Researchers have discovered more malicious Android apps on the Play Store. They specifically noticed numerous adware-delivering Android games and camera apps that evaded Play Protect.
More Adware-Delivering Android Apps Found
Researchers from Trend Micro have reported multiple malicious apps targeting Android users with malware. Reportedly, they discovered 49 different adware-delivering Android games and camera apps with over 3 million downloads. These apps not only infected users but also utilised various security evasion features to bypass Play Protect.
As elaborated in their blog post, the apps, after installation, delivered full-screen ads on the devices. The ads provided no viable option to the users to close, compelling them to press back or home key.
Moreover, those apps also disguised their icons to bluff the users. The following image lists all 49 adware-delivering apps.
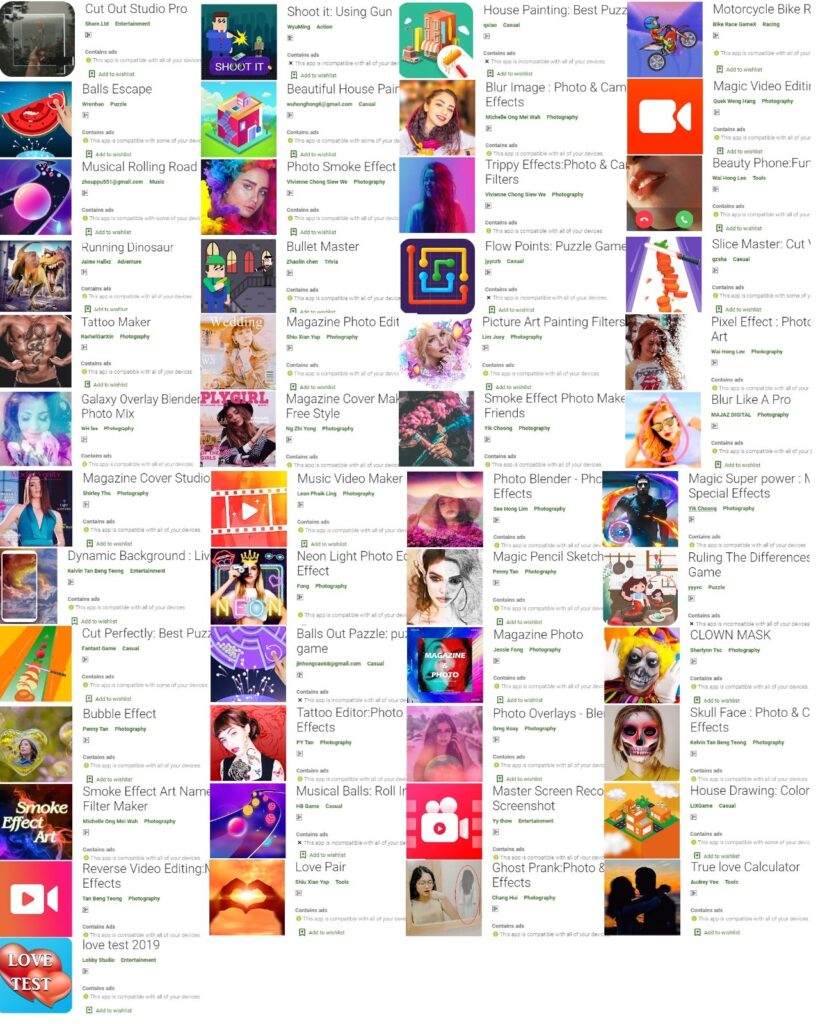
Source: Trend Micro
In addition, the apps also applied various behaviors to evade Google’s app vetting, including,
- Heavy code obfuscation
- Strings encryption with a custom algorithm
- Adware shortcut disguised as a popular browser
- Different actions based on Android versions
- Registration as a foreground service to continue running with no user interaction
- Prolonged delay time
Google Removed The Nasty Apps
Following Trend Micro’s report, Google removed all the apps from the Play Store.
Nonetheless, the threat is not over. In fact, it seems an ongoing battle between Play Store and malicious app developers considering the wave of adware-delivering apps.
Until now, hundreds of Android applications made it to the Play Store, targeted users with malware, and eventually got removed. Nonetheless, removing these apps does not effectively end this malicious campaign. The developers are smart enough to employ various tricks to evade Google’s app vetting processes.
Let us know your thoughts in the comments.

