What Bunny rating does it get?
Recon-ng is a modular framework that can gather detailed information about target web applications and individuals, it is n amazing tool for the OSINT part of a red team engagement!. As a result we will be awarding this tool an amazing rating of 4.5 out of 5 bunnies!.




![]()
Want to learn more about ethical hacking?
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.