The issue was discovered in mid-March. OrbitScripts LLC fixed the vulnerability shortly after being notified. The security hole has been addressed with the release of Orbit Open Ad Server 1.1.1.
Version 1.1.0 and probably prior variants are impacted, which is why users are advised to update their installations as soon as possible.
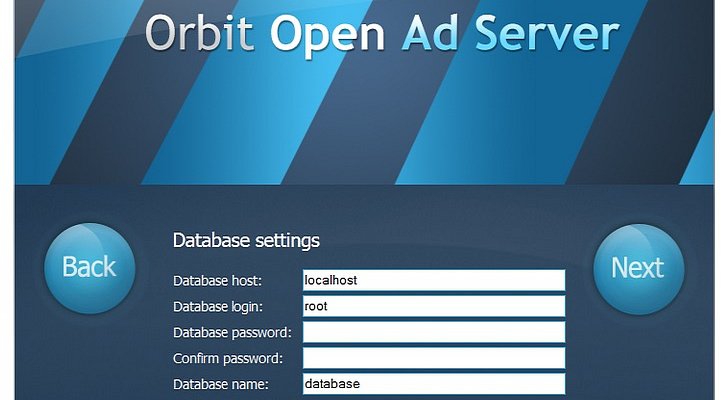
According to the advisory published by High-Tech Bridge on Wednesday, the flaw (CVE-2014-2540) can be exploited to launch SQL Injection attacks, alter SQL requests to the databases, and possibly even to gain control of impacted sites.
“This is definitely a high-risk vulnerability,” said Ilia Kolochenko, CEO of High-Tech Bridge.
“It’s a blind SQL injection so its exploitation will require some skills from a hacker,” he added. “But nothing really complicated for an experienced hacker.”
Proof of concept attacks against the vulnerability can be seen here.
The security company’s CEO Ilia Kolochenko has told SecurityWeek that the vulnerability is “high risk.” While it might be a bit tricky to exploit, due to the fact that it’s a blind SQL Injection, the vulnerability can be leveraged by experienced hackers.
While OrbitScripts has fixed the security hole, there could be a lot of third-party services that use vulnerable versions of the application to manage ads. Cybercriminals can leverage these websites for malvertising attacks.
While there’s no evidence that the flaw has been exploited in the wild, it could have been.
“As cybercriminals are increasing targeting the ad servicing ecosystem with increased precision and distribution of malvertising, it underscores the need for all stakeholders to work to secure their servers and operations,” said Craig Spiezle, executive director and president of the Online Trust Alliance. “Malvertising is a significant risk to the industry, publishers and most importantly consumers who are being unknowingly comprised when visiting legitimate web sites.”