Webvulnscan is a web application scanner that automates vulnerability assessment tasks. The tool can automatically detect different web application vulnerabilities including Cross Site Scripting (XSS), Click-jacking, Breach, Cross Site Request Forgery (CSRF), and cacheable cookies. Apart from vulnerabilities assessment, Webvulnscan can be used for other web related tasks, such as links crawling, form crawling, white- and black-listing of specific web links, and web pages authentication tasks.
How to Install Webvulnscan
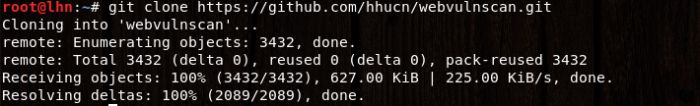
Webvulnscan is a Python tool that can be cloned from Github using the following github path.
git clone https://github.com/hhucn/webvulnscan.git
The tool does not require any installation and can be run directly from the source code.
How to Use Webvulnscan
Webvulncan can be run from the source code using the following commands.
cd webvulnscan python –m webvulnscan <option> <target web application>
In the above command, the <option> field requires an action to be defined for the target web application. The action can be scanning process or it can be other tasks like blacklisting or whitelisting web pages.
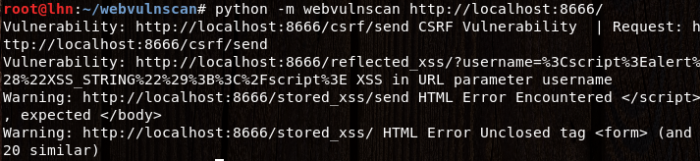
Webvulnscan can automatically assess all the aforementioned vulnerabilities on a test web application (localhost:8666) using the following command.
python -m webvulnscan http://localhost:8666/
The results (detected vulnerabilities) are presented in the following format.
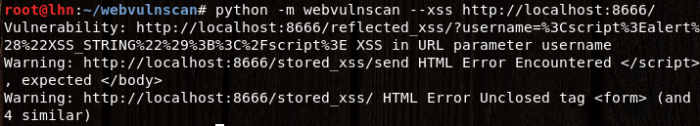
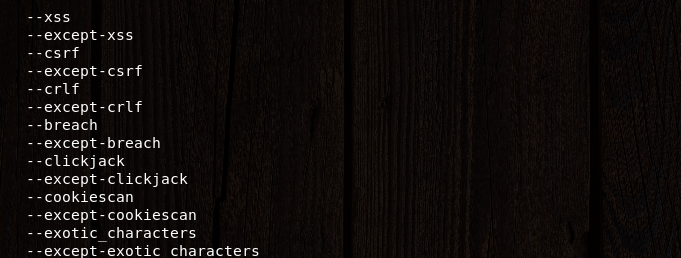
We can direct Webvulnscan to include or omit certain vulnerabilities tests from the scanning process. For instance, we can direct Webvulnscan to only look for XSS vulnerabilities in the target web application using the following command.
python -m webvulnscan --xss http://localhost:8666/
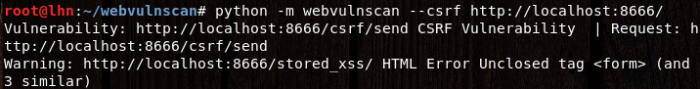
Similarly, we can scan CSRF vulnerabilities using the following command.
python -m webvulnscan --csrf http://localhost:8666/
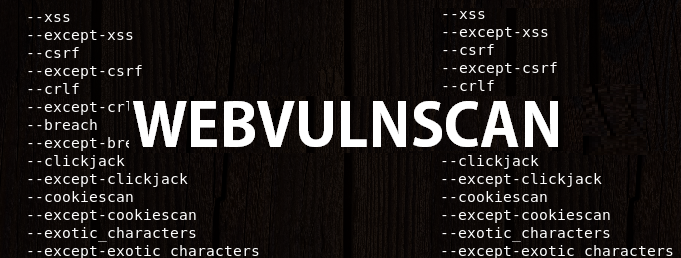
The following screenshot shows the complete list of attack options that can be included or excluded from the scanning process.
To whitelist or black list target web pages, simply use the –whitelist and –blacklist parameters in the following format.
python -m webvulnscan –whitelist <target web page link/s>python -m webvulnscan –blacklist <target web page link/s>
What Bunny rating does it get?
Webvulnscan can automatically detect certain web application vulnerabilities including XSS, CSRF, Clickjacking, and cached cookies. The tool, however, takes longer to scan large websites for said vulnerabilities.. I’m giving it 3 out of 5 bunnies.



Want to learn more about ethical hacking?
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.