Tulpar is an open source penetration testing tool that can find web application vulnerabilities such as SQL injection, Cross-site Scripting (XSS), Command injection, Directory traversal, E-mail disclosure, Credit card disclosure, and File inclusion attacks. Apart from these vulnerabilities assessments, Tulpar can do the following tests.
- Web crawling
- Whois information
- Server information
- Certification information
- Technology information
- Port scanner
- Cyber Threat Intelligence
- IP2Location
- X-Content-Type check
- X-XSS Protection check
- File input available check
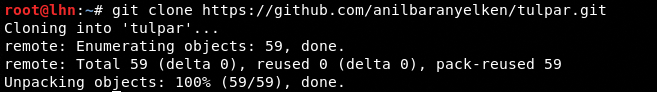
Tulpar Installation
Tulpar is a Python tool that can be cloned from Github using the following repo path.
git clone https://github.com/anilbaranyelken/tulpar.git
The tool depends on python-whois, futures, requests, and lxml packages. To install these dependencies, navigate to the tool’s directory and run the requirements file as shown below.
cd tulpar pip install -r requirements

Tulpar Working
Running Tulpar requires the execution of following command in the terminal.
python tulpar.py <action> <target web url>
The <action> argument in the above command is the desired scanner function, such as all, sql, xss, portscanner, and fuzzing. The following screenshot shows the complete list of scanner functions that can be set in the <action> field.
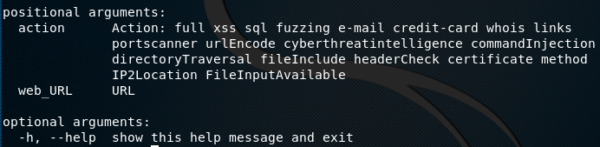
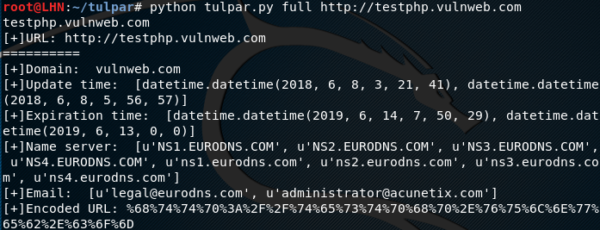
We can use the all argument to scan everything supported by the tool.
python tulpar.py all testphp.vulnweb.com
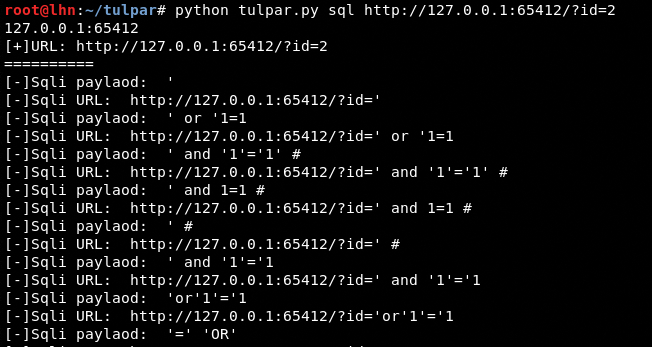
We can use Tulpar tool to scan specific vulnerability, such as SQL, in the following manner.
python tulpar.py sql http://testphp.vulnweb.com/listproducts.php?cat=1
If the target web application is vulnerable to SQL injection, the tool shows a number of payloads that can be successfully injected to find out the database errors in the target web application.
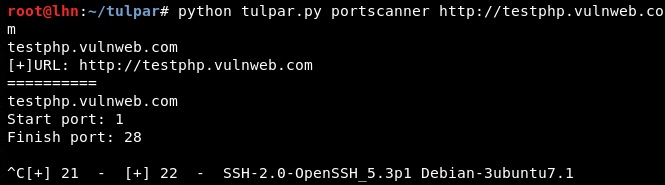
Similarly, we can use Tulpar tool for other aforementioned information gathering purposes. For instance, we can use Tulpar tool as follows to scan the live ports in the target web applications.
python tulpar.py portscanner testphp.vulnweb.com
What Bunny rating does it get?
Tulpar is an open source web application scanner that can help in information gathering and vulnerabilities assessment tasks. The tool, however, slows down while performing some of the scanning tasks, therefore we are giving it 4 out of 5 bunnies.




Want to learn more about ethical hacking?
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.

