Spiderfoot is an open-source tool used for reconnaissance. It is capable of gathering open-source information which can be further used for investigations and red teaming exercises.
Spiderfoot has a multitude of scanning options and modules available, it utilizes more than 100 OSINT data sources to collect information automatically. It can capture information like domains, IP addresses, emails, DNS record, contacts, integrated technologies, entities, networks, and more.
Downloading and Installing Spiderfoot
It can be downloaded in Kali Linux using the following command:
git clone https://github.com/smicallef/spiderfoot.git

python -m pip install requirements.txt

Running Spiderfoot
We will start the Spiderfoot GUI for starting its web server;
python sf.py
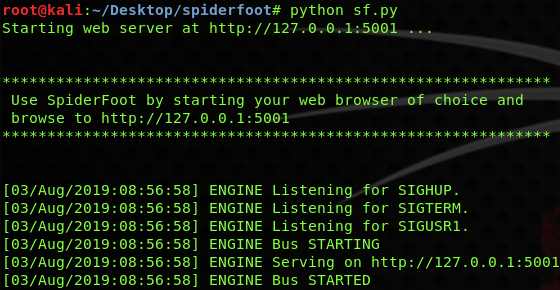
When the webserver gets started, open your preferred browser and go to the http://localhost:5001. It will open the Spiderfoot dashboard as shown in the below screenshot;

Now go to the New Scan tab and enter the scan you wish to utilise, then enter your preferred domain name or IP address you want to enumerate and click Run Scan.

Once the scan gets started, you ca view the results in GUI with a chart;

The data can be viewed logically too;

And also with a graph;

What Bunny rating does it get?
Spiderfoot is a sharp and handy penetration testing tool that can help in providing a great picture of a target within your red teaming scope. It is loaded with several modules, configuration, and OSINT sources to assist in the information gathering process, which gives an in-depth result within a GUI format. I am giving it 4.5 out of 5 bunnies.




![]()
Want to learn more about ethical hacking?
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.
