Today, we are going to talk about a powerful web application scanner named WAScan.
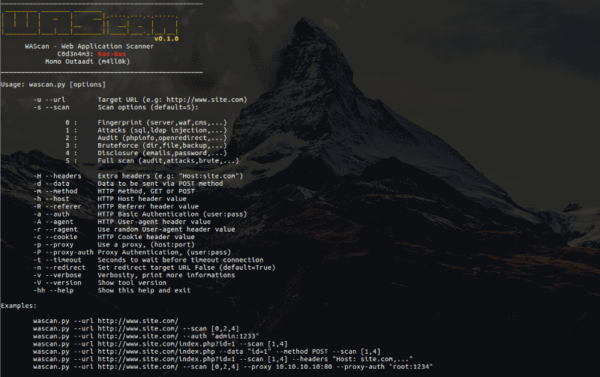
WAScan stands for Web Application Scanner, it also completely open source. The purpose of the tool is to gather information and find various vulnerabilities assuming a”black-box” model. WAScan is built on Python 2.7 and can run on any platform which has a Python environment.
The features of WAScan allows it to fingerprint, audit, bruteforce and disclose sensitive information of a web application.
Let’s Get started
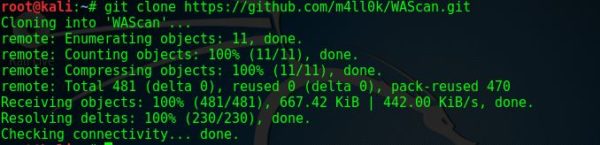
First, we need to clone the application using the following command:
git clone https://github.com/m4ll0k/WAScan
After a successful clone, your screen should look like that:
Then we change directory to WAScan by typing the following:
cd WAScan
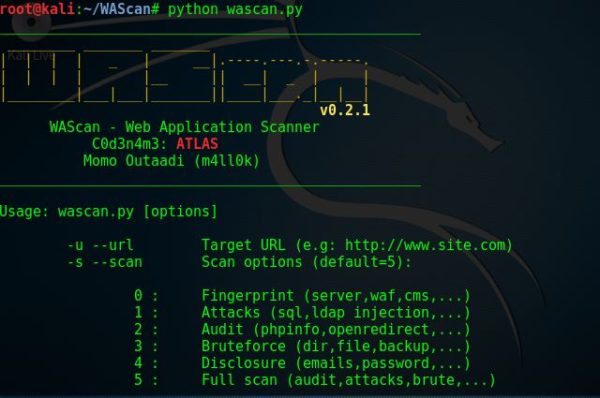
Then we run the tool using the following command:
python wascan.py
Then the application will display its help menu. Your screen should look like the below screenshot:
Then, if you want to perform specific attacks, you should then type the desired command within the relevant parameters.
The tool provides guides on what commands to use along with its parameters..
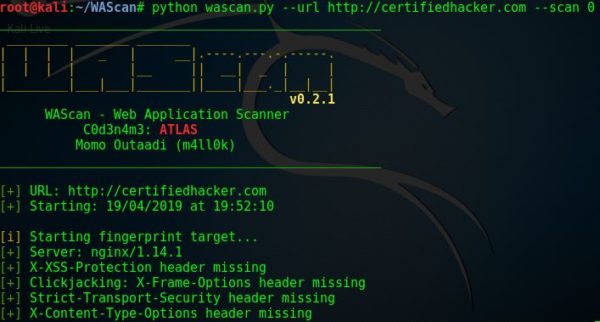
So we type the following command:
python wascan.py --url http://example.com --scan 0
The 0 parameter is used to fingerprint a server.
So the tool should gather information about the web application, and should return a result like that:
This tool is cool. Let’s run another test 🙂 , using the following command:
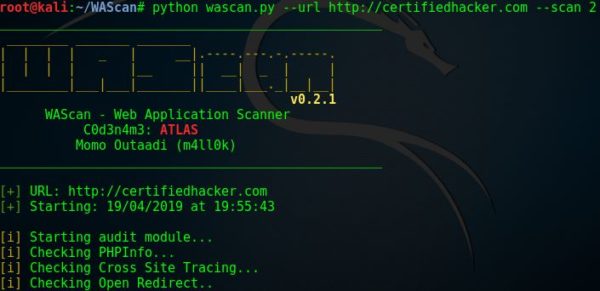
python wascan.py --url http://example.com --scan 2
The 2 parameter is used to perform an audit against the web application. The tools will be auditing the web application against phpinfo, openredirect etc…
We run the command, and your screen should look like that:
The tool also supports other types of tests when typing any of the following command:
python wascan.py --url http://xxxxx.com/test.php --scan 5 --auth "admin:1234" python wascan.py --url http://xxxxx.com/test.php --scan 5 --data "id=1" --method POST python wascan.py --url http://xxxxx.com/test.php --scan 5 --auth "admin:1234" --proxy xxx.xxx.xxx.xxx python wascan.py --url http://xxxxx.com/test.php --scan 5 --auth "admin:1234" --proxy xxx.xxx.xxx.xxx --proxy-auth "root:4321" python wascan.py --url http://xxxxx.com/test.php --scan 5 --auth "admin:1234" --proxy xxx.xxx.xxx.xxx --proxy-auth "root:4321 --ragent -v
You can try these commands and explore the different features of the application on your own.
What Bunny Rating Does it Get
This tool has different useful features. As a penetration tester, you can gather information, check for common vulnerabilities as well as perform different attacks against the web application. You can do all this using one tool. This tool has features that other tools don’t. Moreover, the tools has an easy to us guide. The instructions on how a penetration tester can use the tool are clear, however sometimes the tool can be absent in providing verbose notifications, I will be awarding this tool 3.5 out of 5 bunnies.



![]()
Want to learn more about ethical hacking?
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.